Researchers from Avast have uncovered a vulnerability in the cryptographic schema of the Mallox ransomware, a particularly active variant between 2023 and early 2024.
This flaw allows victims of this specific Mallox variant to decrypt their files without paying a ransom.
However, this window of opportunity is limited. The ransomware developers rectified the flaw in March 2024, making newer versions immune to this decryption method.
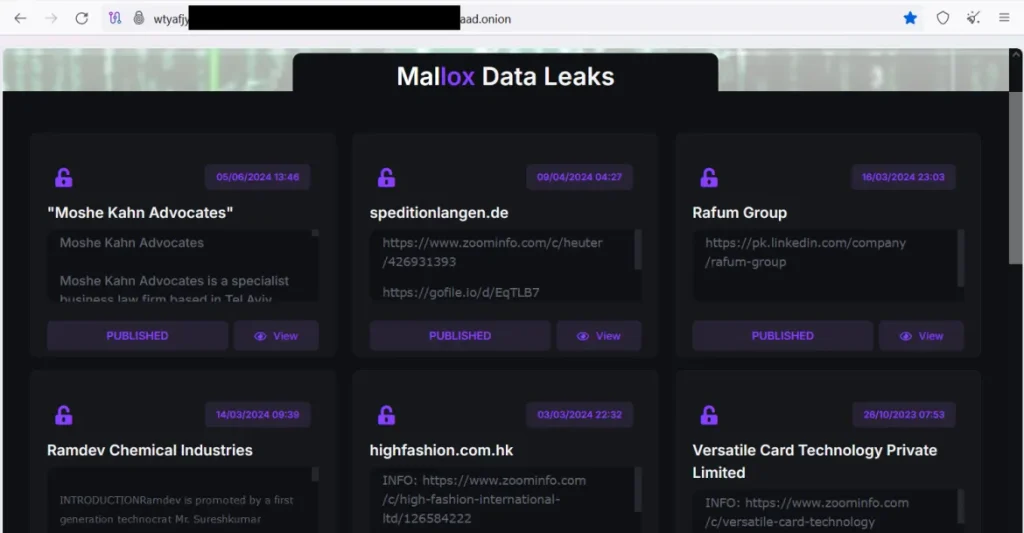
Mallox Ransomware
Mallox ransomware, formerly known as TargetCompany ransomware, has been a persistent threat since its emergence.
National Cybersecurity Awareness Month Cyber Challenges – Test your Skills Now
Initially, Avast released a decryptor for TargetCompany in January 2022. However, the ransomware’s developers quickly patched the cryptographic flaw by February 2022, rendering the decryptor ineffective.
Despite these improvements, subsequent iterations of Mallox introduced new cryptographic errors that allowed decryption without needing the private ECDH key.
As per a report by Gendigital, the Mallox ransomware has had a widespread impact globally, with telemetry data indicating significant activity across various countries from October 2023 to October 2024.
India, France, Portugal, Saudi Arabia, and the United States are among the five countries experiencing the highest number of blocked attacks.
The ransomware primarily targets Microsoft Windows systems and has been known to exploit unsecured MS-SQL servers for initial access.
Victims can identify if they have been affected by a decryptable version of Mallox by checking the file extensions appended during encryption.
The vulnerable versions were active from January 2023 to February 2024 and used extensions such as .bitenc, .ma1x0, .mallab, .malox, .malloxx, and .xollam.
Additionally, these versions leave ransom notes in folders with filenames like “FILE RECOVERY.txt,” “HOW TO BACK FILES.txt,” and “HOW TO RESTORE FILES.txt”.
For those affected by the decryptable versions of Mallox ransomware, Avast provides a free decryptor tool.
Users should run this tool on the same computer where the files were initially encrypted. The decryptor operates through a wizard interface that guides users through selecting files or folders for decryption.
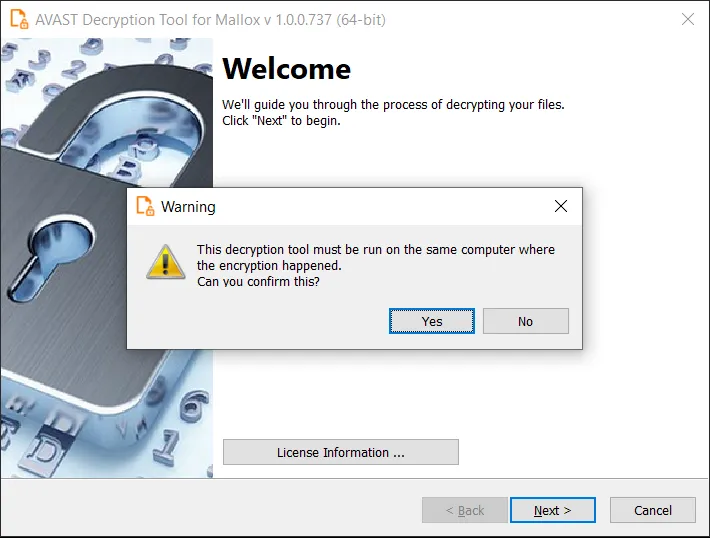
Encryption files should be backed up before beginning the decryption process to prevent data loss in case of errors.
While this discovery offers relief to some victims of Mallox ransomware, it highlights the ever-evolving nature of cyber threats and the importance of timely updates and patches in cybersecurity defenses.
Organizations are urged to maintain robust security measures and stay informed about potential vulnerabilities to mitigate risks associated with such ransomware attacks.
Free Webinar on How to Protect Small Businesses Against Advanced Cyberthreats -> Watch Here



.png
)
