Researchers observed a new wave of PHP-based Web Skimmer by Magecart group 12 threat actors to steal card details from Magento 1 websites.
Magento eCommerce platform is written by PHP, and acquired by Adobe. also frequently targeted by the threat actors specifically from the Magecart group, who have very active to attack vulnerable e-commerce platforms.
Magecart group is well known for continuously distributing new malware to attack online shopping websites by injecting a skimmer in the payment page to steal credit/debit card data.
Attackers using webshell that allow an attacker to maintain remote access by exploiting the vulnerability on the eCommerce websites.
Currently observed campaign known as Smilodon or Megalodon was developed by this Magecart group to infect online stores by loading JavaScript skimming code via server-side requests dynamically.
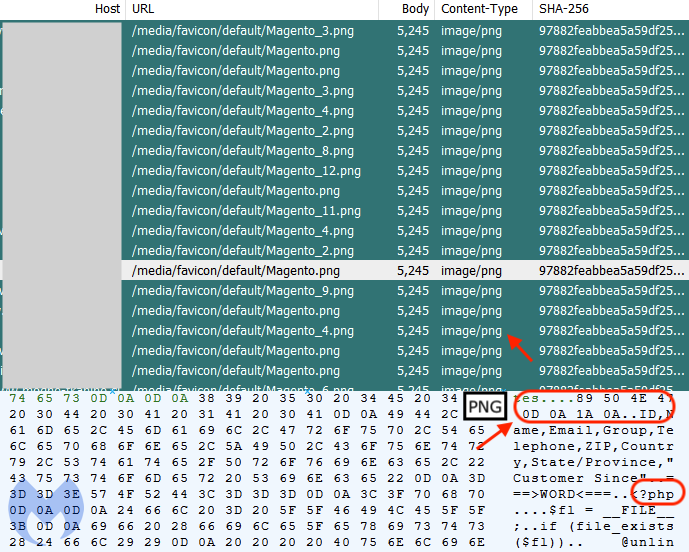
During the research, Malwarebytes researchers observed a new piece of file mimics as favicon with the name of Magento.png, and attempt to run as ‘image/png’ but the format was looks suspicious.
PHP-based Skimmer Infection Process
Magecart group initiate this attack using a PHP-based web shell into the compromised site by replacing the legitimate shortcut icon tags with a path to the fake PNG file.

When dig into deep, researchers found the m1_2021_force directory reveals additional code very specific to credit card skimming.
researchers also found that the control servers are connected with the new domains (zolo[.]pw) happens to be hosted on the same IP address (217.12.204[.]185) as recaptcha-in[.]pw and google-statik[.]pw, domains.
What is a Dynamically loading Skimmer?
Dynamically loading skimmer is an approach used by the threat actors to inject the skimmer into the compromised website from the server-side instead of the client-side and, this approach helps attackers form being blocklisted, so consider it as more effective.
According to the researchers, In comparison, the skimmer we showed in this blog dynamically injects code into the merchant site.
“We continue to track this campaign and other activities from Magecart Group 12. Online merchants need to ensure their stores are up-to-date and hardened” Malwarebytes said.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and hacking news updates.



.png
)
