Researchers uncovered a new malware variant of AgentTesla used by threat actors to steal WiFi Password and data from different applications such as browsers, FTP clients, and file downloaders.
AgentTesla initially observed in 2014, Since then the malware frequently used by various threat actor groups, and performed multiple cyber-attacks around the globe.
We have reported the AgentTesla Activities last year while it was attempted to steal the username-password and log keystroke from various Windows applications.
Attackers using the different modules in this campaign, one of the modules has the capability of stealing Wi-Fi passwords.
Recent activities of the malware observed during March and April 2020, and the actors using the malspam campaigns as a medium and distribute malware in various formats such as ZIP, CAB, MSI, IMG files, and Office documents.
AgentTesla Infection Process
AgentTesla info stealer written in .Net, and the researchers saw its activities in wide that collect the information about the victim’s WiFi profile and possibly spread into other machines.
Attack distributed the embedded executable Variant as an encrypted image resource named (ReZer0V2) that can extract and execute one of the victim’s machine in the run time.

Attackers added anti-debugging, anti-sandboxing, and anti-virtualization checks before executing the variant in the victim’s machine. Once it performed all the checks, it executable decrypts and injects the content.

Later it drops the second payload (owEKjMRYkIfjPazjphIDdRoPePVNoulgd) which is heavily obfuscated and it is the main component that responsible for stealing credentials from browsers, FTP clients, wireless profiles, and more.
The malware creates a new “netsh” process bypassing “wlan show profile” as an argument to collect the WiFi profile credentials and extract the WiFi profiles using a Regular expression “All User Profile * : (?<profile>.*)”.
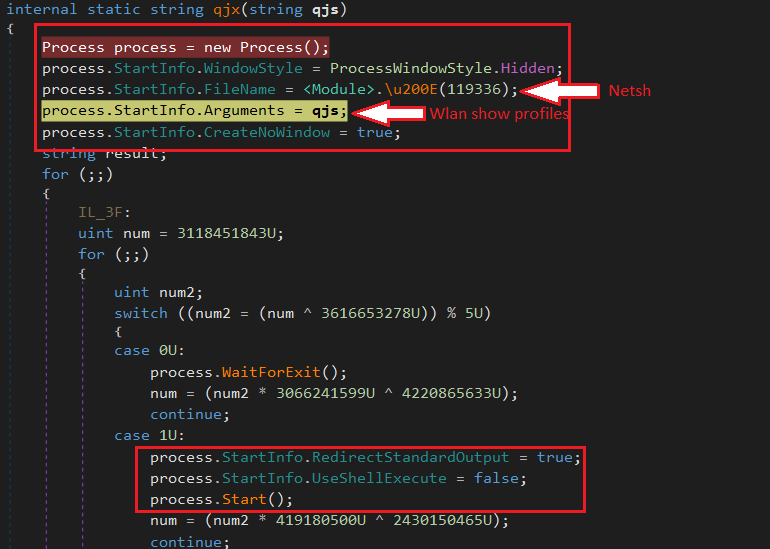
Later attackers extract the WiFi password in plan text by applying the “netsh wlan show profile PRPFILENAME key=clear”.
According to the Malwarebytes report, All the strings used by the malware are encrypted and are decrypted by Rijndael symmetric encryption algorithm in the “<Module>.\u200E” function. This function receives a number as an input and generates three-byte arrays containing input to be decrypted, key and IV.
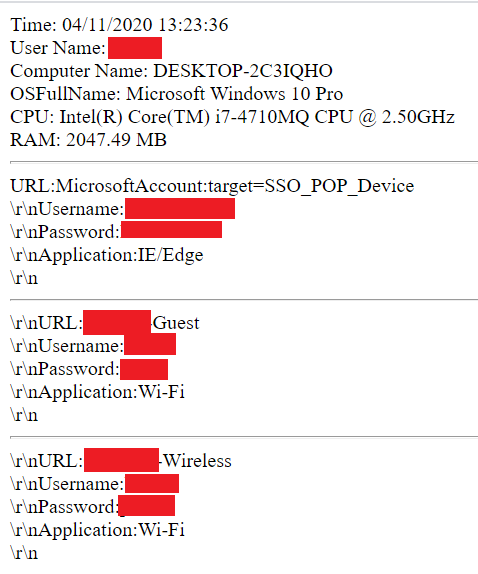
In addition to that, AgentTesla collecting the system information including FTP clients, browsers, file downloaders, and machine info (username, computer name, OS name, CPU architecture, RAM) and send them into the attackers via C2 server.
AgentTesla has some of the other capabilities in the previous variants including Logs keystrokes and is listed in the top 10 most wanted malware families in 2020.
Researchers also belives that the actors expact the operation of AgentTesla since they have added this WiFi stealing feature.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity updates.
Indicators of compromise
AgentTesla samples:
91b711812867b39537a2cd81bb1ab10315ac321a1c68e316bf4fa84badbc09b dd4a43b0b8a68db65b00fad99519539e2a05a3892f03b869d58ee15fdf5aa044 27939b70928b285655c863fa26efded96bface9db46f35ba39d2a1295424c07b
First payload: 249a503263717051d62a6d65a5040cf408517dd22f9021e5f8978a819b18063b
Second payload: 63393b114ebe2e18d888d982c5ee11563a193d9da3083d84a611384bc748b1b0



.png
)
