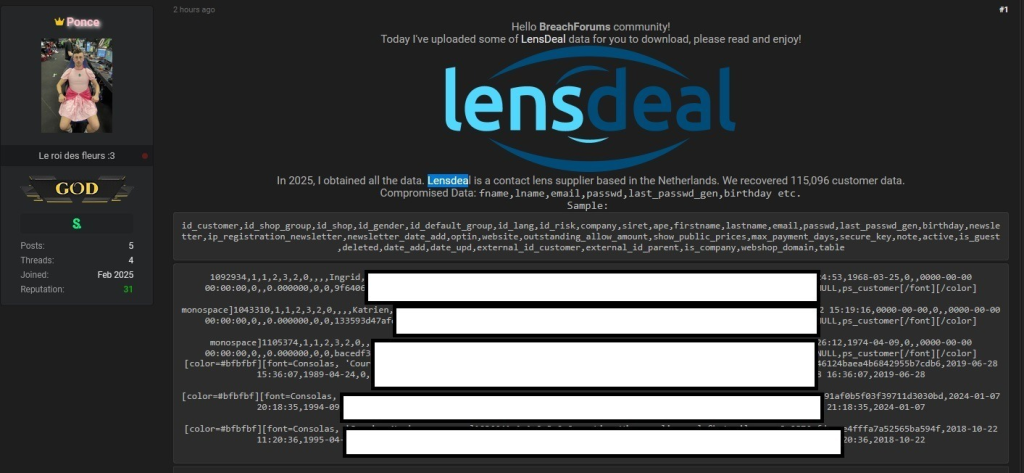
A major data breach involving LensDeal, a Netherlands-based contact lens supplier, has reportedly exposed the personal information of over 100,000 customers.
According to the Cyber Security Hub post, the breach affects 115,096 individuals and includes sensitive details such as full names, birthdates, email addresses, hashed passwords, IP addresses, and in some cases, company details.
Some customer records date back several years, while others are as recent as early 2025, hinting that the breach itself may be recent and far-reaching.
The data, which was allegedly stolen from LensDeal’s internal systems, has not yet been verified.
However, cybersecurity experts analyzing samples shared in the forum have noted that the data’s structure and formatting strongly suggest validity.
LensDeal has yet to issue an official statement on the matter, leaving customers and privacy advocates in the dark about the company’s response.
A Serious Threat to Privacy
The exposed information poses a significant risk to the affected individuals, according to cybersecurity specialists.
The combination of names, contact details, and other personal information creates an ideal scenario for malicious actors to conduct phishing attacks, identity theft, or unauthorized account access.
Experts are urging LensDeal customers to respond proactively. Immediate steps include:
- Changing account passwords: Customers should also avoid reusing old passwords and adopt stronger, unique ones.
- Monitoring financial and online accounts: Any suspicious activity should be reported immediately to service providers or relevant authorities.
- Staying vigilant: Customers should be wary of emails or messages requesting personal or financial information, especially those masquerading as LensDeal.
If confirmed, the LensDeal breach will add to the growing trend of European e-commerce platforms becoming targets for hackers.
With cybercriminals increasingly exploiting vulnerabilities in online retailers, including small and medium-sized enterprises, consumers’ data often becomes collateral damage.
The incident underscores the urgent need for businesses to adopt robust cybersecurity measures, such as encrypted customer databases and timely security audits.
Customers, too, must remain informed and cautious about the online platforms they engage with.
As the situation develops, LensDeal’s silence has drawn criticism, with users and experts calling for transparency from the company.
Authorities and independent groups are expected to investigate the breach further to verify its scope and legitimacy.
Investigate Real-World Malicious Links & Phishing Attacks With Threat Intelligence Lookup - Try for Free



