The North Korean threat actors under the Kimsuky Umbrella are using a piece of malware which is called KONNI.
KONNI is a RAT (Remote Administration Tool) that is under the radar for nearly 8 years since its identification in 2014.
The owners of KONNI have been attacking political institutions in South Korea and Russia.
They distributed the malware by impersonating government software by sending emails from compromised accounts. It seems that they have also used the covid mandates to enhance their malware campaign.
On January 5th, A new campaign targeted the Russian Ministry of Foreign Affairs. They got access to one of the high-value networks through stolen credentials and exploited all the trusted connections.
Attack Process
They have been leveraging on Microsoft Office documents which involved a multi-stage attack.
Although they used these documents just to accomplish to escalate privileges and evade detection, their ultimate goal was to install KONNI rat on target systems.
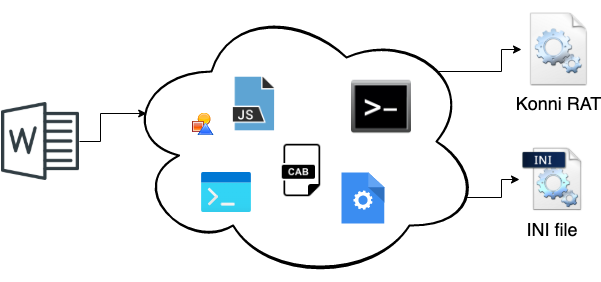
The KONNI rat is a .dll file which is supported with a .ini file.
The .dll consists of the functionality whereas the .ini file specifies the address of the command and control server. The new variant is not much different from the previous version but has certain advancements.
Many of the remote administration tool malware use protection for their strings in order to bypass the basic string analysis. The strings that were used in the KONNI rat were using base64 encoding for obfuscation.
Now, they are using AES encryption with a custom alphabet that changes from time to time which takes more time to decode.
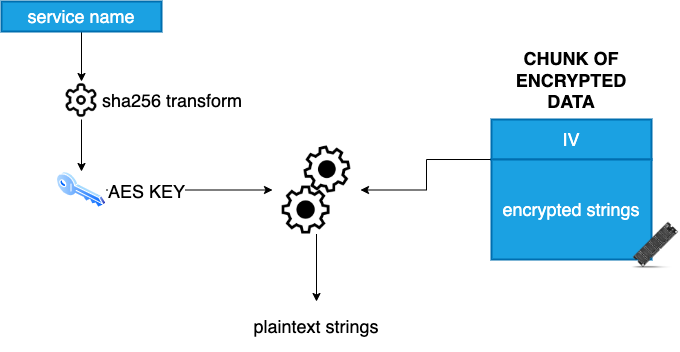
This is applied to files too. KONNI rat used a .dll file and a .ini file. These files are now encrypted with AES encryption making them difficult to analyze.
A full detailed analysis of the KONNI rat is published which gives a better understanding of the techniques and methods used.
IOCs
A3CD08AFD7317D1619FBA83C109F268B4B60429B4EB7C97FC274F92FF4FE17A2
F702DFDDBC5B4F1D5A5A9DB0A2C013900D30515E69A09420A7C3F6EAAC901B12



.png
)
