The Oligo Research team has disclosed a critical vulnerability in Meta’s widely used Llama-stack framework.
This vulnerability, tracked as CVE-2024-50050, allows remote attackers to execute arbitrary code on servers running the Llama-stack framework.
Due to its potential impact, the flaw has been rated as critical with a CVSS score of 9.3 (v4.0) and 9.8 (v3.1).
The Meta Llama Framework and Its Importance
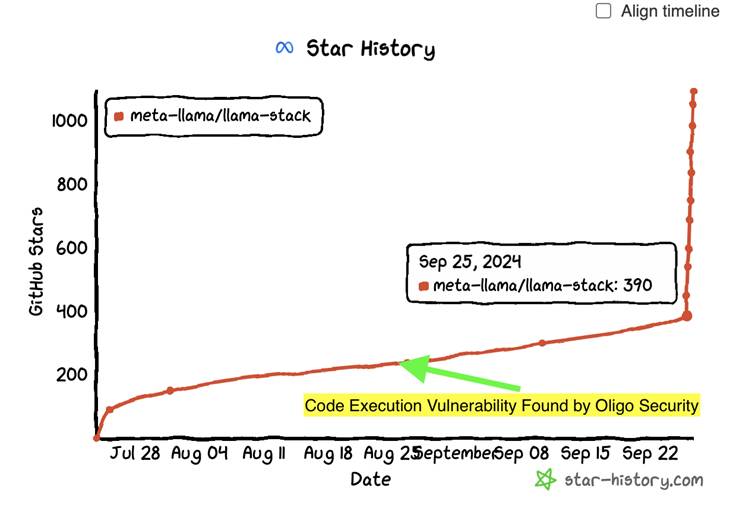
Meta introduced the Llama-stack framework in July 2024 as an open-source solution to simplify the development and deployment of generative AI (GenAI) applications based on its Llama family of large language models (LLMs).
This framework offers developers tools and APIs to train, deploy, and operate AI models efficiently, enabling faster innovation in AI-powered applications.
Are you from SOC/DFIR Teams? - Analyse Malware Files & Links with ANY.RUN Sandox -> Try for Free
The adoption of the Llama-stack framework has grown rapidly, with backing from industry giants like AWS, NVIDIA, and Dell.
It has also gained traction among developers worldwide, accumulating over 6,000 stars on GitHub. However, this popularity has now brought attention to the unforeseen security risks embedded in the framework’s code.
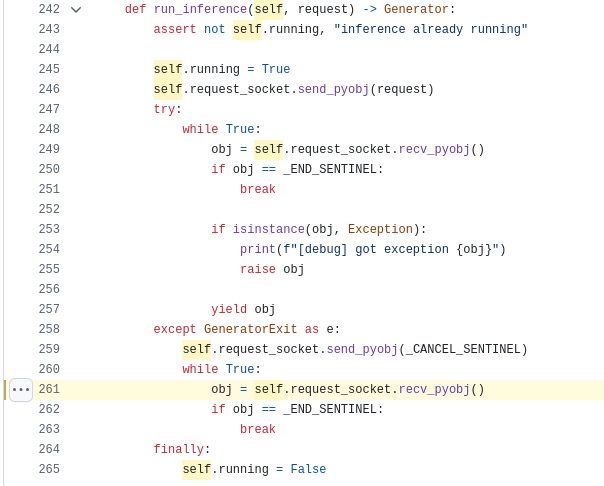
The flaw resides in a Python method, recv_pyobj, used in the default Python inference server of the Llama-stack framework.
This method leverages Python’s pickle module to deserialize serialized objects received via a network socket.
The pickle module, while powerful, is notoriously insecure when used with untrusted data because it can execute arbitrary commands during the deserialization process.
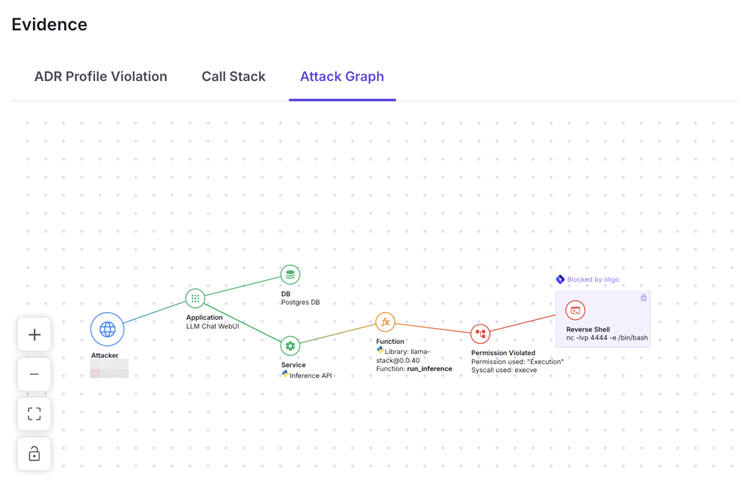
Attackers exploiting this vulnerability can send maliciously crafted data to a Llama-stack server. When the server deserializes this data using recv_pyobj, it executes the attacker’s commands, potentially allowing full control over the server.
This opens the door to various malicious activities, such as resource theft, data breaches, and tampering with hosted AI models.
The vulnerability stems from the use of the pyzmq library, a Python implementation of the ZeroMQ messaging protocol.
While pyzmq’s recv_pyobj method is efficient, the library itself warns against its unsafe use with untrusted sources due to its reliance on the insecure pickle.loads function.
Meta’s default inference implementation improperly exposed this function over the network, leaving it susceptible to exploitation.
Proof-of-Concept Exploit
Security researchers from Oligo demonstrated how the vulnerability could be exploited. By scanning for open ports on systems running Llama-stack and sending a specially crafted malicious payload, they achieved remote code execution (RCE).
class RCE:
def __reduce__(self):
import os
cmd = 'touch /tmp/pickle_rce_created_this_file.txt && echo RCE'
return os.system, (cmd,)For example, attackers could run arbitrary commands on the compromised server using a custom Python class that defines a method to execute shell commands.
Oligo responsibly disclosed the vulnerability to Meta on September 29, 2024. Meta responded promptly and released a patch within two weeks, addressing the issue in version 0.0.41 of the Llama-stack framework.
The fix replaced the vulnerable pickle-based deserialization with a more secure JSON-based implementation using the Pydantic library, which enforces type safety and removes the risk of arbitrary code execution.
The maintainer of pyzmq also introduced warnings in the documentation, advising developers against using recv_pyobj with untrusted data in the future.
- Immediate Upgrade: To protect against this critical vulnerability, all users of the Llama-stack framework are urged to upgrade to version 0.0.41 or higher.
- Secure Design Practices: Avoid using modules like Pickle to deserialize untrusted data. Opt for safer alternatives such as JSON or Pydantic.
- Monitor Open Ports: Regularly scan for open ports and monitor network activity to detect potential exploitation attempts.
The discovery of CVE-2024-50050 highlights the inherent risks in open-source development, where even widely adopted frameworks can harbor critical vulnerabilities.
Meta’s swift response underscores its commitment to maintaining the security of its AI ecosystem.
Integrating Application Security into Your CI/CD Workflows Using Jenkins & Jira -> Free Webinar



.png
)
