New Mirai level Botnet Echobot using 26 different exploits for the infection vectors that leveraging the vulnerabilities in Oracle, D-Link, Dell, LINKSYS, REALTEK, Vmware applications and take control of it.
Since 2016, Mirai variant spreading via hundreds of campaigns, similarly researchers from Palo Alto recently uncovered the latest variant contains a total of 18 exploits, 8 of which are new to Mirai.
A researcher from Akamai discovered this updated Echobot variant binary in honeypot system where attackers using 26 different exploits to spread the botnet.
Most of the exploits that were being used for this campaign leverages the command execution vulnerabilities that affected various network devices.
New campaign of Echobot adds the various new targets than the old version of following,

Some of the exploits found in this campaign are ten years old that targets the network devices and is believed to be never patched by the respective vendors.
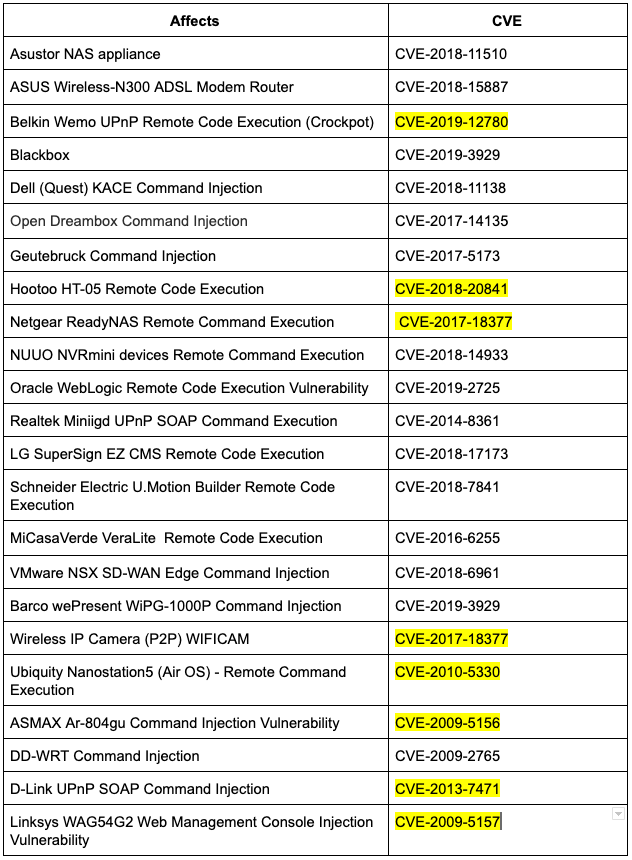
Also, few vulnerabilities that are being exploited in wide has no CVE assigned, and the following table indicates the list of each exploit and assigned CVE.
A researcher from Akamai said, “What I found the most interesting, and not so surprising, is the inclusion of cross-application vulnerabilities. For example, rather than sticking to devices with embedded OSs like routers, cameras, and DVRs, IoT botnets are now using vulnerabilities in enterprise web (Oracle WebLogic) and networking software (VMware SD-WAN) to infect targets and propagate malware.”
Based on the binary comparison using strings, Echobot commonly shared attack code typically derived from the Mirai botnet, but the infection vector of the exploits are different.
There are two commands and control servers are uncovered under the domains akumaiotsolutions.pw and akuma.pw and the DNS data have shown that the records pointing to servers in Italy (80.211.224.232, 80.211.168.74) and the US (198.54.117.200).
Attackers not only rely on new vulnerabilities that target the IoT devices but also focusing on enterprise networks and new exploits they’ve added are older and have remained unpatched by the vendor.
“This is an interesting tactic as these systems if found have remained vulnerable for years and will probably remain vulnerable for many more. Also, there are not just new exploitation vectors to examine but attack vectors as well.” Researcher said.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity updates also you can take the Best Cybersecurity courses online to keep yourself updated.



.png
)
