A security researcher has uncovered critical vulnerabilities in Eight Sleep’s internet-connected smart beds, revealing exposed Amazon Web Services (AWS) credentials, remote SSH backdoors, and potential access to users’ entire home networks.
The findings underscore growing concerns about IoT device security as consumers increasingly adopt connected appliances for everyday use.
Researcher Discovers AWS Keys and Remote Access Protocols
The investigation began when the researcher, who purchased the $2,000 temperature-regulated Eight Sleep Pod mattress cover, discovered live AWS credentials embedded in the device’s firmware.
These keys granted write access to Amazon Kinesis data streams, potentially allowing attackers to manipulate sleep data or inflict substantial financial damage through excessive API requests.
While Eight Sleep revoked the keys after being notified, the incident highlighted systemic security gaps.
Further analysis revealed a more alarming issue: a remote SSH backdoor accessible via remote-connectivity-api.8slp.net.
Configuration files showed engineers at eng@eightsleep.com could bypass standard code review processes to execute arbitrary commands on users’ beds, which operate on Linux-based systems.

“This isn’t just about adjusting bed temperatures,” the researcher noted. “It’s a gateway to every device on your Wi-Fi—laptops, smart locks, security cameras.”
The SSH vulnerability grants unprecedented access to sensitive data, including:
- Sleep patterns and bed occupancy detection
- Remote activation of vibration alerts or alarms
- Network traversal capabilities to connected devices
Notably, Eight Sleep’s system lacks user-accessible logs to monitor such access.
The researcher compared the risk to Uber’s 2014 “God Mode” scandal, where employees tracked politicians and celebrities, stressing that compromised engineering credentials could enable similar abuses.
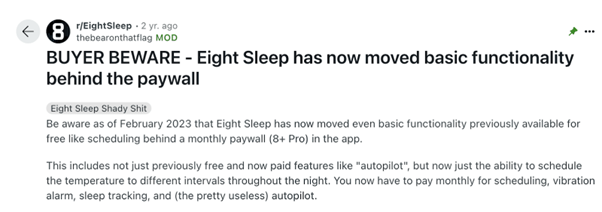
Company Response and Consumer Alternatives
Eight Sleep has not publicly addressed the SSH backdoor concerns but previously marketed sleep-tracking features through social media posts like “We’re watching you sleep.”
Meanwhile, the researcher devised a low-tech workaround using a $150 aquarium chiller—a device employing the same thermoelectric technology—by rerouting the mattress’s cooling tubes.

This modification preserves temperature control without internet dependency, subscription fees, or attack surfaces.
This incident reflects widespread issues in IoT ecosystems, where convenience often overshadows security.
The researcher urged manufacturers to adopt zero-trust architectures and encrypted local controls: “Your bed shouldn’t be a Trojan horse for hackers.”
For now, consumers must weigh the benefits of connected devices against risks to their digital and physical safety.
Analogies to historical breaches (e.g., Uber’s “God Mode”) provide layperson-friendly parallels, while the aquarium chiller solution offers actionable advice without promotional language.
Free Webinar: Better SOC with Interactive Malware Sandbox for Incident Response, and Threat Hunting - Register Here



.png
)
