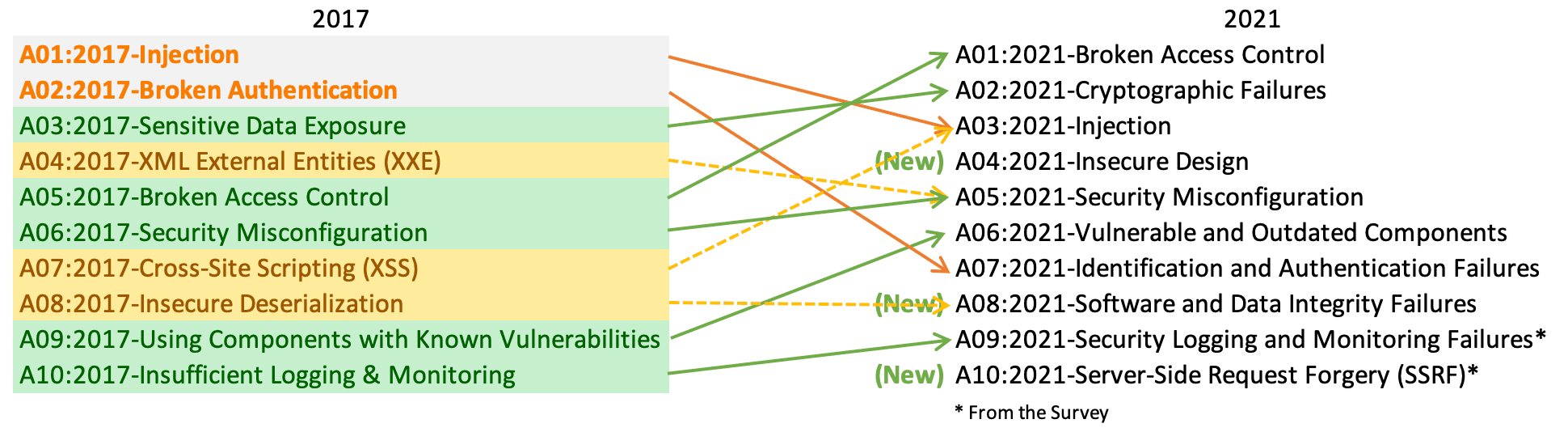
OWASP released a draft for 2021, the all-new OWASP Top 10 2021 comes with three new categories and position changes.
The OWASP Top 10 is a minimal or a basic security testing requirement for every web application.
The OWASP Top 10 was first introduced in 2003, and for there it took many revisions, now the draft report for 2021 is available now.
OWASP said that “the OWASP Top 10 2021 is a good start as a baseline for checklists and so on, but it’s not in itself sufficient”.
OWASP Top 10 2021
A01:2021 – Broken Access Control
Moves to the top from the fifth position in 2017, it is also called an authorization that defines how a web application grants access to content and functions to some users and not others.
A02:2021 – Cryptographic Failures
Shifted from third to the second position, previously it was called as Sensitive Data Exposure. The lack of encryption often leads to sensitive data exposure or system compromise.
A03:2021-Injection
Moves down to the third position from No.1, it is a technique in which the attacker takes non-validated input vulnerabilities and injects SQL commands through a web application that are executed in the backend database.
A04:2021 – Insecure Design
This is a new category with the OWASP Top 2021, it focuses on the risks related to design and architectural flaws.
“Insecure design is a broad category representing many different weaknesses, expressed as missing or ineffective control design”.
A05:2021 – Security Misconfiguration
Moved from 6th to fifth position, it focuses on the security hardening across the application stack or improperly configured permissions on cloud services.
A06:2021 – Vulnerable and Outdated Components
It was moved from the second position to six, as not enough attack data is available, this category focuses on the vulnerable versions of all components used on both client-side and server-side.
A07:2021 – Identification and Authentication Failures
Previously it was known as Broken Authentication, this category focuses on authentication failures.
It leads to automated attacks such as credential stuffing in which attackers use a list of usernames and passwords.
A08:2021 – Software and Data Integrity Failures
This is a new category introduced on OWASP Top 10 2021, it focuses on software and data integrity failures relate to code and infrastructure that do not protect against integrity violations.
A09:2021 – Security Logging and Monitoring Failures
Moves one step from the tenth position, this category helps to detect, escalate, and respond to active breaches.
A10:2021 – Server-Side Request Forgery (SSRF)
This category focuses on securing a connection that a web application is fetching a remote resource without validating the user-supplied URL.
Please follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and hacking news updates.



