Over the past few weeks FireEye, Microsoft, SolarWinds and several US government departments have been subject to attack by the “Sunburst” malware injected via the infected SolarWinds Orion software.
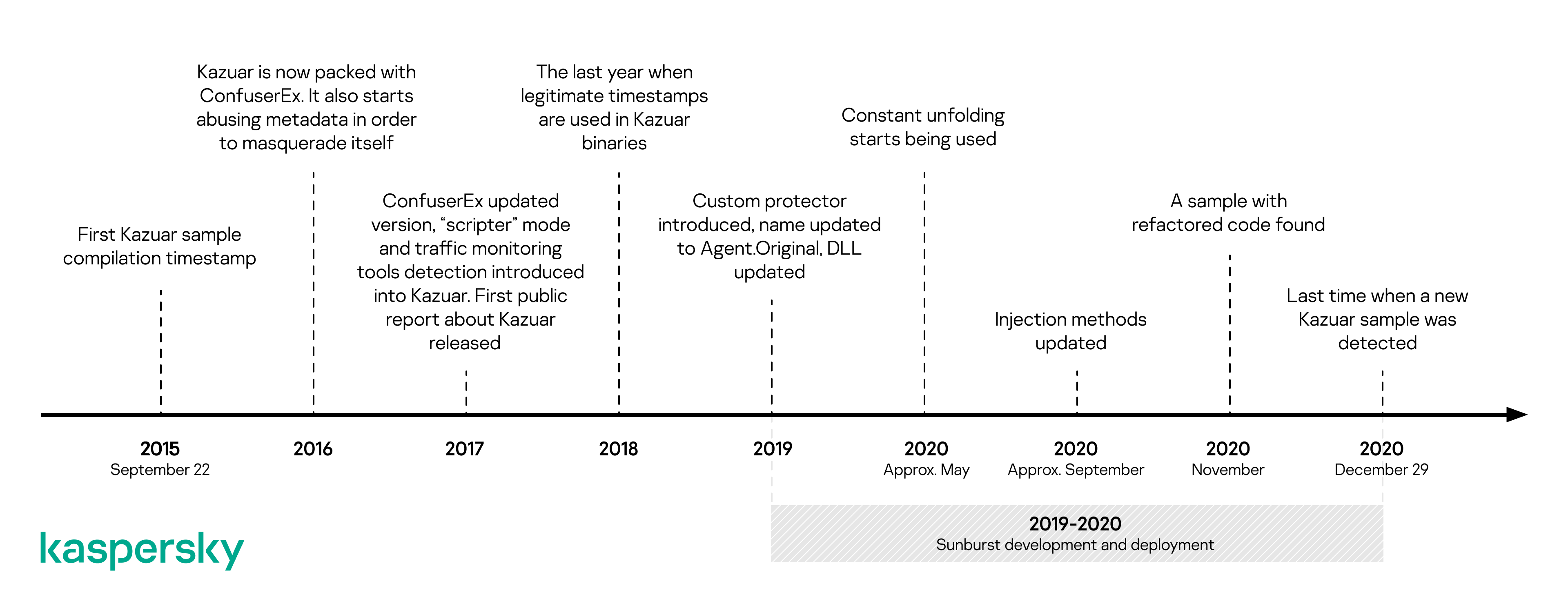
Similarities have been found by Kaspersky between the Sunburst backdoor and Kazuar, a .NET backdoor reportedly linked to the Russian Turla hacking group. Over the course of the investigation the FBI, CISA, and the NSA also suspected that the SolarWinds attacks too had Russian links.
Turla also goes by the names Venemous Bear and Waterbug. Turla specializes in coordinating information theft and espionage campaigns and has a track record going back as far as 1996.
They have been enlisted as the main suspects behind the attacks targeting the Pentagon and NASA. And The U.S. Central Command.
The algorithm used to generate victim UIDs, the extensive usage of the FNV-1a hash and the sleeping algorithm of both the backdoors are some of the major similarities found between Kazuar and Sunburst.
Despite these similarities, the extent of the similarities and nature of the relationship is still unclear.
Some of the explanations for these similarities highlighted by Kaspersky’s report include:
- Sunburst was developed by the same group as Kazuar
- The Sunburst developers adopted some ideas or code from Kazuar, without having a direct connection (they used Kazuar as an inspiration point)
- Both groups, DarkHalo/UNC2452 and the group using Kazuar, obtained their malware from the same source
- Some of the Kazuar developers moved to another team, taking knowledge and tools with them
- The Sunburst developers introduced these subtle links as a form of false flag, in order to shift blame to another group
Kaspersky researchers feel that a coincidence or two would not be too surprising, however, when there are three such coincidences it is definitely quite suspicious.
Having said that, researchers at Kaspersky have not ruled out the possibility that these could be planted to misdirect the investigation. Further technical details can be found in the detailed report published by Kaspersky.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity, and hacking news updates.



.png
)
