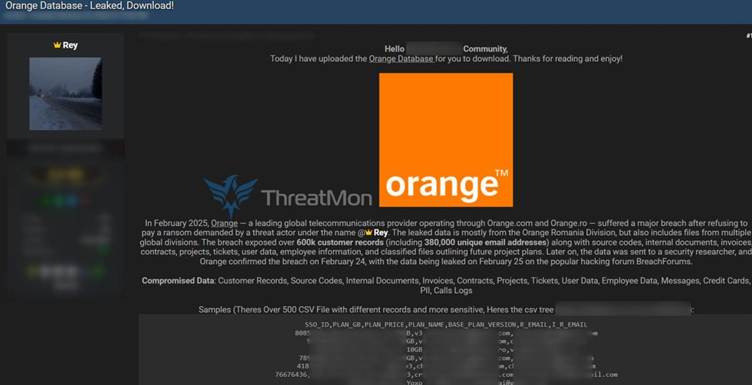
Telecommunications provider Orange Communication faces a potential data breach after a threat actor using the pseudonym “Rey” claimed responsibility for leaking 380,000 email records and sensitive corporate data on a dark web forum.
The alleged breach, disclosed earlier this week, includes source code, internal invoices, client contracts, project blueprints, and user data, raising concerns about operational security and customer privacy.
Scope of the Breach
According to forum posts reviewed by cybersecurity researchers, the leaked data spans multiple categories critical to Orange’s operations.
Forum posts reviewed by cybersecurity researchers
Source code repositories for customer management systems and network infrastructure tools were reportedly exposed, potentially compromising proprietary technology.
Financial documents, such as invoices and service agreements with enterprise clients, were also included in the dump, which could reveal contractual terms and pricing structures.
Most notably, the threat actor asserted that 380,000 email addresses linked to Orange’s consumer and business accounts were extracted, though password hashes or payment details were not explicitly mentioned.
Rey, the alleged hacker, did not specify motives but hinted at “leveling the playing field” in a forum statement, suggesting ideological or retaliatory intentions.
Cybersecurity analysts hypothesize the breach resulted from a combination of phishing attacks and exploitation of unpatched vulnerabilities in Orange’s cloud storage systems.
The leak followed a months-long absence of major security updates to the company’s employee authentication portals, according to independent audits.
Orange’s Response and Investigation
Orange Communication issued a brief statement acknowledging “irregularities in its data logs” but stopped short of confirming the breach.
The company emphasized that its core networks remain secure and urged customers to enable two-factor authentication as a precaution.
A spokesperson confirmed collaboration with INTERPOL’s Cybercrime Directorate and third-party forensic experts to assess the claims.
Cybersecurity experts warn that exposed email addresses could fuel targeted phishing campaigns or credential-stuffing attacks across other platforms.
Individuals and businesses tied to the leaked contracts may also face reputational harm or competitive disadvantages if sensitive terms were disclosed.
Collect Threat Intelligence on the Latest Malware and Phishing Attacks with ANY.RUN TI Lookup -> Try for free



