While using web browsers, there are security threats that, if not careful, can allow cybercriminals to take over the browser and steal information.
To ensure browser security for enterprises and individuals, steps must be taken to keep cyber criminals away. These steps involve having an active firewall and antivirus software, using a secured internet connection, and updating the browser.
In this article, you will learn some common browser security vulnerabilities you may encounter and the steps you should take to counter them.
Top Browser Security Vulnerabilities and How To Prevent Them
Below are some potential web browser security vulnerabilities you may witness and how to prevent them from happening.
Malicious Extensions and Plugins
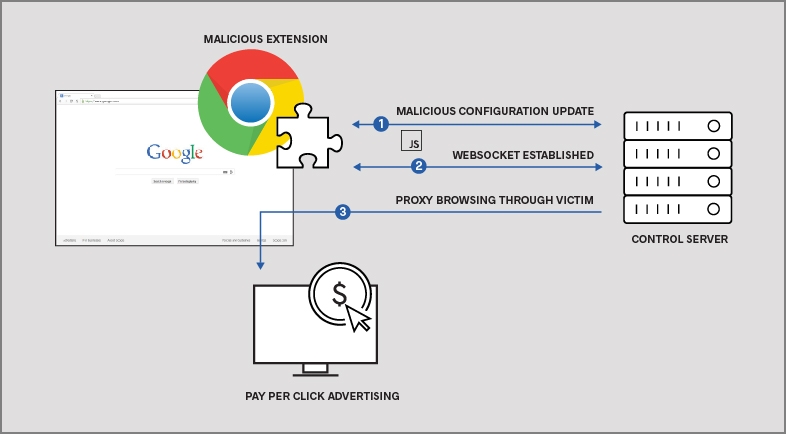
Browser extensions and plugins are in-app tools that help increase a web browser’s functionality. For instance, some extensions and plugins serve as antivirus software, YouTube video downloaders, and even ad blockers.
Extensions and plugins are quite popular because of how productive it makes web browsers to be. Many users have downloaded them within their browser, and sometimes they can be up to millions of users using one browser extension.
While extensions and plugins serve essential purposes within a web browser, they can be manipulated and used by cybercriminals to launch a cyber attack. Because of how some plugins work, they can access your browser history and sensitive information.
Cybercriminals create malicious browser extensions or inject existing browser plugins with viruses that get access to personal data. Many malicious browser plugins exist within popular browsers such as Chrome, Firefox, and Edge.
Prevention
The best way to prevent malicious browser extensions from accessing your data or any other information is by avoiding them altogether. However, many people need browser plugins for one activity or another, making removing plugins hard.
So the next step to preventing malicious plugins is installing those from reliable or official sources. They are plugins created by reputable and credible companies; try downloading from these sources only.
The next thing is to update the plugin frequently; updates help remove and patch up security vulnerabilities.
DNS Poisoning Attacks
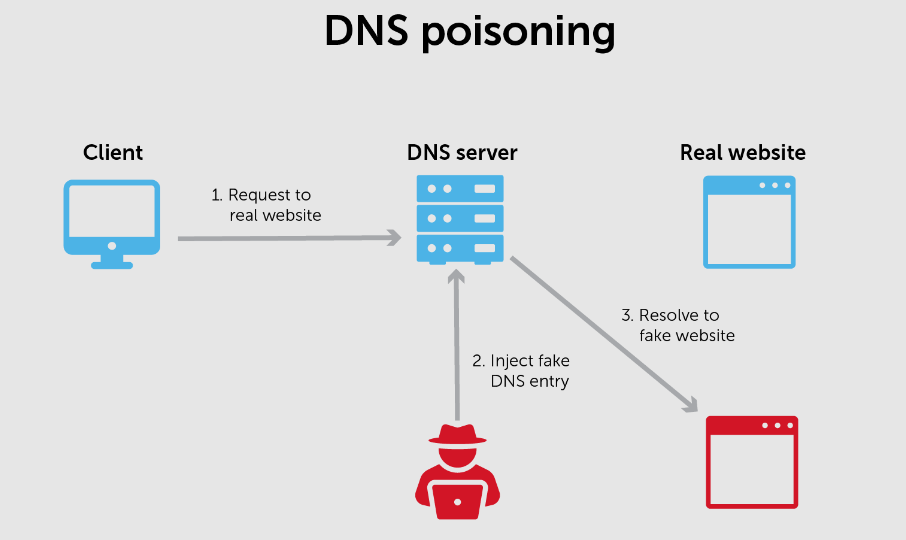
A DNS poisoning attack is a severe web browser security threat used by hackers to access users’ information. DNS servers translate human-readable website names into machine languages; for instance, they translate apple.com into 17.253.144.10.
