Google patches a critical vulnerability with MediaTek rootkit chips that affect millions of devices with chipsets from MediaTek.
MediaTek is a large Taiwanese chip design company that provides chips for wireless communications, High-definition television, and devices like smartphones and tablets.
MediaTek bug
The vulnerability tracked as CVE-2020-0069 discovered first by members of the XDA developers forum while looking for a possible way to Amazon’s Fire tablets.
The bug is open to the Internet since April of 2019, now the attackers started exploiting in the attack campaigns.
MediaTek released a patch attempting to fix the vulnerability last year, but the attackers continue to exploit the vulnerability by installing a malicious app on the device.
The exploit works with all the MediaTek’s 64-bit chipsets that include Motorola, OPPO, Sony, Alcatel, Amazon, ASUS, Blackview, Realme, Xiaomi and other devices.
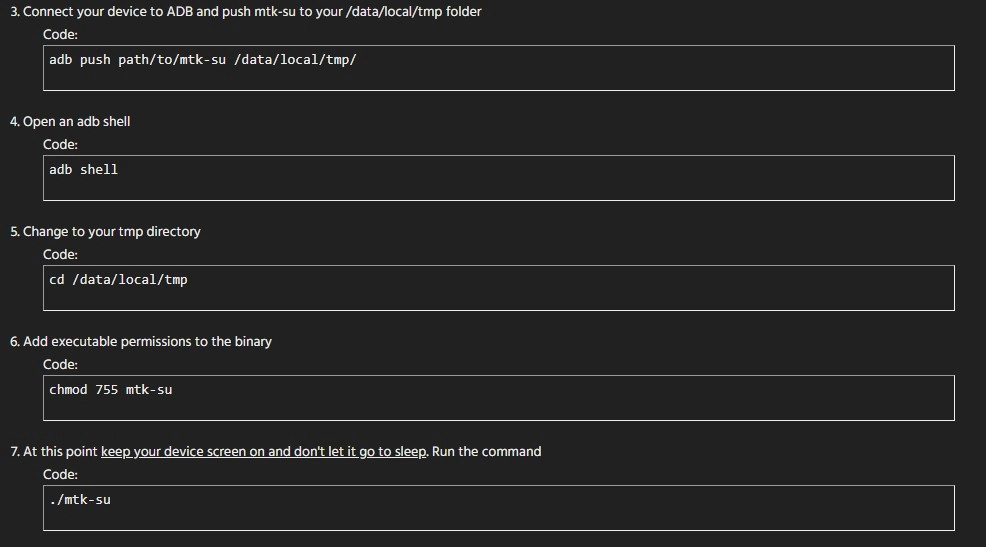
Exploiting the vulnerability is simple, the author of the vulnerability “shared a script that users can execute to grant them superuser access in shell, as well as set SELinux, the Linux kernel module that provides access control for processes, to the highly insecure “permissive” state.”
This vulnerability allows any user to get root access and to set SELinux permissive on their device is easy, by just copying the script to the temporary folder, providing executable permission and executing it.
Starting this January Trend Micro spotted it malicious spyware apps on the Google play using MediaTek-SU get root privileges.
Now the vulnerability was patched by Google along with other critical vulnerabilities as a part of the March 2020 Android Security bulletin.
Another critical bug patched is CVE-2020-0032 which can be exploited with a maliciously crafted file to execute arbitrary code within the context of a privileged process.



.png
)
