As the latest adaptation of Snow White hits theaters with lukewarm reception, the absence of streaming options on platforms like Disney+ has led many viewers to seek pirated versions online.
This trend is not new; every major movie release without a digital option becomes a prime opportunity for attackers to exploit users eager to watch from home.
A recent campaign identified by Veriti’s research team highlights this risk, involving a sophisticated malware distributed via torrent sites.
Veriti researchers found that a blog post on the website “TeamEsteem” offered a download link for a pirated Snow White (2025) version.
However, this post was malicious, redirecting users to a torrent containing an infected file package. The attackers likely exploited an XSS vulnerability or used leaked admin credentials to access the site.
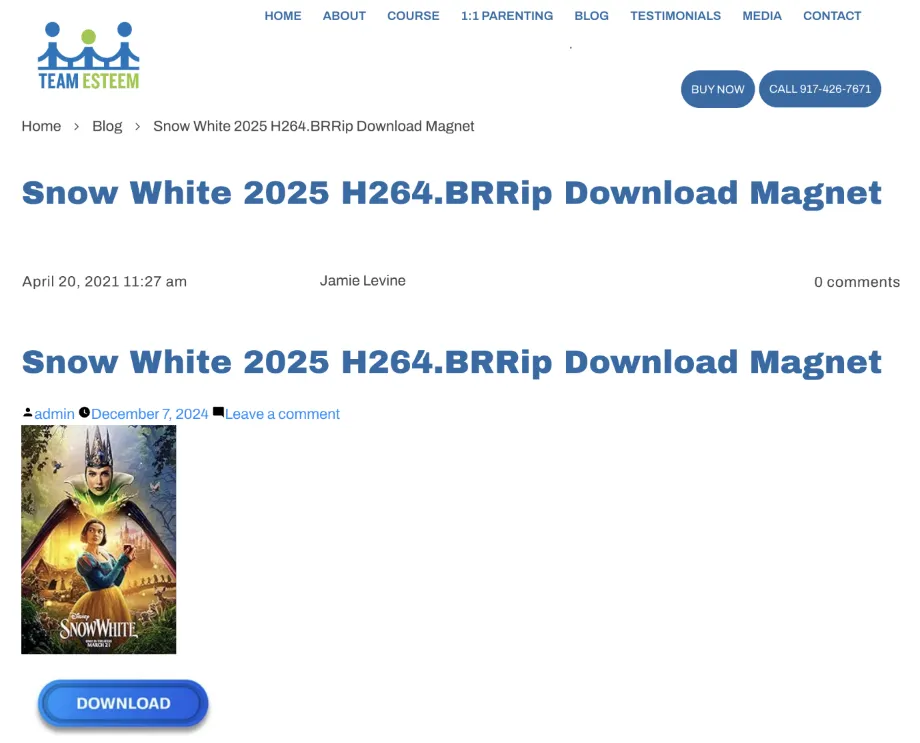
This blog entry redirected users to download a torrent containing a three-file package, which included a malicious executable posing as a necessary codec installer.
Analysis of the Malware
Upon examining the torrent, Veriti analysts discovered a suspicious file named xmph_codec.exe, claiming to be a required video codec.
