Security researchers uncovered a new attack dubbed Kraken that uses injected its payload into the Windows Error Reporting service to evade detection.
The WerFault.exe is a service that shows some error happened with the operating system, Windows features, or applications, victims would assume some error happen, but attackers stealthy execute malware using the process.
Fileless Malware Attack
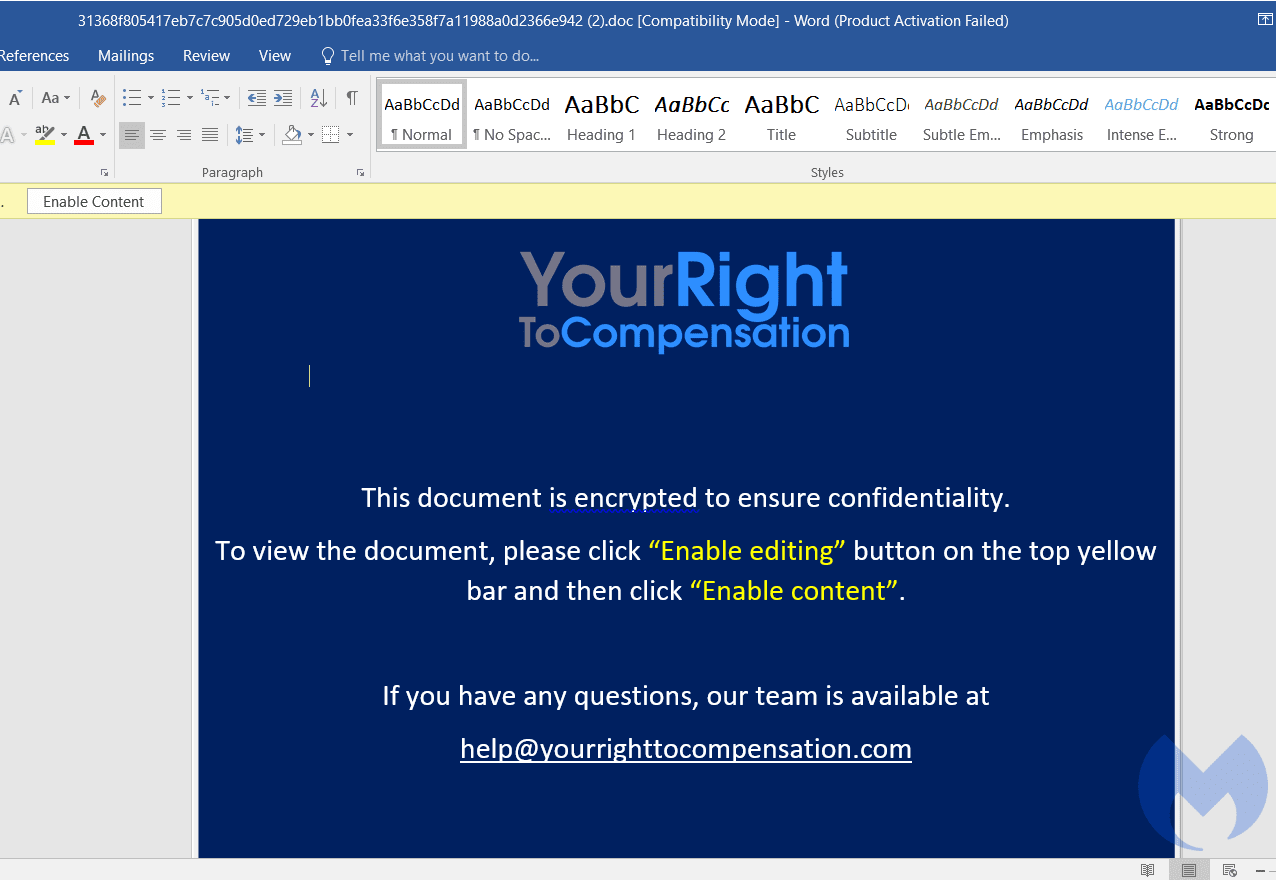
Security researchers from Malwarebytes observed a new attack with a zip file containing a malicious document dubbed “Compensation manual.doc” and it has an image tag that points to the website “yourrighttocompensation[.]com”.
Inside the malicious document file, it includes a modified version of CactusTorch(shellcode launcher) VBA module that leverages the DotNetToJscript technique to load a .Net compiled binary into memory and execute it from VBScript.
Once it is opened by a victim it will execute the CactusTorch macro that loads the NET payload straight directly in the windows device’s memory.
The binary is executed on the window’s memory and injects embedded shellcode into the Windows process. As the binary executed on windows memory it won’t leave any traces on the hard disk.
The new maliciously created Windows Error Reporting service will before some anti-analysis checks such as not running in an analysis/sandbox environment or a debugger.
Once it feels safe after anti-analysis it decrypts and loads the final payload int he maliciously created Windows Error Reporting service. The payload is hosted on the website asia-kotoba[.]net in the name of favicon.
At the time of the report, the target URL was down, so that Malwarebytes unable to retrieve this shellcode for further analysis.
Researchers believe the attack relates to APT32, but not having enough evidence to attribute this attack.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and hacking news updates.
Also Read
GitHub Launches Code Scanning Tool to Find Security Vulnerabilities – Available for All Users
Beware of the New Critical Zerologon Vulnerability in The Windows Server



.png
)
