Researchers discovered a new wave of malware campaign that believed to be launched by APT hackers group using legitimate NSIS software to pack and launch the Shellcode on Windows.
NSIS (Nullsoft Scriptable Install System) is an open-source system script-driven installer authoring tool for Microsoft Windows and is used to create Windows installers.
Attackers abusing the Microsoft Crypto API to decrypt the final payload from the packer named “Loncom”, and the malware named as Trojan-Dropper.NSIS.Loncom.
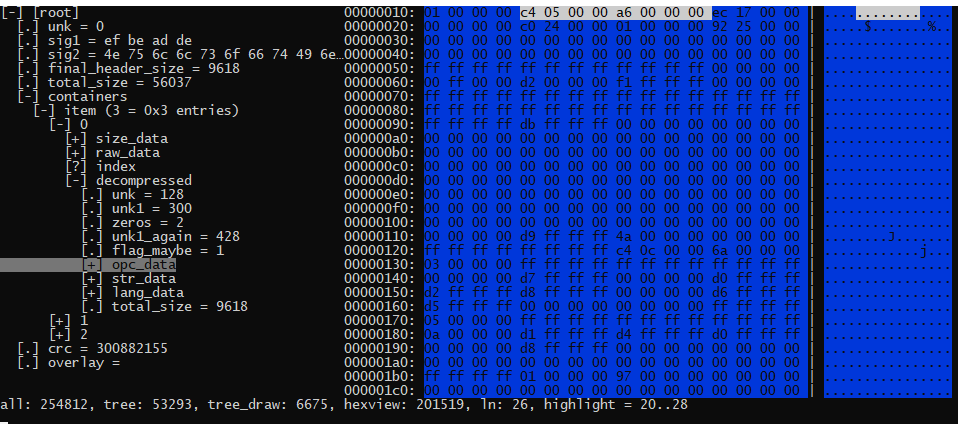
Loncom packer utilizes the NSIS software to run the shellcode from the file named as ” 48510113″, and the shellcode is unpacked to the hard disk and loaded into the memory.

Shellcode using an algorithm to decrypting itself step by step, once it decrypts the several such iterations of block, Shellcode starts loading libraries and retrieving the addresses of required functions with the help of the APIHashing technique.
After that, Loncom decrypts the another payload with an AES-256 block cipher that contains the same Shellcode.
Researchers analysed and observed the structure of the NSIS installers and find the final payload that located above the shellcode.
Accoding to Securelist report “we noticed packed specimens of Backdoor.Win32.DarkVNC and Trojan-Ransom.Win32.Sodin families, also known as REvil and Sodinokibi. The first is a type of backdoor used for controlling an infected machine via the VNC protocol. The second is a ransomware that encrypts the victim’s information and threatens to publish it.”
Researchers also found that the campaign Cobalt Strike utility that used by the professional pentesters and some time it abused by APT hacker groups.
“The command center of the sample that contained Cobalt Strike had previously been seen distributing CactusTorch, a utility for running shellcode present in Cobalt Strike modules, and the same Cobalt Strike packed with a different packer,” Researchers said.
You can read the complete technical analysis here.
Also Read: Kinsing Malware Attacks Misconfigured Open Docker Daemon API Ports
IOC
BB00BA9726F922E07CF243D3CCFC2B6E (Backdoor.Win32.DarkVNC)
EBE191BF77044961684DF51B88CA8D05 (Backdoor.Win32.DarkVNC)
4B4C98AC8F04680F7C529956CFE8519B (Trojan-Ransom.Win32.Sodin)
AEF8FBB5C64734093E78EB13E6FA7849 (Cobalt Strike)



.png
)
