A critical vulnerability has been identified in the xz-utils package, versions 5.6.0 to 5.6.1, which harbors a backdoor capable of compromising system security.
This vulnerability, cataloged under CVE-2024-3094, poses a significant threat to the Linux ecosystem, including the widely used Kali Linux distribution, known for its robust security and penetration testing tools suite.
The Vulnerability: CVE-2024-3094
The backdoor discovered in the specified versions of xz-utils could allow an attacker to bypass sshd authentication, thereby gaining unauthorized remote access to the affected system.
AI-Powered Protection for Business Email Security
Trustifi’s Advanced threat protection prevents the widest spectrum of sophisticated attacks before they reach a user’s mailbox. Try Trustifi Free Threat Scan with Sophisticated AI-Powered Email Protection .
Given the ubiquity of xz-utils across various Linux distributions, the potential for widespread compromise was alarmingly high.
Fortunately, the issue was identified and addressed swiftly, mitigating the potential damage.
The vulnerability has been patched in Debian, from which Kali Linux derives much of its software base, thereby rectifying the issue for Kali users.
Impact on Kali Linux
For Kali Linux users, the vulnerability window was narrow but critical. The affected xz-utils version, 5.6.0-0.2, was available in the Kali repositories from March 26th to March 29th.
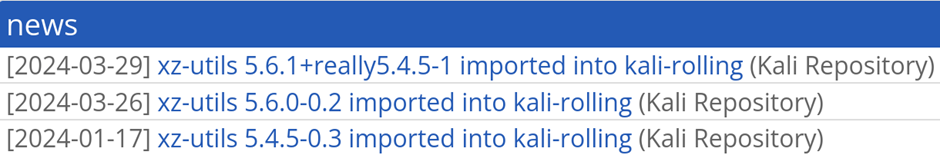
Users who updated their Kali Linux installations within this timeframe are at risk and must take immediate action to secure their systems.
If your Kali Linux system was not updated during this period, you are not at risk from this specific vulnerability.
However, staying informed and vigilant about system updates is always advisable to maintain security.
How to Check for Infection and Update
To determine if your Kali Linux system is affected, you can execute the following command in the terminal:
kali@kali:~$ apt-cache policy liblzma5
liblzma5:
Installed: 5.4.5-0.3
Candidate: 5.6.1+really5.4.5-1
Version table:
5.6.1+really5.4.5-1 500
500 http://kali.download/kali kali-rolling/main amd64 Packages
*** 5.4.5-0.3 100
100 /var/lib/dpkg/status
If the output indicates the installed version as 5.6.0-0.2, your system is vulnerable, and you must upgrade to the latest version, 5.6.1+really5.4.5-1. This can be achieved with the following commands:
kali@kali:~$ sudo apt update && sudo apt install -y --only-upgrade liblzma5
...
kali@kali:~$For those seeking more detailed information on this vulnerability, several resources are available:
- Help Net Security provides a summarized post on the details of the vulnerability.
- Openwall features the initial disclosure of the vulnerability.
- The National Vulnerability Database (NVD) entry for CVE-2024-3094 offers comprehensive information on the specifics of the vulnerability.
This incident serves as a reminder of the constant vigilance required in the digital age to protect against evolving cybersecurity threats.
Users are encouraged to promptly apply updates and stay informed on the latest security advisories.
Stay updated on Cybersecurity news, Whitepapers, and Infographics. Follow us on LinkedIn & Twitter.
.webp?w=696&resize=696,0&ssl=1)


