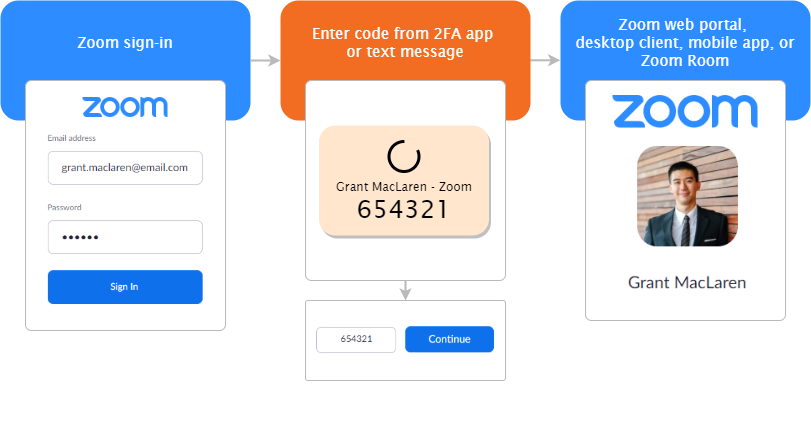
Zoom announced Two-Factor Authentication (2FA) for all users that let admins and organizations prevent security breaches & data thefts.
The two factor authentication (2fa) brings an additional security layer to the authentication process, blocking attackers from taking control of meetings by guessing the password or using compromised credentials.
“With Zoom’s 2FA, users have the option to use authentication apps that support Time-Based One-Time Password (TOTP) protocol (such as Google Authenticator, Microsoft Authenticator, and FreeOTP), or have Zoom send a code via SMS or phone call, as the second factor of the account authentication process,” Zoom explained in an announcement published today.
How to Enable Zoom’s 2FA
Zoom offers a range of authentication methods such as SAML, OAuth, and/or password-based authentication, which can be individually enabled or disabled for an account.
To enable Zoom’s 2FA at the account-level for password-based authentication, account admins should take the following steps:
- Sign in to the Zoom Dashboard
- In the navigation menu, click Advanced, then Security.
- Make sure the Sign in with Two-Factor Authentication option is enabled.
- Select one of these options to enable 2FA for:
- All users in your account: Enable 2FA for all users in the account.
- Users with specific roles: Enable 2FA for roles with the specified roles. Click Select specified roles, choose the roles, then click OK.
- Users belonging to specific groups: Enable 2FA for users that are in the specified groups. Click the pencil icon, choose the groups, then click OK.
- Click ‘Save’ to confirm your 2FA settings.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity, and hacking news updates.
Also Read
A New Zoom URL Flaw Let Hackers Mimic Organization’s Invitation Link
Zoom 0day Vulnerability Let Remote Attacker to Execute Arbitrary Code on Victim’s Computer
New Zoom Flaw Let Attackers to Hack into the Systems of Participants via Chat Messages



