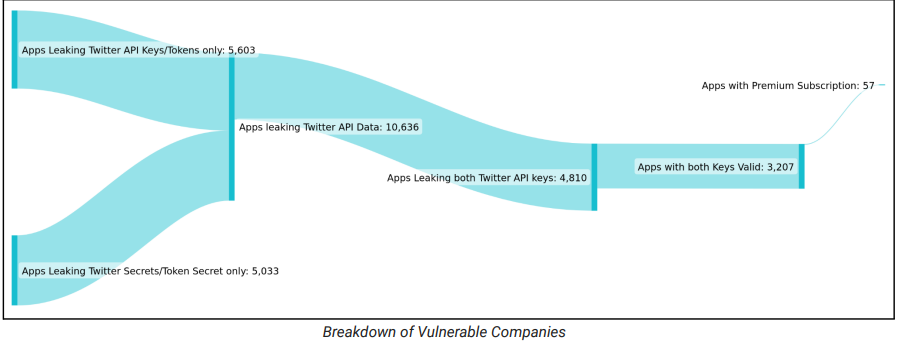
Cybersecurity Company CloudSEK examined a broad range of apps for possible data leaks and discovered 3,207 apps leaking Twitter API keys, that can be utilized to gain access to or to take over Twitter accounts.
The report says 230 apps, some of which are unicorns, were leaking all 4 Auth Creds and can be used to completely take over their Twitter Accounts to carry out critical actions that include the following:
- Read Direct Messages
- Retweet
- Like
- Delete
- Remove followers
- Follow any account
- Get account settings
- Change display picture
How Does Twitter API Work?
Generally, an application programming interface (API) is a way for two or more computer programs to communicate with each other. It is a type of software interface, that offers a service to other pieces of software.
The Twitter API is a set of programmatic endpoints that can be used to understand or build the conversation on Twitter. This API allows finding and retrieving, engaging with, or creating a variety of different resources like Tweets, Users, Spaces, Direct Messages, Lists, Trends, Media, and Places.
The Twitter API provides direct access to a Twitter account. Sending passwords with each request to the API is not an efficient and secure method.
Therefore, OAuth tokens are used by the Twitter API. OAuth (“Open Authorization”) is an open standard for access delegation, commonly used as a means to grant API access without using the password each time. This standard is also used by Amazon, Google, Facebook, and Microsoft
Building a Twitter Bot Army
Usually, while developing a mobile application, developers use the Twitter API for testing. At that time, they save the credentials within the mobile application at locations such as:
- resources/res/values/strings.xml
- source/resources/res/values-es-rAR/strings.xml
- source/resources/res/values-es-rCO/strings.xml
- source/sources/com/app-name/BuildConfig.java
These credentials are not removed before deploying them in the production environment occasionally. Once the app gets uploaded to the play store, the API secrets are there for anyone to access.
Finally, a threat actor can merely download the app and decompile it to get the API credentials. Thus, from here bulk API keys and tokens can be harvested to prepare the Twitter bot army.
According to CloudSEK, threat actors would use these exposed tokens to create a Twitter army of verified (reliable) accounts with large numbers of followers to promote fake news, malware campaigns, cryptocurrency scams, etc.
CloudSEK says the impacted applications include, apps between 50,000 and 5,000,000 downloads, including city transportation companions, radio tuners, book readers, event loggers, newspapers, e-banking apps, cycling GPS apps, and more.
How to Protect Against the Attacks?
- Standardizing Review Procedures: Make sure accurate versioning
- Hiding Keys: Variables in an environment are alternate means to refer to keys and disguise them
- Rotate API keys: Rotating keys can help reduce the threat posed by leaked keys
Therefore, it is essential for organizations to secure their social media data and prevent their verified handles from being used to spread misinformation.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and hacking news updates.



