BigBasket(Innovative Retail Concepts Private Limited) is India’s largest online food and grocery store. It is funded by Alibaba Group, Mirae Asset-Naver Asia Growth Fund, and therefore the UK government-owned CDC group.
“Recently BigBasket became victim to a data breach,” reported Cyble. Cyble has indexed the breached information at AmiBreached.com.
The Cybel Research team found the database of Big Basket for sale in a cyber-crime market during routine Dark web monitoring, being sold for over $40,000.
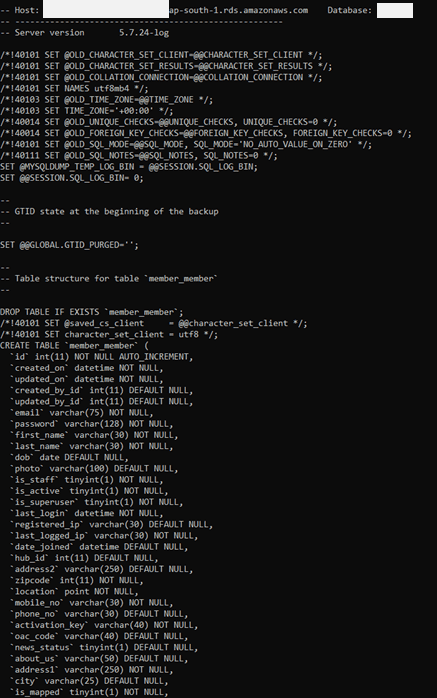
The leak contains a database portion; with the table name ‘member_member’. The size of the SQL file is ~ 15 GB, containing near to 20 Million user data, and is being sold for around Rs 30 lakh.
The database consists of names, email IDs, password hashes (potentially hashed OTPs), contact numbers (mobile and phone), addresses, date of birth, location, and IP addresses of login among many others. While Cyble has mentioned “passwords”, the corporate uses a one-time password sent through SMS which keeps on changing every time a user logs in.
Based upon the leaked records, it appears the breach occurred on October 14, 2020.
Cyble is disclosing the alleged data leak in the interest of the population impacted.

People who are concerned about their information exposure can register on Cyble’s data breach monitoring and notification platform, AmiBreached.com, to determine the risks at no cost.
The timeline of events:
- Oct 14, 2020 – The alleged breach occurred (screenshot below)
- Oct 30, 2020 – Cyble detected the breach
- Oct 31, 2020 – Cyble validated the breach through validation of the leaked data with BigBasket users/information
- Nov 1, 2020 – Cyble disclosed the breach to BigBasket management
- Nov 7, 2020 – Public disclosure
Here are a couple of ways to prevent cyber-attacks:
- Never click on unverified/unknown links
- Do not open untrusted email attachments
- Only download media from places you trust
- Never use unfamiliar USBs
- Use security software and keep it updated
- Backup your data regularly
- Keep passwords unique and unpredictable
- Keep Software and Systems up to date
- Train employees on Cyber Security
- Set up Firewall for your internet
- Take a Cyber Security assessment
- Update passwords regularly
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and hacking news updates.
Also Read
Shopify Data Breach – Two Rogue Employees Stole Customer Data
Truecaller Data Breach – 47.5 Million Indian Truecaller Records On Sale in Dark Web



