Bitdefender Security Researchers identified a new, highly sophisticated spyware targeting Android users for financial motivations and distributed via Google Apps Market place.
Researchers named the threat “Mandrake” and estimated victim users were probably hundreds of thousands throughout the full 4-year period.
Malware has complete control over infected android phones as it can turn down the volume of the phone and block calls or messages, steal credentials, exfiltrate information, money transfers, and blackmailing.
Malicious applications on Google Play:
Mandrake operators published seven malicious applications, “Abfix, CoinCast, SnapTune Vid, Currency XE Converter, Office Scanner, Horoskope, and Car News “on Google Play market place for creditability.
To disguise as a legitimate app, these apps have a dedicated microsite, a Facebook page, social media accounts like Twitter, Telegram or Reddit and even YouTube channels to gain the user’s interest & trust to get victimized.
Researchers highlighted that “Besides posing as legit applications, the apps use extra techniques to avoid Google Play protection: they delay malicious activity greatly and work in stages.
These three stages are dropper, loader, and core. These functionalities have different roles and complexity. The dropper is considered the app that the victim installs from Google Play.

One cannot predict when they will get the loader and the core components, which will be downloaded by the dropper at some point when the attacker issues the command (or possibly never)”.
Threat Infrastructure
Mandrake used several hardcoded Command and Control servers as mentioned below and most of them were active for the full 4 years. Researcher spot an active C2 server androidfirmware(.)top associated with ip address “159.69.66.184” and hosting provided by “Hetzner Online GmbH” in Germany location.
| Domain | Registration Date |
| rendfiles.top | 11-02-2016 |
| androidfrimware.com | 06-04-2016 |
| android-soft.top | 09-04-2016 |
| androidfirmware.ca | 06-06-2016 |
| nfmmlrkagflemt.top | 17-11-2016 |
| xjkbhysexthnpl.top | 23-11-2016 |
| livingstream.mobi | 14-12-2016 |
| androidfirmware.top | 21-08-2019 |
The malicious applications hosted on Google play targets mostly banking applications such as CommBank, NAB Mobile Banking, Westpac Mobile Banking, Bankwest, Bendigo Bank, St.George MobileBanking, ING Australia Banking, AustralianSuper, Beyond Bank Australia.
Other target applications belonged to cryptocurrency, communications, a gaming application, and product category. For example: PayPal Mobile Cash: Send and Request Money Fast, Microsoft Outlook: Organize Your Email & Calendar, Google Pay: Pay with your phone and send cash, Amazon Shopping – Search Fast, Browse Deals Easy, AliExpress – Smarter Shopping, Better Living, Coinbase – Buy & Sell Bitcoin, Crypto Wallet, Blockchain Wallet-Bitcoin, Bitcoin Cash, Ethereum and VIP Access.
This campaign masters all elements of a professional spyware platform,this attack is most likely financially motivated. This threat can easily defeat two-factor authentication (2FA) codes that some banks send to prevent fraud.
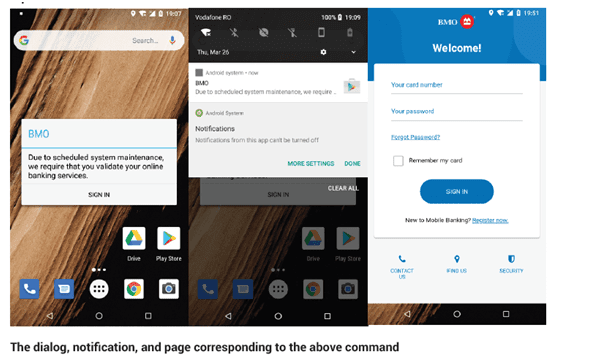
It conducts phishing attack on targeted application, by loading a webpage and injecting a specially crafted JavaScript code to retrieve all data from input forms loaded in an overlay web component.In some cases, for legitimate apps that are themselves webviews, the user is not aware he’s interactingwith a credential-stealing page.
As a backup measure in case JavaScript injection fails, the screen is also recorded, this MP4 recording is saved as <timestamp>.dat in the private files dir and it is later sent to the C2 server with a post request to URL http://androidfirmware.top:8888/?r=<victim UID>.
Mandrake targets specific countries: Australia, Canada, United States, Poland, Netherlands, Germany, Austria, Italy, Spain, United Kingdom, Belgium, Brazil, CzechRepublic, and Singapore”, besides targeting globally utilized popular applications.
It was observed that more than 40 different targeted banking applications that serve Australian users.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and hacking news updates.



.png
)