Cybercriminals can try to poison the DNS, change the content, and then use another website to gain access to a user’s information. These cybercriminals try to launch an attack on the DNS cache (this is where all the DNS entries are stored) and make away with the information stored there.
When these cyber criminals gain access to the DNS cache, they provide compromised IP addresses for legitimate sites, thereby having total control over the website your browser displays. The major objective these cybercriminals have when they get a user over to a new site is to make them enter personal data such as financial information and passwords.
Prevention
To prevent DNS poisoning, ensure you have antivirus software running behind the scene so it can detect whenever an attack is launched.
Another step is to ensure that every website one visits have “https://” at the beginning of the website address; this step should be considered serious whenever you visit a financial website, your email, or any other website that requires your information.
You need to check this consistently because cybercriminals, even after a DNS poisoning, cannot fake the TLS/HTTPS certificates of the website.
SQL Injection
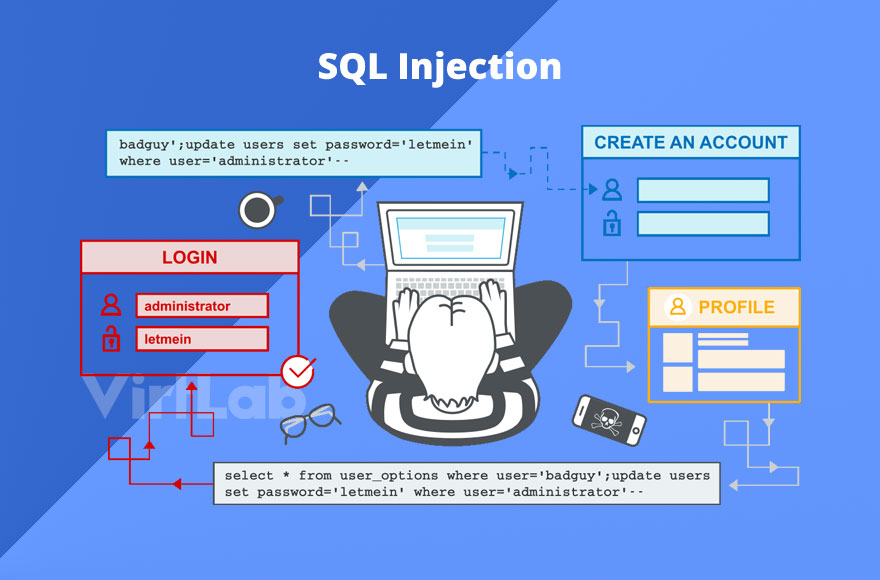
SQL injection is a browser threat that has existed for over a decade, and it is most effective when cyber criminals successfully launch one on a user’s browser. Those who use SQL injection do that on a website’s server; if successful, they access the website and modify the stored data.
The next step the cybercriminals take is to manipulate the website’s web forms, cookies, or HTTP posts with their malicious SQL injection. Whenever an unsuspecting user comes to the website and enters their information, these attackers can now steal the information from the website visitor.
Prevention
They are certain steps that can be taken to prevent the effectiveness or the ability of attackers to use the SQL injection technique. The first step to bring down this threat is to reduce the number of functions that can be executed using SQL commands on the browser.
Also, the user should turn on their firewalls and antivirus software to ensure that it stops cyber criminals from injecting any malicious SQL commands into the browser.
