A critical 0-day vulnerability has been disclosed in CentreStack, a popular enterprise cloud storage and collaboration platform, which could allow attackers to execute arbitrary code remotely on affected web servers.
The vulnerability, tracked as CVE-2025-30406, leverages a flaw in the application’s handling of cryptographic keys responsible for securing sensitive ViewState data.
Flaw in MachineKey Management Exposes Servers
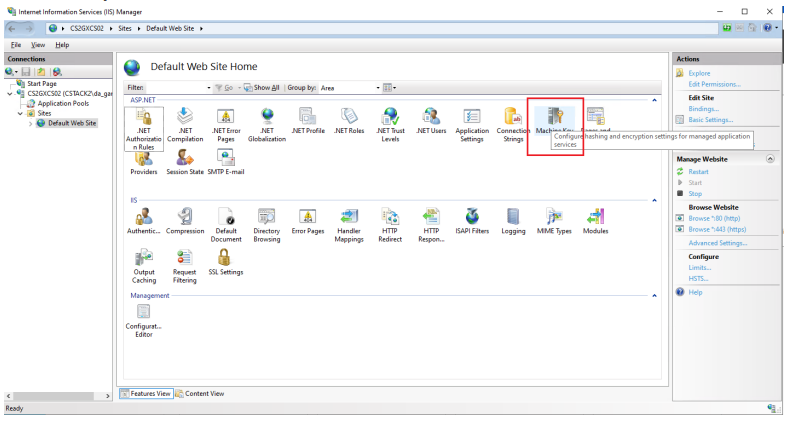
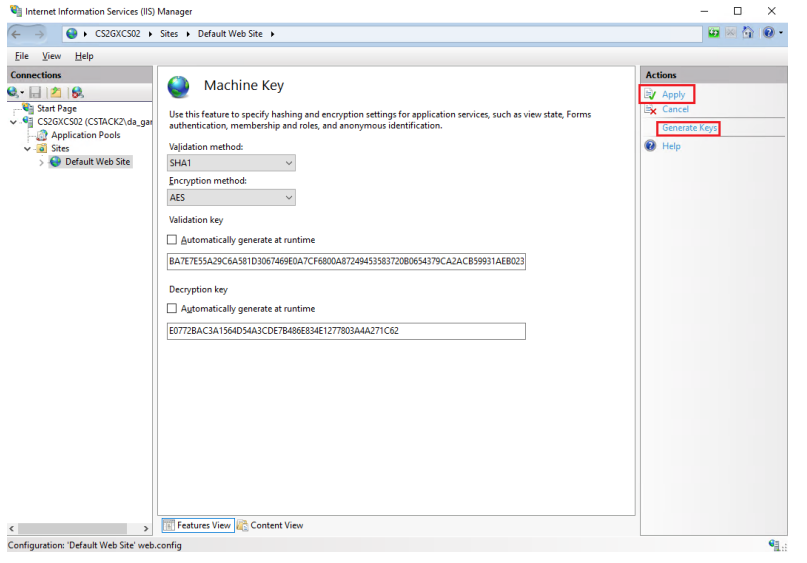
According to the official security advisory, the exploit centers on the use of hardcoded or improperly managed machine key values in the Internet Information Services (IIS) web.config file.
The machineKey is crucial for ensuring the integrity and confidentiality of ASP.NET ViewState data, which is used to maintain state across web requests.
If a threat actor is able to obtain or accurately predict the machineKey, they can forge malicious ViewState payloads that pass the application’s verification checks.
This in turn can lead to so-called ViewState deserialization attacks—a well-known vector for remote code execution (RCE).
Experts warn that, if exploited, this vulnerability could give attackers the same level of access as the underlying web server service account, potentially leading to data theft, lateral movement, or full server takeover.
Exploitation Confirmed in the Wild
Security researchers have observed attempts to exploit this vulnerability in the wild, escalating the urgency for organizations to apply protective measures.
The CentreStack team has responded rapidly, releasing a patched version—build 16.4.10315.56368—that automatically generates and applies a unique machineKey for each installation.
Immediate Mitigation Steps Recommended
For organizations unable to update immediately, interim mitigation steps have been provided:
- Rotate the machineKey: Generate a new, unique machineKey using IIS Manager, and update the web.config file for all CentreStack nodes.
- Synchronize Keys on Server Farms: In deployments with multiple nodes, ensure all share the same newly generated key.
- Remove Legacy Keys: Edit portal/web.config files to remove outdated or hardcoded key entries.
- Restart IIS: After making these changes, restart IIS to apply the new configuration.
Full details, including step-by-step instructions and links to the latest secure build, are available in the CentreStack support knowledge base.
Enterprise IT administrators are urged to assess their CentreStack deployments immediately.
Given the observed exploitation and the potential for complete server compromise, delaying remediations could expose organizations to significant risk.
Find this News Interesting! Follow us on Google News, LinkedIn, & X to Get Instant Updates!



.png
)
