A newly identified Android spyware app is elevating its tactics to remain hidden and unremovable by leveraging a password prompt for uninstallation.
This unsettling feature effectively blocks users from removing the app unless the correct password—set by the person who installed the spyware—is entered.
How the Spyware Works
The spyware, which TechCrunch decided not to name to avoid promoting it, takes advantage of Android’s built-in “overlay” permission.

This feature allows apps to display content over other applications, and in this instance, the spyware uses it to hijack the uninstall screen.
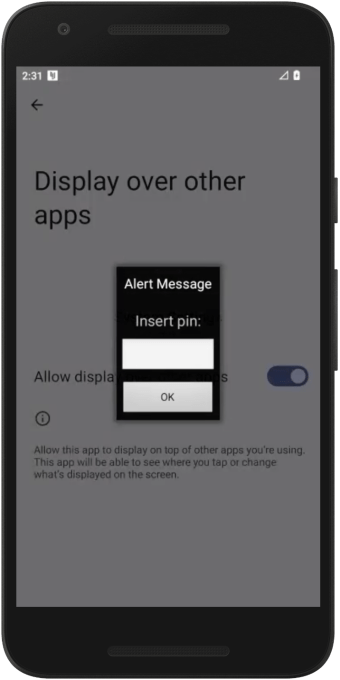
Whenever the victim tries to deactivate or uninstall the app, a password prompt is triggered, shutting down any removal attempts if the wrong password is entered.
The app, often disguised under a generic name like “System Settings” with an Android-default icon, hides its presence from the home screen while continuously feeding private user data—messages, photos, and even real-time locations—to an online dashboard accessible to the perpetrator.
Growing Threat of “Stalkerware”
This spyware belongs to the increasingly concerning category of consumer-grade surveillance software, commonly referred to as “stalkerware” or “spouseware.”
While marketed for legitimate uses like monitoring children or employees, these apps are frequently abused to spy on partners or individuals without consent—a practice that is both invasive and illegal.
These apps are typically downloaded from unofficial sources and require physical access to the victim’s phone along with knowledge of their passcode.
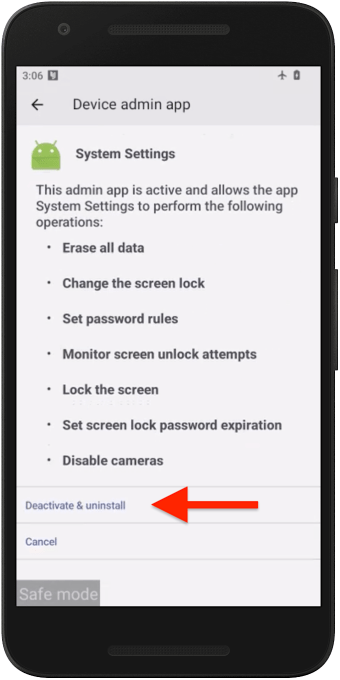
Once installed, they can exploit advanced Android features, such as “device admin” privileges, to maintain control and prevent removal.
Removing the Spyware
Here’s how to proceed:
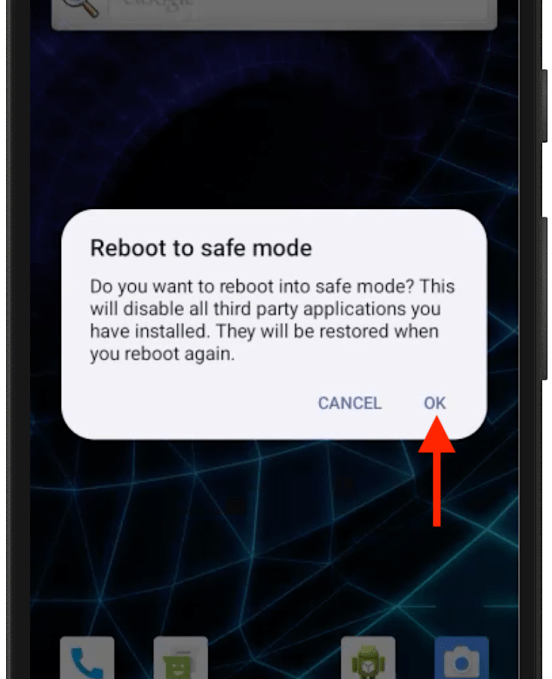
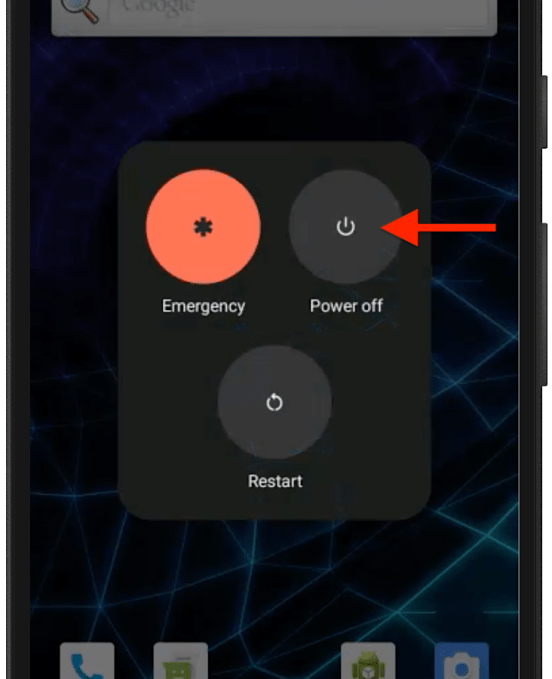
- Reboot to Safe Mode: Hold down the power button, then press and hold the “Power Off” option. Confirm the “Reboot to Safe Mode” prompt.
- Identify Suspicious Apps: In safe mode, check the “Device Admin” apps in the settings. Disable any unrecognized apps.
- Uninstall the Spyware: Locate the spyware in “Apps” settings and select “Uninstall.” Confirm the action.
Once the app is removed, restart the phone to exit safe mode and secure your device with a stronger passcode to prevent future unauthorized access.
Users must remain vigilant against such threats. To protect your device, avoid downloading apps from untrusted sources and monitor app permissions closely.
If you suspect spyware, consult specialized guides and consider reporting the incident to authorities if malicious intent is evident.
This alarming development underscores the escalating sophistication of spyware apps. It is a stark reminder for Android users to stay informed and proactive about securing their devices and data.
Find this News Interesting! Follow us on Google News, LinkedIn, & X to Get Instant Updates!



.png
)