Broken Authentication
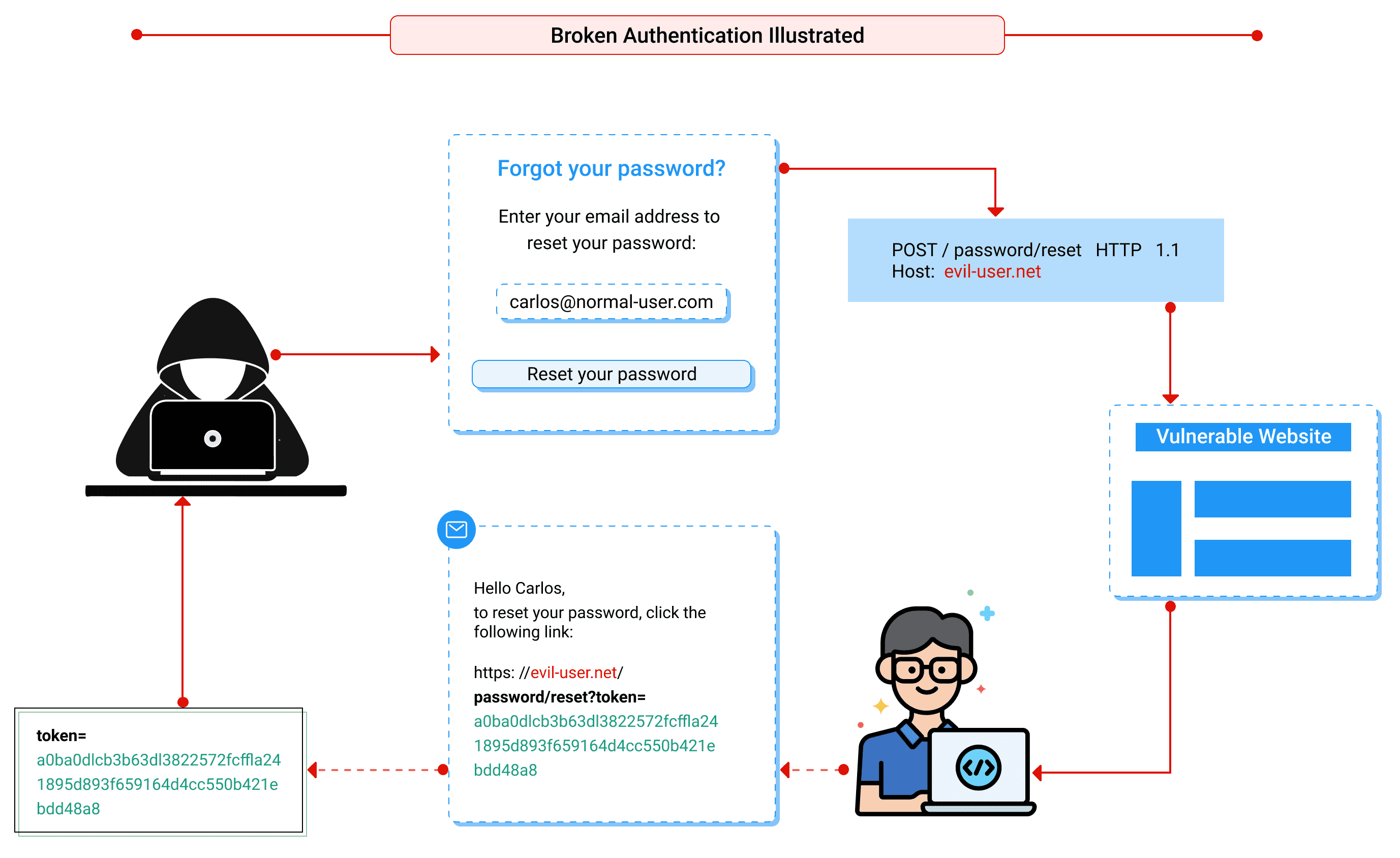
Broken Authentication is mostly executed on those websites that give out unique IDs to their visitors (which might be you).
Cybercriminals can use websites that issue unique IDs to get access to your information, assuming the session ID isn’t properly encrypted. So what these cybercriminals do is hijack your session using the unique ID, lock you out of the account, and can make purchases with your linked credit cards if there are any in your account.
Apart from using your credit card or any other linked payment method, they will get access to your information and steal them. This mostly occurs when the unique IDs are not properly encrypted, and the user is connected to an unprotected public network.
Prevention
The first step to preventing this type of security threat on your browser is to avoid using an internet connection that is unprotected. Even if you don’t have any options, you can use a VPN to protect your traffic, even on unprotected internet connections.
The next step is to avoid any website that does not have an SSL certificate; in other words, avoid any website that does not have “https://” on its website address.
Wrapping Up
A web browser serves an important purpose for users as it helps people to look up information online, communicate, and run a business empire online.
A web browser can get run over by security threats such as SQL injection, Broken authentication, malicious extensions, and DNS poisoning. However, instead of waiting for your browser to be overrun by these security threats, one can prevent it by taking the abovementioned steps.



.png
)
