D-link DNS-320 Devices have used as an ideal backup solution, it offers an effective way to share documents, music, videos, and photos with anyone that connected in your network.
CyStack security researcher, Trung Nguyen, detected a remote code execution vulnerability in DNS-320 sharecenter devices that let the user’ s data vulnerable to remote hackers. The vulnerability can be tracked as CVE-2019-16057.
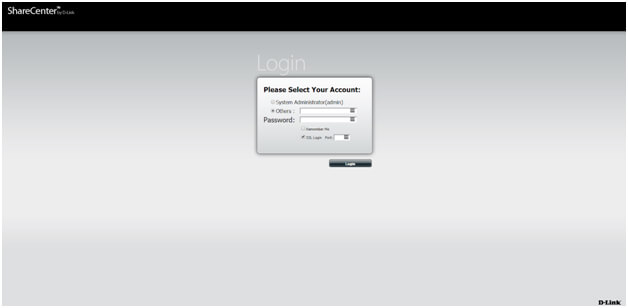
Unauthenticated RCE – DNS-320 Sharecenter Devices
The vulnerability resides in the login module of DNS-320 devices, by exploiting this vulnerability attackers could gain access to the devices remotely and control devices by executing arbitrary code.
According to CyStack report shared with GBHackers On Security, the critical vulnerability in the device allows an unauthenticated attacker to “access to all application commands with root permission”.
The vulnerability rated as critical receives CVSSv2 base score 10.0, and it affects DNS-320 sharecenter Devices with version equals 2.05.B10 or lower.
According to Trung, by targeting binary /cgi/login_mgr.cgi which handles login requests, attackers may poison the parameter port and perform an RCE attack.

“Let’s take a look at sub_9924(). We can see that if an attacker controls parameter v1 which stands for the port, he will be able to arbitrarily execute commands, which is the key point in this vulnerability.” He explained
The vulnerability was reported to D-link by CyStack security team, but it was unknowingly patched in April 2019 release. D-link also published a report.
D-link DNS-320’s users are urged to update their devices’ firmware to the latest version.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity news updates



.png
)
