A critical vulnerability in WhatsApp Lets hackers read the local file systems and allows to perform cross-site scripting in Mac and Windows platform when the users paired using WhatsApp for iPhone with desktops.
The vulnerability affected the WhatsApp Desktop prior to v0.3.9309 paired with WhatsApp for iPhone versions prior to 2.20.10.
It was initially reported by PerimeterX researcher Gal Weizman who have discovered this vulnerability and exploit it by altering the WhatsApp rich preview banner with a legitimate-looking crafted phishing link.
During his research, Gal experiment the discover an XSS vulnerability from an open-redirect using javascript: URIs, as a result, he gained a one-click Persistent-XSS.
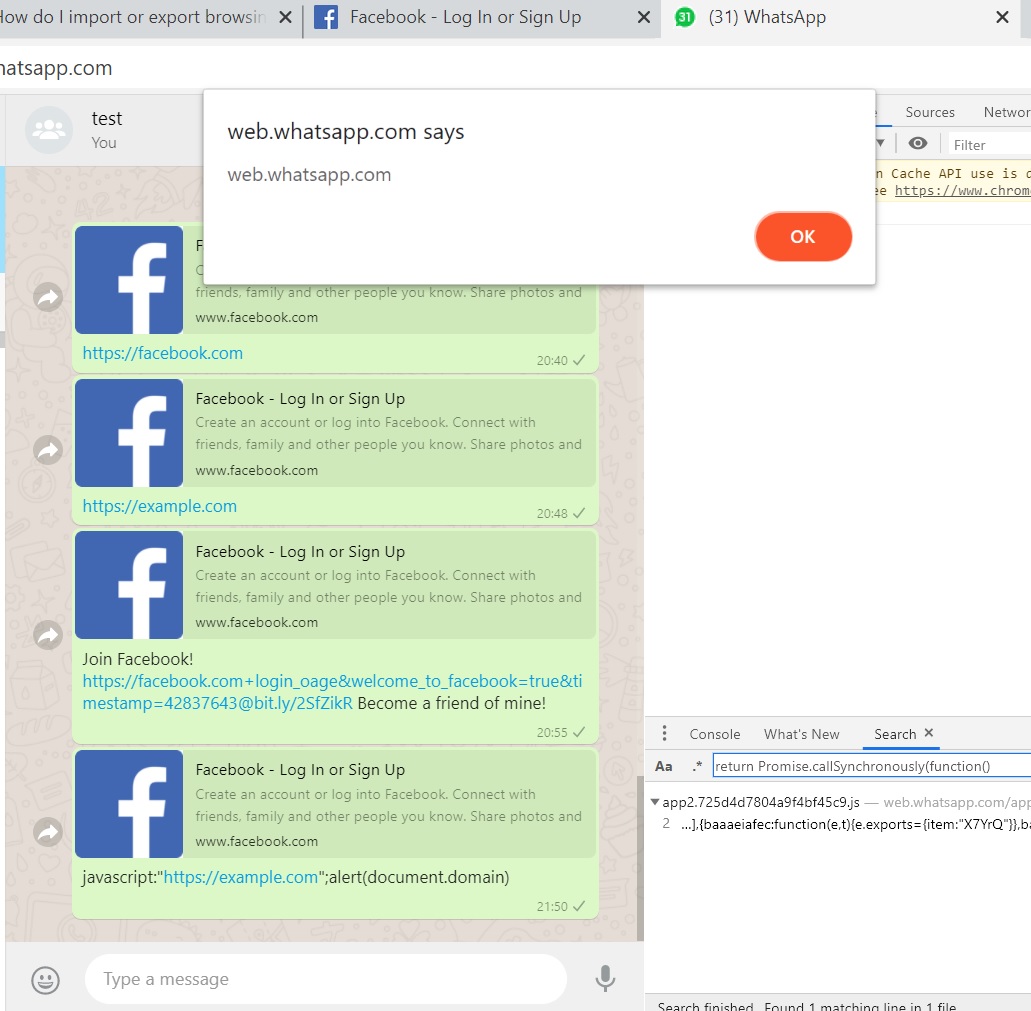
This potentially dangerous Cross-site scripting vulnerability can be triggered in both Mac/Windows desktop by sending a crafted URL to the WhatsApp desktop users.
Except for Chromium-based browsers that added a defense mechanism against javascript:, This vulnerability still existing int he other browsers such as Safari and Edge.
