Free Antivirus apps on Google play asks users to explicitly agree for dangerous permissions that they are not required to operate. Even if you are installing an antivirus app, you should be careful with permission.
While installing any app from Google play, make sure it is a well-known brand and the permission is required to operate on. Here is a list of some best antivirus apps for Android devices.
Free Antivirus apps – Dangerous Permissions
Security researchers from VPNPro spotted six Antivirus app’s that asking for dangerous permissions such as access to the microphone, camera, making calls, reading and writing files, and much more.
The following are the six apps that downloaded more than 2 billion times requesting dangerous permissions.
- Security Master – Antivirus, VPN, AppLock, Booster(500 Million)
- Antivirus Free 2019 – Scan & Remove Virus, Cleaner (10 Million)
- Virus Cleaner 2019 – Antivirus, Cleaner & Booster (50 Million)
- Virus Cleaner, Antivirus, Cleaner (MAX Security) (50 Million)
- Super Phone Cleaner: Virus Cleaner, Phone Cleaner (50 Million)
- Clean Master – Antivirus, Applock & Cleaner (1 billion)
These apps are highly popular and they are potentially dangerous, by having explicit permissions these apps can track, can open the camera and access phone without user consent.
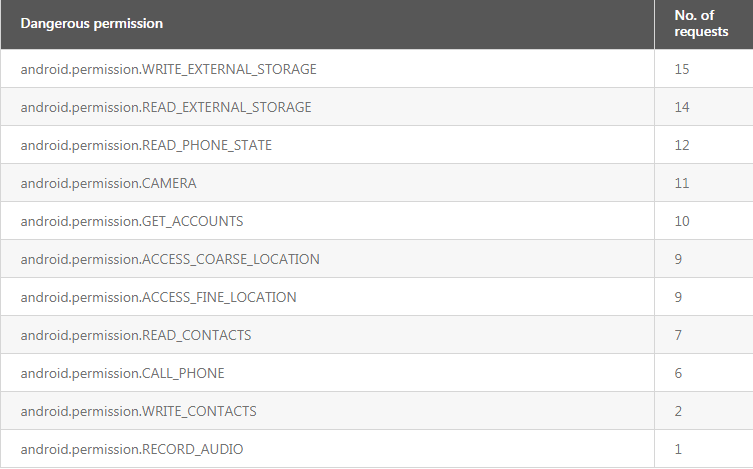
Following are the dangerous permission requested
“Even though these apps have been found guilty of these malicious activities in the past, they’re still available on Google Play and amassing millions of installs every month,” reads VPNpro report.
The research conducted against 15 popular free antivirus apps from Google plays to check which type of permissions they are looking for. Out of 15 apps, 12 apps belong to developers based in China or Hong Kong.
Another interesting thing is that three developers (ONE App Ltd, Hyper Speed, and Smooth Apps Studio) share the same address, all the three including another developer removed from Google play now.
Specifically, these apps are looking for ACCESS_COARSE_LOCATION and ACCESS_FINE_LOCATION, by having this permission they can closely track the user’s location, these data are sold to data brokers by app developers.
These illicit apps are huge privacy threats for users, a detailed analysis to be done before installing an app.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and hacking news updates



.png
)
