The Cyber police exposed a criminal group stealing 100 million hryvnias from Ukrainians under the guise of social security payments from the European Union.
According to the cyber police of Ukraine, the criminals created more than 400 phishing links to acquire the bank card data of citizens and appropriate money from their accounts. As a consequence, the criminal may face up to 15 years behind bars for what they have committed.
A dedicated cybercrime unit within the Ministry of Internal Affairs operating with police based in central Kyiv and specialists from the National Bank of Ukraine (NBU) worked to arrest nine individuals.
Phishing Links Used to Obtain Bank Data
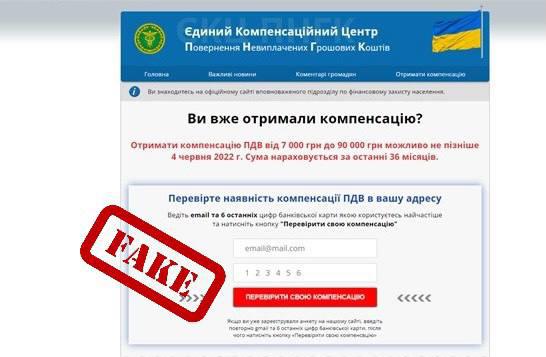
For obtaining the banking data of citizens, the nine individuals created and administered more than 400 fake web resources. Through the websites, Ukrainians were offered to form an application for the payment of financial assistance from the countries of the European Union.
Unknowingly, by using phishing links victims took surveys and entered their bank card details. Having received bank data, the attackers carried out unauthorized intervention in online banking and withdrew money from citizens’ accounts.
According to the NBU, “Criminals defrauded more than 5,000 citizens. The total amount of damages reaches more than 100 million hryvnias”.
The police searched the home of the suspects and seized computer equipment, mobile phones, bank cards, and money obtained through the illicit activities. The police also released a video during their raid on a suspect’s home.
Authorities Arrested the Cybercriminal Gang
The reports state that the perpetrators may face up to fifteen years in prison for multiple violations of Ukraine’s Criminal Code.
“Criminal proceedings have been opened under Part 3 of Art. 190 (Fraud), Part 5 of Art. 361 (Unauthorized interference in the work of information (automated), electronic communication, information and communication systems, electronic communication networks) of the Criminal Code of Ukraine”. “The issue of declaring suspicion and choosing precautionary measures for the persons involved are being resolved”, reads the advisory.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and hacking news updates.



.png
)