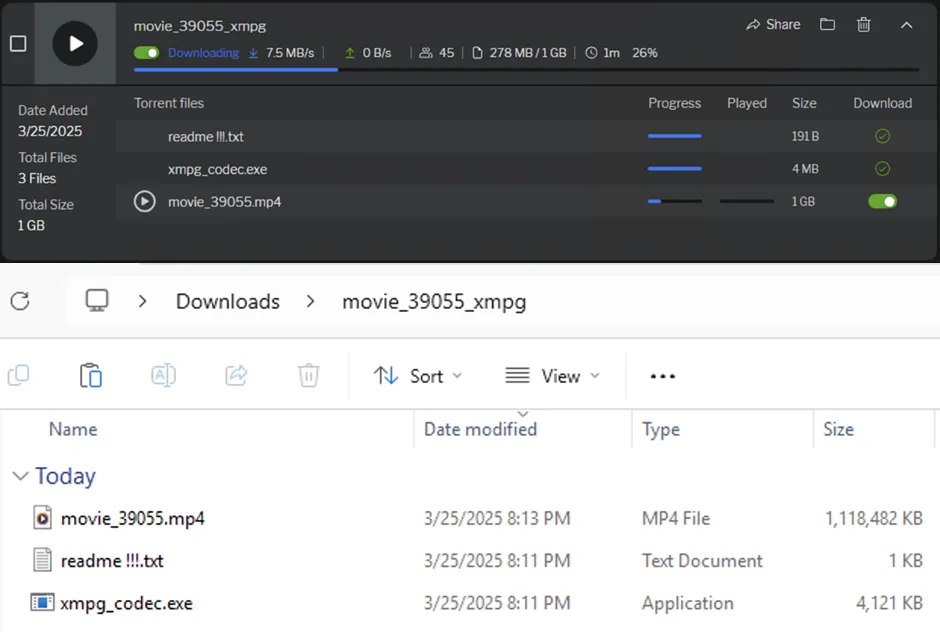
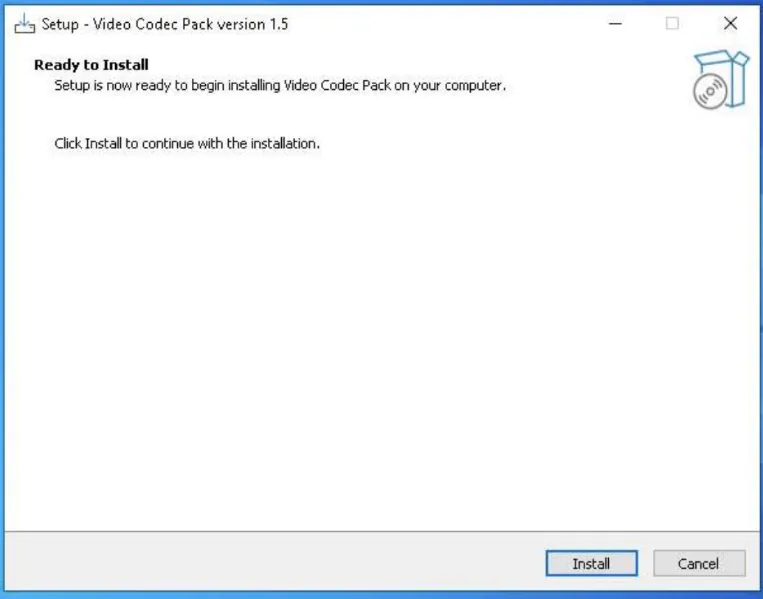
The file triggered a sophisticated malware deployment process when run. Key findings include:
- Detection: Identified as malicious by 50 out of 73 security vendors on VirusTotal.
- Compilation: Compiled on July 12, 2024, suggesting reuse from prior campaigns.
- Unsigned Executable: Raises red flags about its origin.
- Malicious Actions: Drops additional malicious files, silently installs the TOR browser, initiates communication with a Dark Web .onion domain, and disables Windows Defender and other security features.
The malware communicates with a C2 server on the Onion network:
- http://cgky6bn6ux5wvlybtmm3z255igt52ljml2ngnc5qp3cnw5jlglamisad.onion
- http://cgky6bn6ux5wvlybtmm3z255igt52ljml2ngnc5qp3cnw5jlglamisad.onion/route.php
This campaign leverages the anonymous nature of the TOR network to mask communications and evade detection.
The absence of digital streaming options for major movies like Snow White continues to drive users to illegal downloads, creating an ideal environment for attackers.
Users are advised to be cautious when seeking digital content online and to use reputable streaming services to avoid falling prey to such sophisticated malware campaigns.
This not only protects their devices but also supports legal content creators. As cybersecurity continues to evolve, staying informed about these tactics is crucial for maintaining digital safety.
Indicators of Compromise (IoCs)
- File hashes:
- 9c1a0608bae991af50096acaec9d979df9f9a3bb6e89d9d20972d6cfeb9582bb
- 2ec555c34f0af1514501ca5e4d999c843d5b9de7973467820fcf6034a517c4cc
- 8b81b0017c0e154c1fdea226f1ad0d3cfc0e301af05698bdbb7d0d6037d71a12
Are you from SOC/DFIR Teams? – Analyse Malware, Phishing Incidents & get live Access with ANY.RUN -> Start Now for Free.



.png
)
