In a recent announcement, the team behind the widely acclaimed source code editor, Notepad++, has issued a call to arms for its user community.
The appeal comes in response to the emergence of a deceptive website that misleads users and poses significant security risks.
Here’s a closer look at the situation and how you can help.
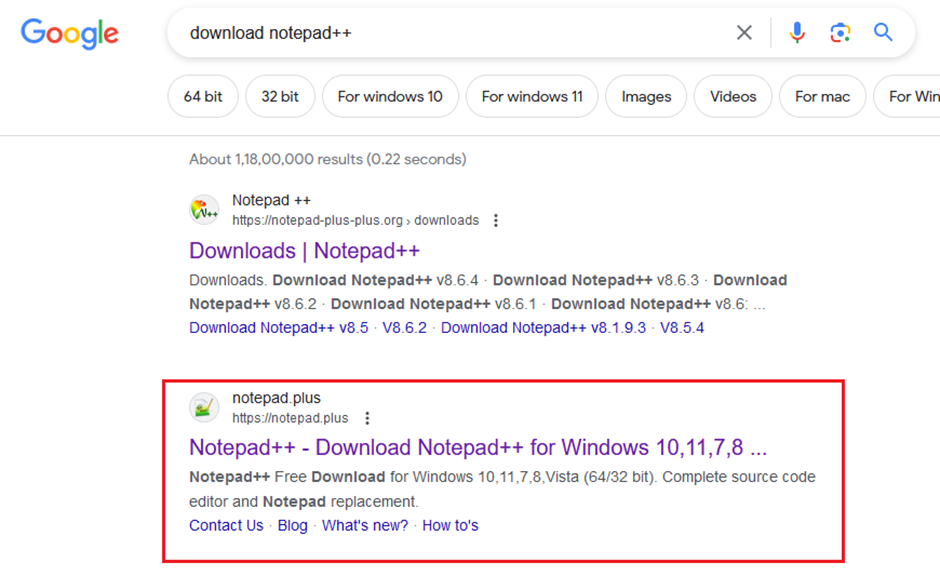
The website [https://notepad.plus/] has been masquerading as an official source for downloading Notepad++.
This has led to confusion among users, some of whom have been tricked into believing it is the legitimate site for the popular code editor.
AI-Powered Protection for Business Email Security
Trustifi’s Advanced threat protection prevents the widest spectrum of sophisticated attacks before they reach a user’s mailbox. Try Trustifi Free Threat Scan with Sophisticated AI-Powered Email Protection .
The creators of Notepad++ have received numerous complaints through emails, social media, and forums, highlighting this imposter site’s frustration and potential dangers.!
Hidden Dangers Lurking Behind Every Click
Despite its claims of being an “unofficial fan website created for general information/educational purposes only,” the site harbors malicious intentions.
It is littered with misleading advertisements that aim to profit from unsuspecting visitors and pose serious security risks.
These ads are designed to trick users into clicking on them, thereby compromising their online safety.
The Real Victim: Notepad++ and Its Community
The existence of [https://notepad.plus/] does more than mislead users; it actively diverts traffic away from the legitimate Notepad++ website, notepad-plus-plus.org.
This undermines the integrity of the Notepad++ community and threatens user safety by exposing them to potential security threats.
The Notepad++ team is urging its community to take action against this parasitic website.
By reporting the site as harmful, you can play a crucial role in protecting not only the Notepad++ community but also the broader internet ecosystem.
Your vigilance and prompt action can help maintain a safe and secure online environment for all users.!
The call to action from the Notepad++ team is a reminder of the power of community.
In the face of deceptive practices and online threats, standing together can make a significant difference.
By reporting the malicious website, you contribute to a safer internet, ensuring that the integrity and security of the Notepad++ community remain intact.
Secure your emails in a heartbeat! Take Trustifi's free 30-second assessment and get matched with your ideal email security vendor - Try Here
.webp?w=696&resize=696,0&ssl=1)


.png
)
