Security researchers from CyberARK discovered security bugs with anti-malware software that allows attackers to escalate privileges on an infected machine.
Bugs with anti-malware pose high risks than other applications, as it has high privileges that let attackers run malware at elevated privileges.
Cause for the Flaw
According to researchers, the main cause of the bug is with the default DACLs of the C:\ProgramData directory. On Windows used by the application to store data.
This process is not tied to a specific user, any user has read/write permissions on ProgramData instead of the %LocalAppData%, which is accessible by the current logged in user.
“So, if a non-privileged process created a directory in ProgramData that would be later used by a privileged process, we might have a security issue on our hands,” reads the blog post.
Researchers analyzed Avira’s AV which has two processes non-privileged & privileged process hat write to the same log file.

An attacker could exploit the privileged process to delete the file and create a symlink that would point to any arbitrary file on the target system with malicious content.
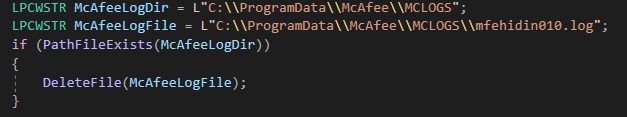
Also, the researchers analyzed McAfee antivirus which creates the “McAfee” folder, under the standard user control, but the local user could gain elevated permissions through a symlink attack.
“he implications of these bugs are often full privilege escalation of the local system. Due to the high privilege level of security products, an error in them could help malware to sustain its foothold and cause more damage to the organization.”
Following are the vulnerabilities discovered
- Kaspersky CVE-2020-25045, CVE-2020-25044, CVE-2020-25043
- McAfee CVE-2020-7250, CVE-2020-7310
- Symantec CVE-2019-19548
- Fortinet CVE-2020-9290
- Checkpoint CVE-2019-8452
- Trend Micro CVE-2019-19688, CVE-2019-19689 +3
- Avira – CVE-2020-13903
- Microsoft-CVE-2019-1161
- Avast + F-Secure – Waiting for Mitre
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and hacking news updates.
Also Read
GitHub Launches Code Scanning Tool to Find Security Vulnerabilities – Available for All Users
Beware of the New Critical Zerologon Vulnerability in The Windows Server



.png
)
