Researchers discovered a new wave of FTCODE ransomware campaign that steal browsers login credentials and Encrypt files in Windows systems.
FTCODE ransomware was first observed in 2013, it uses the Windows PowerShell program to perform file encryption.
The ransomware resurfaced again starting from last year September, according to Certego analysis of the FTCODE ransomware, it is still in active development.
Threat actors behind the ransomware strain use weaponized word documents to deliver the ransomware. If the victim opens the documents and disables protected view then it triggers the execution of the malicious macro.
Once executed the macro runs a PowerShell process to download a piece of Powershell code which is FTCODE and save the request only in memory, in an attempt to avoid antivirus detection.
FTCODE Ransomware New Version
Researchers from Zscaler observed a new version of FTCODE ransomware 1117.1, that contains different infection method and password-stealing capabilities.
The ransomware distributed through spam Emails, and the macro documents containing links to VBScripts which further downloads the PowerShell script known as FTCODE ransomware.
To trick the users the script first downloads a decoy document, and in the background, it downloads and runs the run the ransomware.
FTCODE ensures persistence by creating a shortcut file called windowsIndexingService.lnk in the victim’s startup folder, so it will get executed every time system boots.
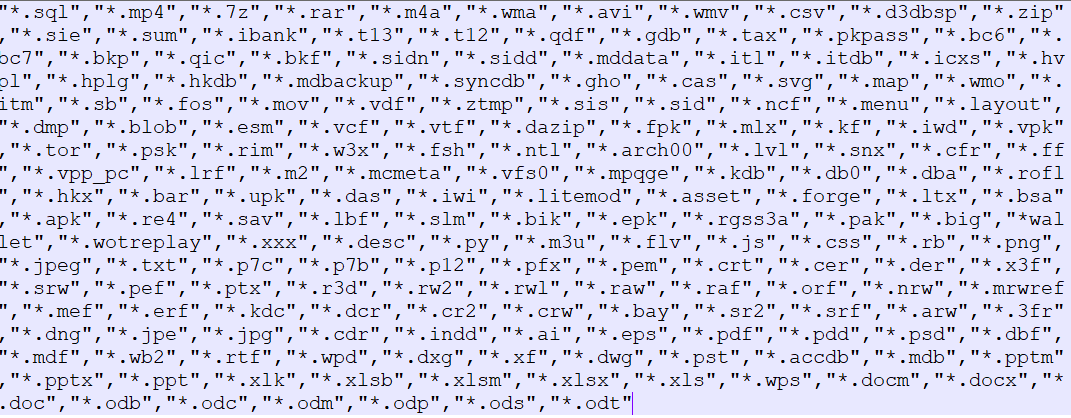
Before encryption it checks in all drives to see at least 50kb of free space is left, here are the extensions it encrypts.
Once the encryption completed it drops a ransom note “READ_ME_NOW.htm” in the directory of the encrypted files.
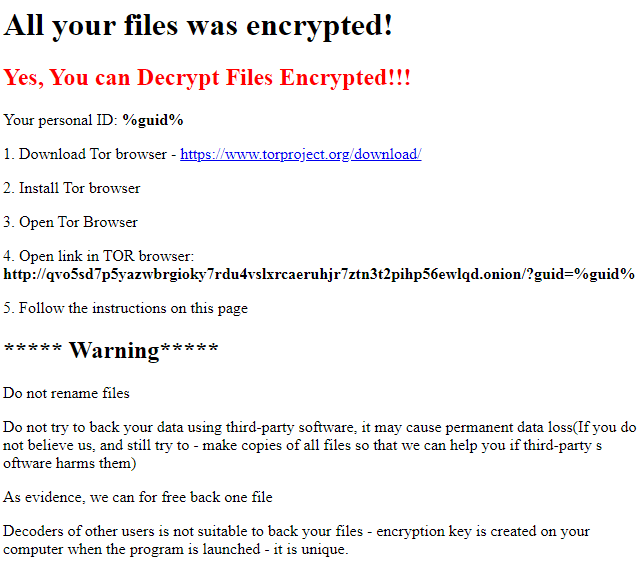
The ransom note directs a Tor website for victims to make the payment, the Tor site contains a Bitcoin address and asks victim’s to pay $500 to recover files.

Some users reported that “someone paid the ransom and did not get the decryptor.”
Password Stealer
The new version of the ransomware includes password-stealing capability, which is not present with the older versions.
It steals the login credentials from browsers and email clients:
- Internet Explorer
- Mozilla Firefox
- Mozilla Thunderbird
- Google Chrome
- Microsoft Outlook
FTCODE Ransomware is evolving, in a short period, multiple versions were spotted. At the moment there is no decryptor available for the ransomware strain.
IOCs:
Md5
- d597ea78067725ae05a3432a9088caae
- c8a214f432fc9d74c913c02e7918fc0
- f96253923e833362ecac97729d528f8c
- cc0f64afa3101809b549cc5630bbd948
- 328ce454698307f976baa909e5c646c7
- 71a8d8c0543a99b8791e1cfaeeeb9211
- f0aa45bb9dd09cfac9d93427a8f5c72c
- d6da191bfc5966dd4262376603d4e8c1
- cc5946ce893ff37ace8de210923467a2
- 7f5bb4529b95a872a916cc24b155c4cc
- edd5fbe846fa51f3b555185627d0d6c5
- a2e88f9486cc838eae038a8ba32352f3
- eab63ee2434417bc46466df07dc6b5b5
- fd46c05b99d00e11d34b93eae2c7ff2b
- 98d2;221445c2c8528cef06e4ef3c9e36
Also Read: Ransomware Attack Response and Mitigation Checklist



.png
)
