Cloud security researchers have uncovered alarming trends in identity compromises within Amazon Web Services (AWS) environments.
Among the most prolific threat actors is a group dubbed “EC2 Grouper,” known for exploiting compromised credentials to carry out sophisticated attacks using AWS tools.
Over the past couple of years, EC2 Grouper has been active in dozens of customer environments, marking them as a persistent threat to cloud infrastructures.
Tactics and Techniques
EC2 Grouper leverages AWS PowerShell tools to automate their attacks, with their user agent providing a key early indicator of their activities.
Initially consistent over several years, their user agent recently evolved to include unusual hash (#) characters, signaling potential countermeasures against traditional detection methods.
Other identifying markers include the creation of security groups with systematic naming conventions such as “ec2group,” suffixed with sequential numbers (e.g., ec2group12345).
These groups are created using the CreateSecurityGroup API, a tactic enabling lateral movement and potential resource hijacking.
The group’s modus operandi involves gathering intelligence about cloud environments through APIs, including:
- DescribeInstanceTypes: To inventory EC2 types.
- DescribeRegions: To identify available regions for resources.
- DescribeVpcs, DescribeSecurityGroups, and DescribeInstances: To map the customer’s environment.
- RunInstances: To launch new EC2 instances.
Interestingly, EC2 Grouper often refrains from configuring inbound access using the AuthorizeSecurityGroupIngress API.
Instead, they occasionally employ APIs like CreateInternetGateway and CreateVpc to establish remote access pathways.
EC2 Grouper’s attacks are typically fueled by compromised AWS credentials, often originating from code repositories where developers accidentally expose sensitive keys.
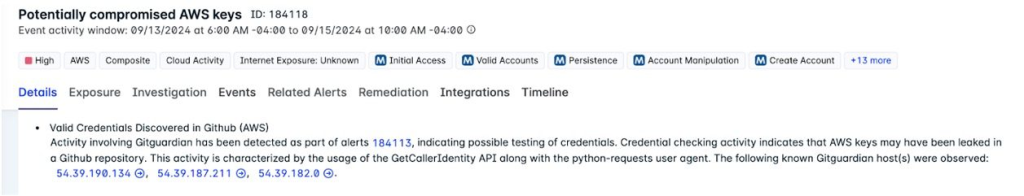
According to the Fortinet reports, public repositories have been a hotbed for such incidents, with the group taking advantage of credentials leaked through platforms like GitHub.
Detecting EC2 Grouper’s illicit activities hinges on correlating multiple signals. While atomic indicators like user agents or security group conventions can assist in attribution, they alone are insufficient for reliable detection due to their transient nature. Key defensive strategies include:
- Secret Scanning Services: Utilizing tools like GitGuardian and GitHub’s secret scanning to detect exposed credentials.
- Composite Alerts: Correlating various signals, such as unusual API sequences, privilege escalation attempts, and anomalous environment behavior.
- Anomaly Detection: Identifying deviations in cloud usage patterns to flag potential reconnaissance or malicious actions.
The rise of attackers like EC2 Grouper underlines the critical need for robust cloud security practices.
While identifying malicious use of compromised credentials remains challenging, advanced detection mechanisms, supplemented by tools like Lacework FortiCNAPP, can provide comprehensive protection.
As attackers continue to refine their techniques, organizations must prioritize proactive monitoring, credential hygiene, and anomaly detection to safeguard their cloud environments.
Investigate Real-World Malicious Links, Malware & Phishing Attacks With ANY.RUN – Try for Free



.png
)
