Recent cybersecurity research has uncovered a concerning trend where hackers are exploiting Microsoft Teams to gain remote access to victim systems.
Utilizing sophisticated social engineering tactics, these malicious actors pose as legitimate employees or trusted contacts, leveraging video calls on Microsoft Teams to deceive users into downloading harmful software.
The attack typically begins with an onslaught of phishing emails designed to create confusion or urgency.
Once the victim is primed, the attacker initiates a Microsoft Teams call, impersonating an employee from a known company or a trusted external supplier.
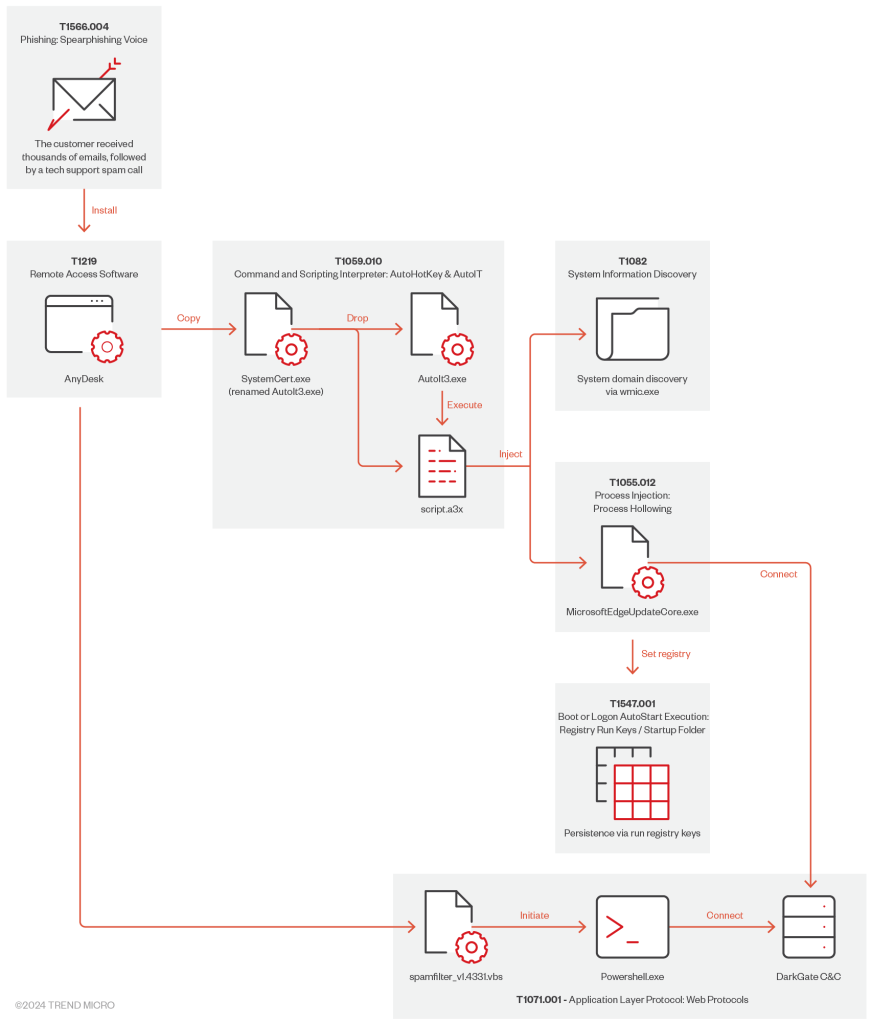
During this call, the fraudulent representative instructs the user to download remote desktop software, supposedly for troubleshooting purposes.
In a notable case, the attacker initially attempted to guide the victim to download a Microsoft Remote Support application, but after a failed installation, they instructed the use of AnyDesk instead.
This remote access tool, once installed, became the vector for deploying DarkGate malware, allowing the attacker to seize control over the victim’s computer.
2024 MITRE ATT&CK Evaluation Results Released for SMEs & MSPs -> Download Free Guide
The Role of DarkGate Malware
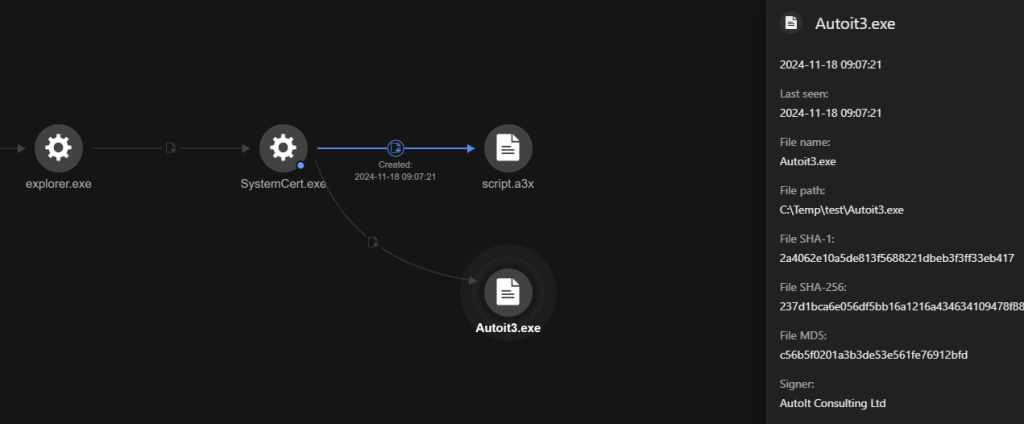
DarkGate malware is a formidable threat distributed via an AutoIt script. Its capabilities include executing remote commands, gathering sensitive system information, and establishing a connection with a command-and-control server.
The malware is executed seconds after AnyDesk is installed, where commands are issued to run it as a local service with elevated privileges.
processCmd: "C:\Windows\System32\cmd.exe"
eventSubId: 2 - TELEMETRY_PROCESS_CREATE
objectFilePath: c:\windows\system32\rundll32.exe
objectCmd: rundll32.exe SafeStore.dll,epaas_request_cloneThis access grants the attacker the ability to perform various malicious actions, including injecting additional malware into processes and manipulating network configurations.
The sophisticated execution flow even allows the malware to load into legitimate system processes to obfuscate its presence and activity.
To defend against these advanced threats, organizations must adopt comprehensive security strategies.
Firstly, employee training is crucial, focusing on the recognition of phishing attempts and the dangers of unsolicited support calls.
A well-informed workforce can significantly reduce the likelihood of successful social engineering attacks. Secondly, implementing strict verification protocols for third-party interactions can prevent unauthorized access.
This includes verifying the identity of any external support personnel. Additionally, organizations should restrict the use of remote desktop tools, permitting only those applications that have been thoroughly vetted and approved.
The enforcement of multi-factor authentication (MFA) on remote access tools offers an additional layer of defense, requiring multiple forms of verification to access systems, as per a report by Trend Micro.
The misuse of Microsoft Teams as a platform for cyberattacks underscores the evolving landscape of cybersecurity threats.
As communication tools become integral to business operations, they also present new vulnerabilities for exploitation.
To counter these emerging threats, organizations must enhance their security measures, combining employee education with advanced technological defenses.
Investigate Real-World Malicious Links, Malware & Phishing Attacks With ANY.RUN – Try for Free



.png
)
