Major U.S. data center provider CyrusOne, hit by Sodinokibi ransomware, impacts six of their managed service customers. The Sodinokibi ransomware was first identified on April 17, 2019.
The ransomware used to encrypt all the files in the disk except the one listed as the configuration file. REvil (Sodinokibi) ransomware previously hit several service providers, local governments and businesses.
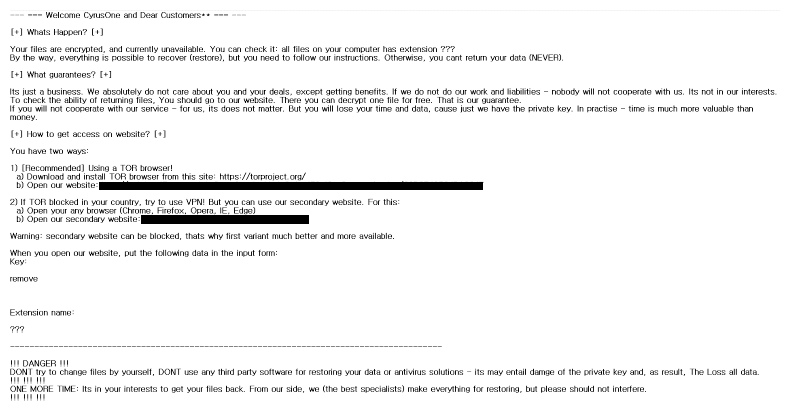
CyrusOne Ransomware Attack
According to the ZDNet report, the attack took place on Wednesday and created availability issues for six of their customers that are located in its New York data center as the ransomware encrypts certain devices in the network.
It is still unknown how the ransomware managed to breach the CyrusOne network, the ransomware was known to distribute via exploit kits, scan-and-exploit techniques, RDP servers, and backdoored software installers.
The ransomware use to target following file extensions .jpg, .jpeg, .raw, .tif, .png, .bmp, .3dm, .max, .accdb, .db, .mdb, .dwg, .dxf, .cpp, .cs, .h, ,php, .asp, .rb, .java, .aaf, .aep, .aepx, .plb, .prel, .aet, .ppj, .gif, and .psd.
The company said that other data center “colocation services, including IX and IP Network Services, are not involved in this incident. Our investigation is on-going and we are working closely with third-party experts to address this matter.”
CyrusOne has data centers in more than 30 countries across the United States, China, London, Singapore and has more than 1,000 customers.
The ZDNet report states that the ransomware attack is a targeted one against the data center which hosts IT infrastructure for companies. The threat actors demanding ransom payment for file recovery.
CyrusOne managed to respond to the attack by restoring the data from the backup servers. The company has not yet released any public statements related to the issue.
Last November SmarterASP.NET, a popular ASP.NET hosting provider hit by a ransomware attack, all the hosted websites including their company website went down.
The Ransomware attack is quite common nowadays since malicious software spreading everywhere through various mediums.
There are ways to prevent ransomware and protect yourself. In this article you will find straight-forward expert tips, so you never become a victim of Ransomware Attack.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and hacking news updates