When the same crafted link opens by WhatsApp mobile users, WhatsApp apps normally open https://example.com instead of running the XSS since the native mobile apps are not allowing to run XSS on mobile.
To utilise the power of Persistent-XSS, the researcher attempt to bypassing CSP(Content security policy) rules in WhatsApp to inject the malicious Payload through a crafted message using Iframe.
As a result, the external payload was successfully fetched and executed in the context of WhatsApp!
According to Weizman “To achieve that, I simply use the XSS to load the iframe and then listen to the messages that are posted by different windows. I then use the iframe to post a message to the top window with the content of the external code.
The top window, where the XSS was executed, receives the message from the iframe, parses the external payload provided by it and executes it in its context (web.whatsapp.com).”
Reading From the File System on Mac/Windows
Bypassing the CSP rules, it allows an attacker to steal valuable information from the victim, load external payloads easily.
Through which, the researcher was able to access the local file system of Mac and Windows platform content of C:\Windows\System32\drivers\etc\hosts file.
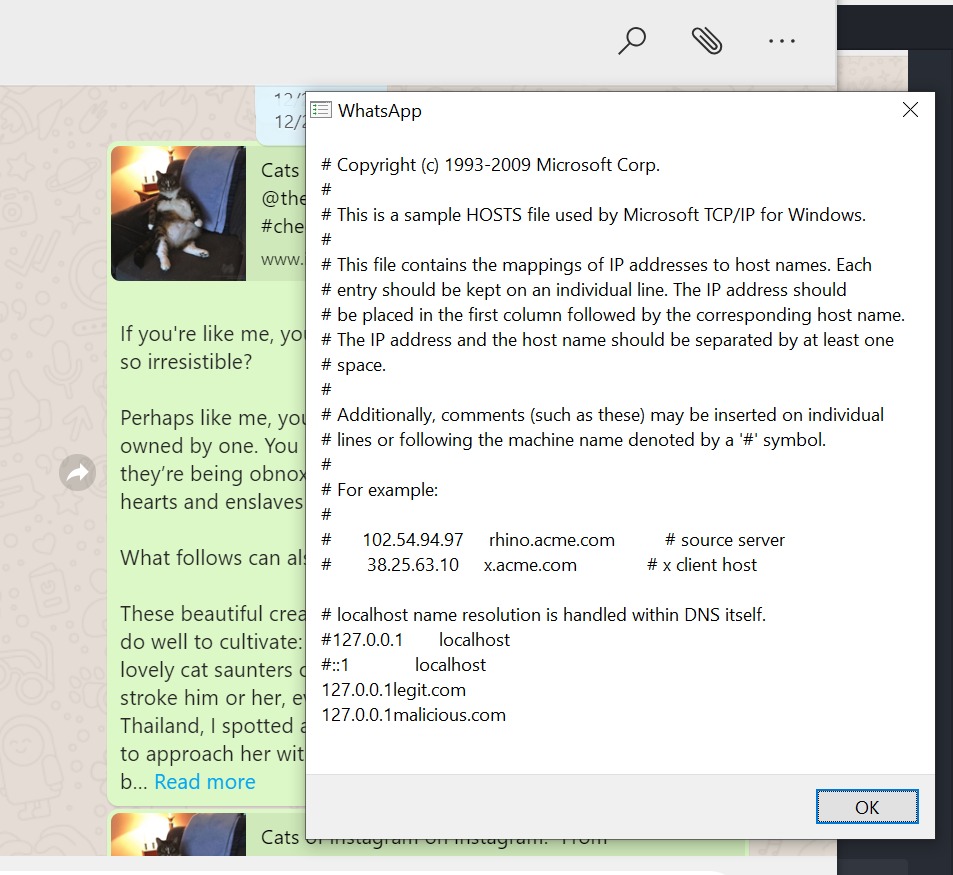
“All the way from a simple Open-Redirect, through a Persistent-XSS and a CSP-bypassing to a full Cross-Platform, Read from the File System plus potentially a Remote-Code-Execution” Weizman added in his Technical Writeup.
Facebook rewarded $12,500 to Weizman under responsible disclosure policy.
Facebook patched this vulnerability and released a new Desktop version. it can be tracked as “CVE-2019-1842“.”Exploiting the vulnerability requires the victim to click a link preview from a specially crafted text message” Facebook said.



.png
)
