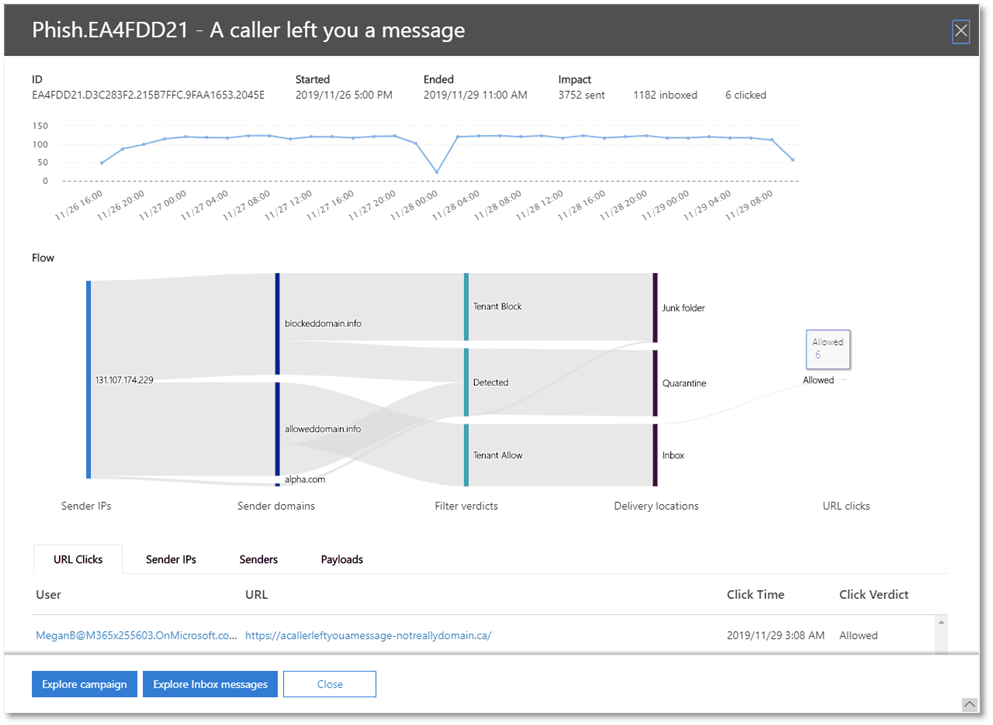
Microsoft announced the public preview of the campaign views security feature that let users view the full campaign of how the attackers targeted the organization and its users. The campaign’s view is the new feature in Office 365 Advanced Threat Protection.
This new feature allows security teams to spot the vulnerable surface, vulnerable users, harvest attacker intelligence and to take remediation steps, Microsoft said.
Campaign Views
The feature displays the data like when the campaign started/ended, impact, the user clicks, sender IP, senders and the payloads embedded. It also highlights the email flow from sender IPs to the delivery location.
Microsoft tested the feature in early previews with some of their customers and the result is extremely positive.
Following are some important features
- Provides campaign summary including a timeline and the users affected.
- List of IP address used to launch an attack
- Messages that blocked, ZAPped, delivered to junk or quarantine or allowed into the inbox
- Domain names used in the attack
- To see how many users clicked on the phishing link
“One large customer we’ve worked with was able to identify multiple configuration flaws in their tenant, by using campaign views for just a short duration of time,” Microsoft said.
The Email accounts are the tempting targets for hackers, cyberattacks are initiated over an email. Attackers follow innovative and sophisticated methods to trick the users in opening the malicious emails.
“It’s worthwhile to think about how attackers target organizations and users. It’s important to remember that attackers are often after financial gain.”
Microsoft Office 365 comes with several security tools that help security teams more comprehensively, effectively investigate, remediate issues and to stop potential breaches.

Now the campaign views are available only the following plans Office 365 Advanced Threat Protection Plan 2, Office 365 E5, Microsoft 365 E5 Security and Microsoft 365 E5.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and hacking news updates.


.png
)
