A significant vulnerability has been discovered in the Alibaba Cloud Object Storage Service (OSS) that allows unauthorized users to upload data, posing critical security risks for organizations relying on this cloud solution.
The vulnerability, caused by the misconfiguration of the PUT method, potentially exposes sensitive data and leaves storage buckets open to exploitation.
The security researcher behind this finding shared a detailed walkthrough of their discovery process:
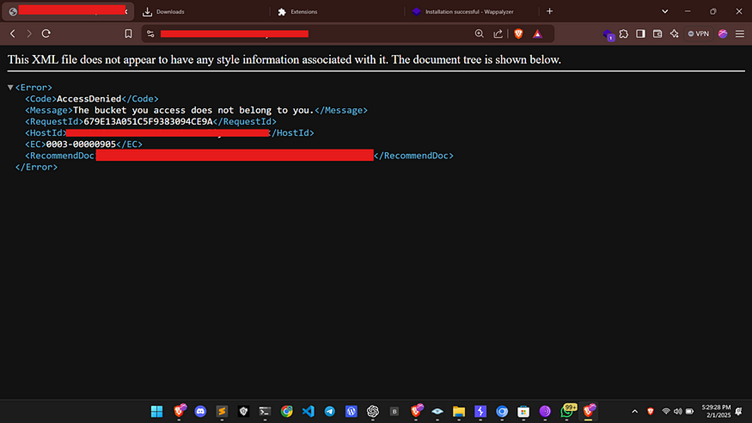
1. Identifying the Target
While browsing a target website, the researcher encountered a “403 Forbidden” response, indicating restricted access to a specific resource.
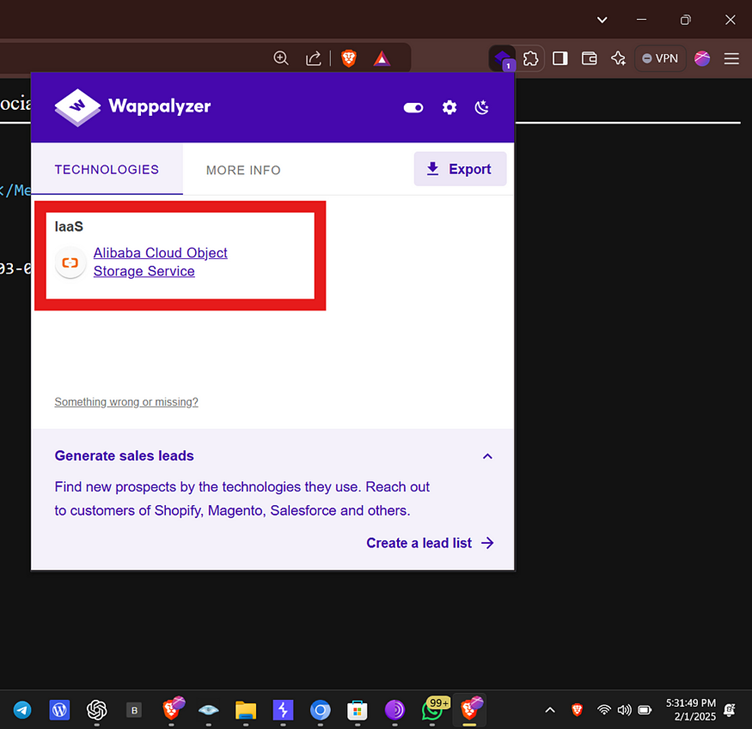
2. Technology Detection
Using the Wappalyzer browser extension, the researcher confirmed that the website was utilizing Alibaba Cloud Object Storage Service (OSS) for its storage infrastructure.
3. Capturing the Request
The researcher employed Burp Suite to capture and analyze the request made to the server. The initial request was structured as follows:
GET / HTTP/1.1
Host: target.com
...The server responded with a “403 Forbidden” message but disclosed that it was running on the AliyunOSS platform.
4. Testing the PUT Method
Despite the restricted “GET” request, the researcher proceeded to test the “PUT” method, which allows users to upload data to the server. A modified request was sent to upload a JSON file (poc.json) containing a simple payload:
PUT /poc.json HTTP/1.1
Host: target.com
...
Content-Length: 32
{"id": "hacked-by-waseem"}5. Successful Upload
Surprisingly, the server responded with a “200 OK” status, indicating that the file was successfully uploaded.
HTTP/1.1 200 OK
Server: AliyunOSS
Date: ...
ETag: "1650257635488786160B4C064076B0A1"HTTP/1.1 200 OK
Server: AliyunOSS
Date: ...
ETag: "1650257635488786160B4C064076B0A1"6. Verifying the Upload
The uploaded file was then accessed, confirming that the data was successfully stored in the target OSS bucket.
This misconfiguration in Alibaba Cloud OSS could lead to:
- Unauthorized Data Storage: Attackers could use the storage bucket to upload malicious or illicit content.
- Overwriting Files: Attackers could overwrite existing files, potentially impacting operational data or applications.
- Data Breaches: Sensitive information stored in the bucket could be exposed due to unauthorized uploads or access.
This critical vulnerability highlights the importance of securing cloud storage configurations.
Organizations using Alibaba Cloud OSS must assess their security settings immediately, ensuring that robust authentication and access control mechanisms are in place to prevent unauthorized actions.
As cloud-based storage continues to grow in popularity, such findings serve as a reminder of the ever-present need for vigilance in securing digital assets.
Are you from SOC/DFIR Teams? – Analyse Malware Files & Links with ANY.RUN Sandox -> Start Now for Free.



.png
)
