A critical vulnerability in the Cacti performance monitoring framework tracked as CVE-2025-22604, has been disclosed, with a proof-of-concept (PoC) exploit now publicly available.
This vulnerability allows authenticated users with device management permissions to execute arbitrary code on the server by exploiting a multi-line SNMP result parser flaw.
The vulnerability has been rated as critical with a CVSS score of 10.
Technical Details
The vulnerability resides in how Cacti processes SNMP responses:
- SNMP Response Parsing: The cacti_snmp_walk() function uses exec_into_array() to process multi-line SNMP results into an array. Malformed Object Identifiers (OIDs) can be injected into these responses.
- Command Injection: The functions ss_net_snmp_disk_io() and ss_net_snmp_disk_bytes() use parts of these OIDs as keys in an array, which are later incorporated into system commands. Improper filtering of OIDs enables attackers to inject malicious commands.
- Shell Command Execution: The JSON-encoded data is passed to a shell command using shell_exec(), where improper quoting allows attackers to break out and execute arbitrary commands.
Integrating Application Security into Your CI/CD Workflows Using Jenkins & Jira -> Free Webinar
PoC Exploit
Below is the step-by-step process for exploiting the vulnerability:
- Start an SNMP agent to send the payload.
- Change the “Local Linux Machine” device port in Cacti to your agent’s port.
- Add the “Net-SNMP – Combined SCSI Disk I/O” graph template to the device if it’s not already present.
- Navigate to the graph tree and select “Local Linux Machine.”
- Click “View in Realtime” under the “Combine SCSI Disk I/O” graph.
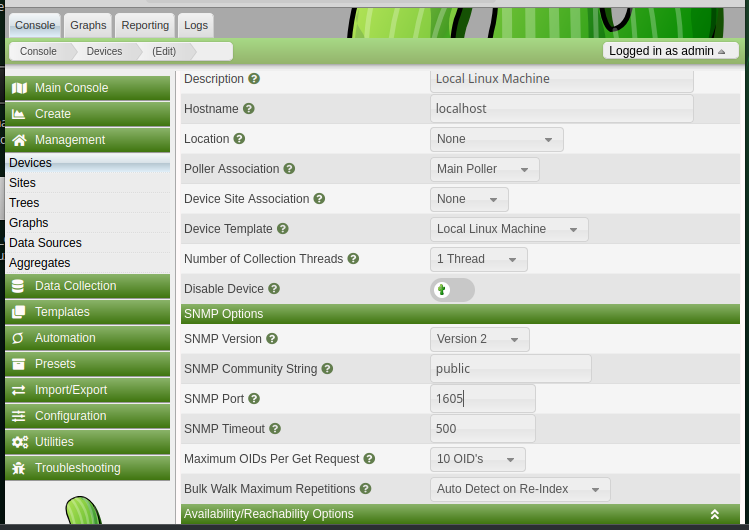
As per a report by Github, this sequence exploits the vulnerability by injecting malicious OIDs into SNMP responses, which are then executed on the server.
Code Example
Below is a simplified PoC code snippet that demonstrates how an attacker can exploit this vulnerability:
<?php
// Malicious SNMP agent payload
$payload = '1.3.6.1.4.1.x.x.x = STRING: "; /bin/bash -c \'echo hacked > /tmp/hacked\' ;"';
// Start SNMP agent
exec("snmptrap -v 2c -c public localhost '' $payload");
// Configure Cacti to point to malicious agent
$cacti_url = "http://target-cacti-instance";
$device_id = 1; // Replace with actual device ID
$snmp_port = 161; // Replace with malicious agent's port
// Update device configuration
exec("curl -X POST $cacti_url/device.php -d 'id=$device_id&snmp_port=$snmp_port'");
// Trigger the exploit
exec("curl $cacti_url/graph_realtime.php?device_id=$device_id");
?>This vulnerability allows attackers to:
- Execute arbitrary commands on the server.
- Steal, modify, or delete sensitive data.
- Compromise the entire system hosting Cacti.
To protect against this critical flaw:
- Update Immediately: Upgrade to Cacti version 1.2.29 or later, which includes a patch for this issue.
- Restrict Access: Limit access to trusted users and restrict network access to Cacti instances.
- Monitor Logs: Regularly inspect logs for unusual activity or malformed SNMP responses.
The release of a PoC exploit for CVE-2025-22604 underscores the importance of timely patching and secure configurations for network monitoring tools like Cacti.
Organizations using vulnerable versions must act swiftly to mitigate potential risks and protect their systems from exploitation.
Collect Threat Intelligence with TI Lookup to improve your company’s security - Get 50 Free Request



.png
)
