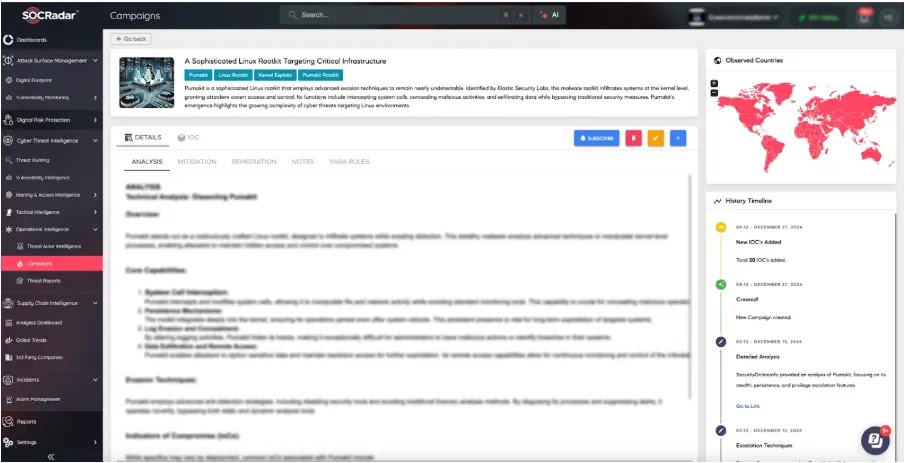
Pumakit is a sophisticated rootkit that leverages system call interception to manipulate file and network activity. It ensures persistence through kernel-level embedding that allows for continued operation after reboots.
By tampering with logs and employing anti-detection techniques that include disabling security tools, it hinders forensic investigations and maintains stealthy operations.
This rootkit facilitates data exfiltration by providing remote access to attackers and enabling continued exploitation of compromised systems.
Anomalous system activity was detected that is potentially indicating a compromise and includes unusual kernel-level modules, modifications to system call handlers, and hidden processes or network connections.
Investigate Real-World Malicious Links & Phishing Attacks With Threat Intelligence Lookup - Try for Free
The investigation should focus on the suspicious IP address 89.23.113.204 domains like rhel.opsecurity1.art and files with specific hashes like 4375998ea157a8a21e1ead13052bad8a and 810f4b422b9c0a6718e9461de3a2edda.
.webp)
To mitigate the Pumakit campaign’s techniques, employ robust application control to block malicious libraries and payloads used in Dynamic Linker Hijacking. Implement behavior-based endpoint detection to identify and prevent process injection activities.
Enforce Multi-Factor Authentication (MFA) for default accounts to enhance account security. Restrict file and registry permissions to prevent tampering with security tools and configurations, thereby maintaining the integrity of your defense mechanisms.
To effectively mitigate Pumakit-like threats, organizations must proactively harden systems by applying regular patches and updates. They should also implement strict access controls, limiting administrative access, and enforcing strong account policies.
Organizations must establish and regularly test robust incident response plans to effectively handle rootkit infections and system compromises that ensure a swift and coordinated response to minimize the impact of these threats.
According to SOC Radar, the YARA rule targets a Linux Trojan named Linux.Trojan.Pumakit that aims to identify malicious files associated with the Trojan on systems with x86 or arm64 architecture.
It searches for a combination of strings that include references to PUMA, Kitsune, specific file paths like /usr/share/zov_f, suspicious filenames like .puma-config, and configuration options related to ping intervals, session timeouts, and C2 communication.
A potential presence of malware can be identified by the rule if it finds at least four of these strings within a file or memory.
Through the utilization of stealthy kernel-level techniques, Pumakit can compromise critical infrastructure and bypass conventional security measures.
By utilizing the proactive approach, organizations are given the ability to effectively defend themselves against Pumakit and other threats of a similar nature, thereby reducing the impact that potential cyberattacks could have on essential operations.
Integrating Application Security into Your CI/CD Workflows Using Jenkins & Jira -> Free Webinar



.png
)
