The North Korean state-sponsored group known as Kimsuky has launched a sophisticated cyber-espionage campaign targeting a prominent weapons manufacturer in Western Europe.
This attack released on LinkedIn, discovered on May 16, 2024, underscores the growing threat state-sponsored cyber actors pose to critical defense infrastructure worldwide.
- New Espionage Tools: The Kimsuky group employed novel espionage tools in this campaign, showcasing their evolving capabilities.
- Primary Target: The main target of this attack was a Western European weapons manufacturer, highlighting the strategic importance of the defense sector.
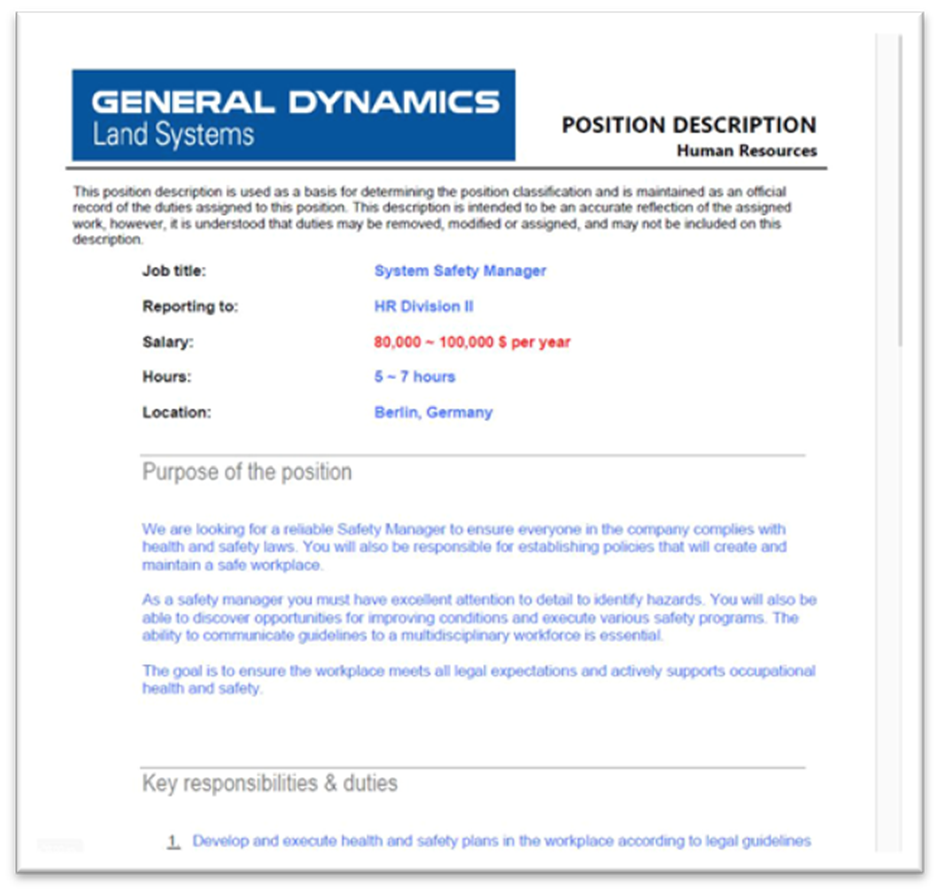
- Deceptive Lure: The attackers, a well-known military contractor, used the “General Dynamics” brand as a visual lure to deceive their targets.
Attack Vector
The attack began with a spear-phishing email sent to employees of the targeted organization.
Analyze any MaliciousURL, Files & Emails & Configuration With ANY RUN : Start your Analysis
The email contained a malicious JavaScript file attachment named “Safety Manager JD (General Dynamics HR Division II).jse.”
This filename was designed to appear as a legitimate job description document from General Dynamics.
Execution Flow
Upon opening the malicious file, the JavaScript code decoded two base64 data blocks.
The first block displayed a benign PDF file as a decoy, while the second block contained the malicious payload, executed silently in the background.
The decoy PDF described an open position for a system security manager, further adding to the deception.
The malicious file executed two files on the system: A legitimate PDF to distract the user and an executable library containing the espionage tool.
The executable library, encoded with double base64, included functions for remote execution by the attacker.
This tool was designed to evade detection by encrypting many strings and API function names decrypted at runtime.

To ensure persistence, the program created a new service called “CacheDB” with the start=auto parameter and inscribed itself in the system registry key, ensuring it launched every time it rebooted.
The program used a unique identifier to communicate with the command and control (C2) server, employing a User-Agent string that mimicked a legitimate browser.
Espionage Tool Capabilities
The espionage tool provided the attacker with several capabilities, including:
- Enumerating directories and files and exfiltrating information to the C2 server.
- Retrieving the full path of running processes.
- Capturing and exfiltrating screenshots.
- Establishing socket connections to specified IP addresses.
- Executing additional processes and downloading secondary payloads.
- Entering a sleep mode for one hour.
- Removing itself from the compromised system, including cleaning up registry entries.
Network Infrastructure
The C2 infrastructure initially called back to hxxp://download.uberlingen[.]com/index.php, resolving to 94.131.120[.]80.
This IP address was associated with multiple domains using illegitimate government naming schemes and was hosted on Stark Industries’ infrastructure.
Another IP address, 103.113.70[.]148, shared similar properties, further linking the infrastructure to Kimsuky.
Research into the network infrastructure revealed significant overlap with known Kimsuky operations, leading to a high-confidence assessment that Kimsuky is behind this campaign.
This attack is part of a broader pattern of North Korean state-sponsored cyber activities targeting the defense sector.
The attack on the Western European weapons manufacturer highlights the escalating risks and potential geopolitical implications of cyber warfare targeting essential military industries.
As the targeted manufacturer plays a crucial role in the defense supply chain, this incident underscores the need for heightened cybersecurity measures in the defense sector.
The Kimsuky group is expected to continue targeting military and aerospace-related entities worldwide, necessitating ongoing vigilance and monitoring.
Indicators of Compromise (IoCs)
The following IoCs were identified in the campaign:
- SHA-256: 24A42A912C6AD98AB3910CB1E031EDBDF9ED6F452371D5696006C9CF24319147
- MD5: 8346D90508B5D41D151B7098C7A3E868
- Network Indicators: hxxp://download.uberlingen[.]com/index[.]PHP
Looking for Full Data Breach Protection? Try Cynet's All-in-One Cybersecurity Platform for MSPs: Try Free Demo
%20(1).webp?w=696&resize=696,0&ssl=1)


.png
)
