A significant leap forward in cybersecurity was announced with the introduction of new threat intelligence (TI) capabilities in Security Copilot, aimed at giving organizations a comprehensive ‘360-degree’ view of attacker tools and methodologies.
These innovations promise to provide defenders with deeper insights into potential threats, making it easier than ever to detect and neutralize adversaries before they can cause harm.
New 360-degree Details Attackers Tools
Microsoft’s Security Copilot team has been working relentlessly to enhance its TI platform, and their latest developments offer unprecedented power to organizations seeking to stay ahead of attackers.
With the newly expanded threat intelligence capabilities, Security Copilot users can now build a more holistic view of threats by tapping into a vast array of TI sources.
Maximizing Cybersecurity ROI: Expert Tips for SME & MSP Leaders – Attend Free Webinar
This includes better insights into attacker tooling, methodologies, and their potential impact on an organization’s security posture.
One of the key updates announced at Ignite 2024 is the general availability (GA) of Security Copilot’s ability to integrate a wide range of TI sources into a single, unified view.
This gives customers a more comprehensive understanding of both known and emerging threats, allowing for faster and more effective responses.
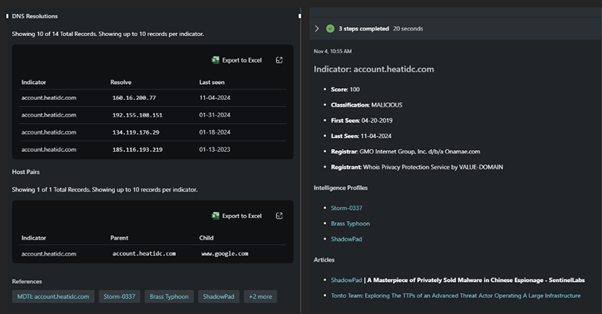
One of the most exciting new features is the public preview of MDTI indicator data, which introduces ten new skills that enhance the ability to link Indicators of Compromise (IoCs) to related threat intelligence.
This feature enables security analysts to access critical context around attacks, including connections to infrastructure, associated articles, and detailed information on attackers.
By using automated infrastructure chaining, analysts can now investigate relationships between different data sets more effectively.
This capability is invaluable for preemptive threat hunting, as it allows organizations to stay one step ahead of adversaries by uncovering new attacker tools and methodologies before they are fully deployed. The new skills harness two key categories of threat intelligence data:
- In-depth Indicators Data: This feature links IoCs with all relevant threat intelligence in MDTI, including profiles, detonation data, and reputation analysis. This allows security teams to quickly understand the nature of an attack and respond more efficiently.
- Indicators Metadata: By drawing from global internet data sets — including WHOIS, DNS, SSL certificates, and more — Security Copilot can map out the attacker’s infrastructure, enabling organizations to detect related activity and mitigate threats early.
Another major announcement was the GA expansion of Unified Vulnerability Intelligence within Security Copilot.
This enhancement integrates vulnerability and asset intelligence from Microsoft tools such as Microsoft Defender External Attack Surface Management (MDEASM), Defender Vulnerability Management (MDVM), and Threat Analytics.
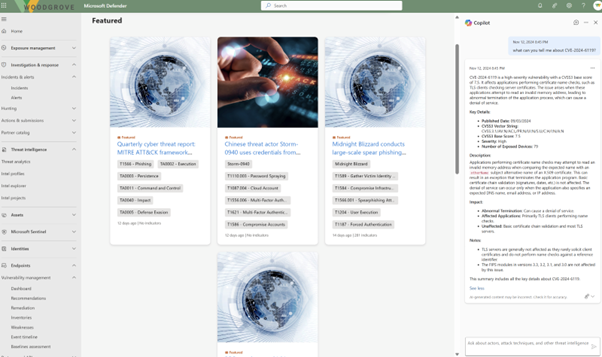
Through this integration, customers gain a more complete view of vulnerabilities, including how they are being exploited by threat actors.
The unified view provides organizations with detailed information on exposed assets, risk prioritization, and remediation steps, allowing for quicker and more informed decision-making.
With these innovations, Microsoft is continuing to lead the charge in providing cutting-edge cybersecurity tools.
By processing 78 trillion security signals daily, Microsoft’s Security Copilot delivers world-class threat intelligence, offering unparalleled insights into the global threat landscape.
This ensures that organizations have the tools they need to detect and respond to threats with speed and precision, safeguarding their critical assets.
Are you from SOC/DFIR Teams? – Analyse Malware Files & Links with ANY.RUN -> Try for Free



.png
)
