Cybersecurity experts are sounding the alarm over a new strain of malware dubbed “I2PRAT,” which leverages encrypted peer-to-peer (P2P) communication via the Invisible Internet Project (I2P) network to avoid detection.
The malware, first reported on November 19 by the researcher Gi7w0rm, demonstrates a highly sophisticated infection chain and innovative evasion techniques, raising concerns among the global cybersecurity community.
I2PRAT’s standout feature is its use of I2P, an encrypted P2P overlay network designed for anonymous communication.
Unlike traditional command-and-control (C2) communication methods, I2P obscures the source and destination of data, making it nearly impossible for security tools to intercept or trace the traffic.
The malware utilizes I2PD, an open-source I2P client, to establish these clandestine C2 channels, allowing it to exfiltrate data and receive commands without detection.
Free Webinar on Best Practices for API vulnerability & Penetration Testing: Free Registration
Infection Chain Overview
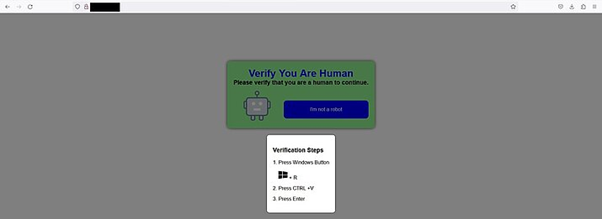
The malware’s infection chain begins with a targeted phishing email. Victims are lured into clicking a malicious link directing them to a fake CAPTCHA verification page.
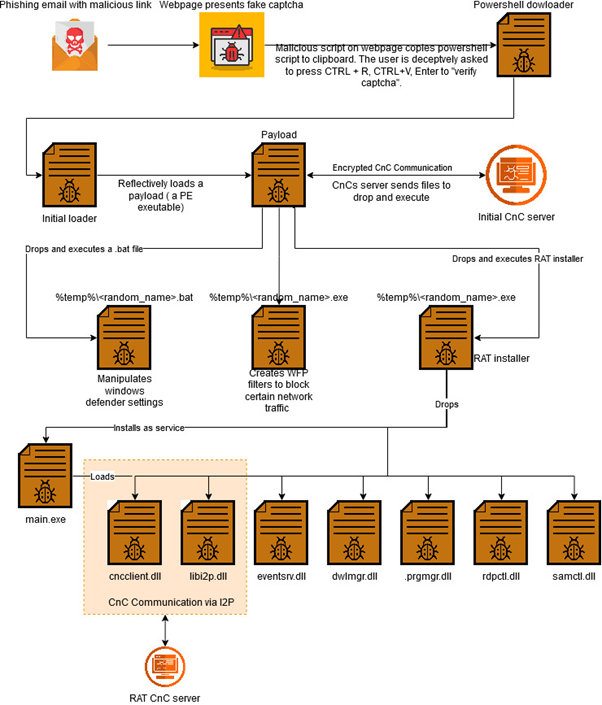
The page uses deceptive JavaScript to copy a malicious PowerShell script to the clipboard, tricking users into inadvertently executing it.
This script downloads the first-stage malware loader, which disables Windows Defender and deploys further malicious payloads.
Key steps in the infection chain include:
- Disabling Windows Defender to bypass antivirus protections.
- Deploying Windows Filtering Platform (WFP) filters to block Microsoft security updates.
- Installing a Remote Access Trojan (RAT) as a system service.
- Establishing encrypted C2 communication through I2P.
I2PRAT incorporates multiple layers of obfuscation and defense evasion tactics. For example, it deploys batch scripts to disable Microsoft Defender updates and exclude key directories from scans.
Additionally, it leverages WFP filters to block telemetry data from being sent to Microsoft’s security cloud, rendering the infected device vulnerable and blind to updates.
The malware also employs a clever trick by creating a hidden directory named to resemble the “My Computer” system shortcut, making its files hard to locate. Permissions within this directory are restricted using utilities like icacls.exe, further masking its presence.
Modular RAT and I2P Communication
At the core of I2PRAT is a modular Remote Access Trojan (RAT) that uses plugins to deliver various malicious functionalities. Communication between the malware and its C2 infrastructure is established through I2P, ensuring all data exchanges are encrypted and anonymized.
This approach allows threat actors to issue commands, exfiltrate sensitive information, and deploy additional payloads while evading traditional network monitoring.
I2PRAT showcases the growing trend of malware developers adopting encrypted P2P networks like I2P to outmaneuver cybersecurity defenses, as per a report by Gdata Software.
The use of anonymized communication channels complicates detection and mitigation, posing a significant challenge for organizations and researchers alike.
To counter such threats, organizations must adopt advanced threat detection systems capable of monitoring anomalous network behaviors and implement robust email security protocols to prevent phishing attacks.
End-user awareness training also plays a critical role in reducing the likelihood of successful exploits.
The cybersecurity community continues to analyze I2PRAT to develop effective countermeasures, but its use of encrypted P2P communication highlights an alarming evolution in cyber threats.
Investigate Real-World Malicious Links, Malware & Phishing Attacks With ANY.RUN – Try for Free



