Cybersecurity experts have uncovered a failed attempt by the notorious Russia-based Turla Advanced Persistent Threat (APT) group to infiltrate an Albanian organization.
This incident is part of a broader cyber espionage campaign targeting European countries, with Poland also falling victim to these sophisticated attacks.
The discovery aligns with the ongoing geopolitical tensions and highlights state-aligned actors’ escalating cyber warfare tactics.
Are you from the SOC and DFIR Teams? – Analyse linux Malware Incidents & get live Access with ANY.RUN -> Start Now for Free.
The Failed Infiltration
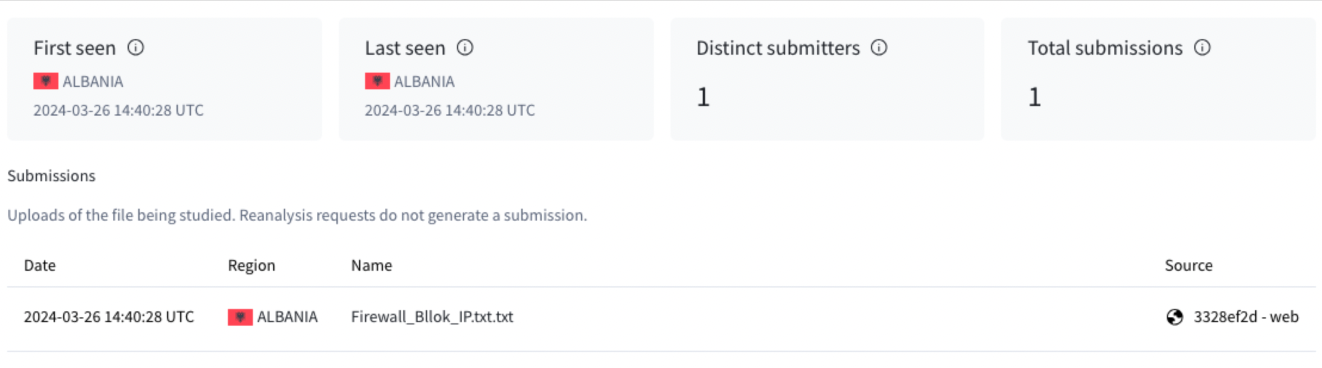
On March 26, a user located in Albania uploaded a file to the VirusTotal web interface, which revealed the attempted breach in Albania.
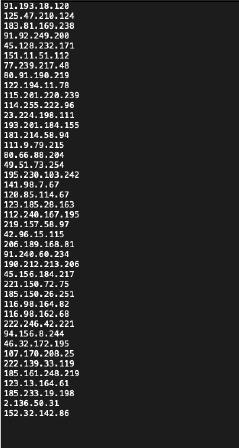
The file, named “Firewall_Bllok_IP.txt.txt,” contained a list of IP addresses, including the address 91[.]193[.]18[.]120.
Cisco Talos has flagged this particular IP as a command and control server associated with the “TinyTurla-NG” (TTNG) backdoor, marking it as a key indicator of compromise.
with ”bllok”(block) written in Albanian.
Analysis of the file confirmed its authenticity. Multiple antivirus vendors recognized all listed IP addresses as malicious.
Turla APT’s Expanding Campaign
The Turla APT group, known for its sophisticated cyber espionage operations, has historically targeted organizations with links to government sectors across Baltic and Eastern European countries.
The recent activities in Albania and Poland underscore the group’s ongoing efforts to gather intelligence and exert influence amidst the broader context of the war in Ukraine.
These incidents provide crucial insights into the possible scope of Russia-based APT operations, which continue to pose a significant threat to European security.
Implications for European Security
The targeting of Albania by the Turla APT group is a stark reminder of the persistent cyber threats facing European organizations.
These entities often possess valuable information and maintain critical infrastructure, so they are high-value targets for espionage activities.
The incident underscores the need for heightened cybersecurity measures and international cooperation to counteract the sophisticated tactics employed by state-aligned APT groups.
Looking Ahead
The cybersecurity community remains vigilant as the Turla APT group continues to refine its tactics and target European organizations.
The failed attempt in Albania is a critical reminder of the ongoing cyber warfare landscape, where information is a valuable commodity, and security is perpetually at risk.
With the geopolitical tensions showing no signs of abating, European organizations must remain on high alert and prioritize cybersecurity to thwart future espionage attempts by state-aligned actors.
Secure your emails in a heartbeat! To find your ideal email security vendor, Take a Free 30-Second Assessment.



.png
)
