Okta has issued a warning about the increasing prevalence of credential-stuffing attacks.
These attacks, which leverage stolen user credentials to gain unauthorized access to accounts, are facilitated by the widespread use of residential proxy services.
This alarming trend underscores the evolving challenges in cybersecurity and highlights the need for robust defensive measures.
The Rise of Credential Stuffing Attacks
From mid-March to late April 2024, cybersecurity teams at Duo Security, Cisco Talos, and Okta’s own Identity Threat Research team have observed a significant uptick in brute force and credential stuffing attacks.
Is Your Network Under Attack? - Read CISO’s Guide to Avoiding the Next Breach - Download Free Guide
These attacks are becoming more frequent and sophisticated, utilizing advanced tools and the anonymity provided by proxy services like TOR, NSOCKS, Luminati, and DataImpulse.
Credential stuffing attacks involve using large databases of usernames and passwords—acquired through previous data breaches, phishing, or malware campaigns—to attempt logins on various online platforms.
These recent attacks are particularly concerning because they rely on residential proxies, which use legitimate user devices to disguise the attackers’ origins, making the attacks more challenging to detect and trace.
Understanding Residential Proxies
Residential proxies are networks that route internet traffic through real users’ devices to anonymize the source.
These proxies can be a double-edged sword.
Integrate ANY.RUN in Your Company for Effective Malware Analysis
Are you from SOC, Threat Research, or DFIR departments? If so, you can join an online community of 400,000 independent security researchers:
- Real-time Detection
- Interactive Malware Analysis
- Easy to Learn by New Security Team members
- Get detailed reports with maximum data
- Set Up Virtual Machine in Linux & all Windows OS Versions
- Interact with Malware Safely
If you want to test all these features now with completely free access to the sandbox:
On the one hand, they provide valuable services like content localization and ad verification; conversely, they can be exploited for malicious activities like credential stuffing.
Deploying residential proxies often involves “proxyware” voluntarily installed by users or, more maliciously, through malware and compromised mobile apps.
This latter method enrolls devices into a botnet-like network without the owner’s knowledge, using them as conduits for illegal activities.
Okta’s Proactive Measures and Recommendations
In response to these threats, Okta has proactively enhanced its security features.
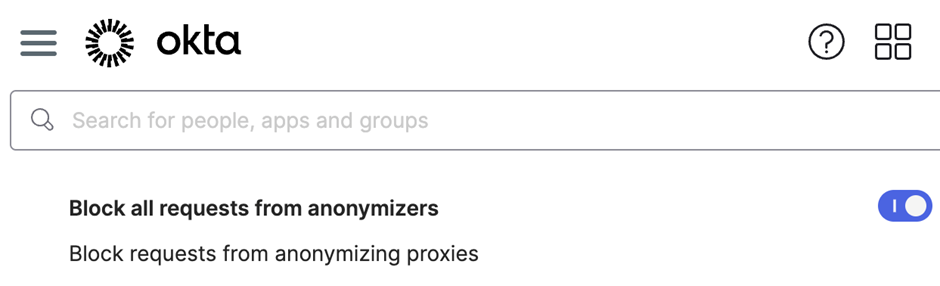
Earlier this year, Okta introduced a new capability in its Workforce Identity Cloud (WIC) and Customer Identity Solution (CIS) that detects and blocks requests from anonymizing services.
This feature is part of Okta’s broader strategy to implement default security measures that protect against such vulnerabilities.
For organizations using Okta’s services, the following measures are recommended:
- Enable the Early Access feature to block anonymizing proxies directly from the Okta Admin Console.
- Use Dynamic Zones for more granular control over which anonymizers are blocked.
- Consider upgrading the Okta Identity Engine for additional features like CAPTCHA challenges and passwordless authentication with Okta FastPass.
Furthermore, Okta advises all its customers to adopt a defense-in-depth approach.
This includes enabling ThreatInsight in log and enforce mode, which has proven effective in blocking IPs associated with high-volume credential-based attacks.
As cyber threats continue to evolve, staying ahead of attackers requires not only the use of advanced technological solutions but also a comprehensive understanding of the tactics employed by cybercriminals.
Okta’s ongoing efforts to enhance security and educate its users are vital in fighting credential stuffing and other forms of cyber aggression.
Combat Email Threats with Easy-to-Launch Phishing Simulations: Email Security Awareness Training -> Try Free Demo
.webp?w=696&resize=696,0&ssl=1)


.png
)
