A new flaw with Microsoft Teams Updater allows attackers to install and run malware from a remote location Using Living off the Land Technique.
The issue was first disclosed last year and it relies on using the ‘update’ command to run the arbitrary binary code with the context of the current user.
Microsoft Teams Updater Flaw
The flaw discovered earlier by reverse engineer Reegun Richard in 2019, he revisited the problem this year with the solution implemented by Microsoft.
“The patch previously provided for Teams was to restrict its ability to update via a URL. Instead, the updater allows local connections via a share or local folder for product updates” – Reegun Jayapaul from Trustwave said.
He found that the patch can be easily bypassed by pointing to a remote SMB share and it can be used for lateral movement.
With the last patch of the Microsoft Teams update it allows only local network paths \server\ to access and update and blocks the “http/s”, “:”, “/” and port numbers in the updater URL.
How an Attacker can Exploit this
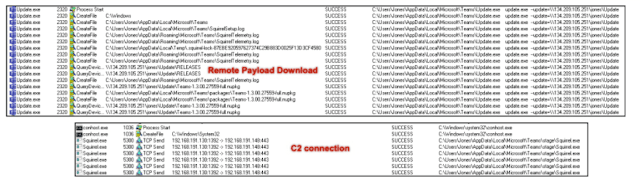
Attackers need to place the file inside the network in an open shared folder. Then the attackers need to access the payload from that share to the victim machine.
Attackers also can exploit the bug remotely by setting up a Samba server for remote public access, and by initiating the command execution a payload can be downloaded remotely and executed directly from Microsoft Teams Updater “Update.exe”.
Steps to create payload, requirements and technical details can be found here, Trustwave has reported the issue to Microsoft.
Microsoft said that “Thank you again for submitting this issue to Microsoft. We determined that this behavior is considered to be by design as “we cannot restrict SMB source for –update because we have customers that rely on this (e.g. folder redirection).”
Trustwave recommends SMB connections especially from the Microsoft Teams updater update.exe or filters SMB connections entirely.
A lot of businesses have transitioned to a remote workforce due to the current health crisis. To protect your business and your remote teams here are some of the best practices.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and hacking news updates.
Also Read
Hackers Hijack Microsoft Teams Accounts Using a Single Weaponized GIF Image
Beware of Fake Microsoft Teams Notifications Aimed to Steal Employees Passwords



.png
)
