A new menace has emerged targeting unsuspecting Facebook Messenger users.
Dubbed the “Python Infostealer,” this malicious software is designed to pilfer credentials through sophisticated means, leveraging popular platforms like GitHub and GitLab for its nefarious purposes.
Stealthy Approach of Python Infostealer
The abuse of legitimate sites is at the heart of the Python Infostealer’s strategy.
Are you from SOC and DFIR teams? – Join With 400,000 independent Researchers
Malware analysis can be fast and simple. Just let us show you the way to:
- Interact with malware safely
- Set up virtual machine in Linux and all Windows OS versions
- Work in a team
- Get detailed reports with maximum data If you want to test all these features now with completely free access to the sandbox: ..
Threat actors exploit the trust users place in reputable public repositories and messaging applications, using them as part of their Command and Control (C2) infrastructure.
This makes maliciously using web-based repositories like GitHub and GitLab particularly insidious, as it can be challenging to detect.

The infection begins with a seemingly innocuous Facebook Messenger message, enticing victims to download archived files.
These files kickstart a two-stage infection process, deploying one of the Python Infostealer’s three variants, each with its unique characteristics and methods of operation.
Cybereason Security Services’ latest Threat Analysis Report illuminates this alarming development and offers insights and recommendations for safeguarding against this digital predator.
A Trio of Threats
The Python Infostealer comes in three variants, showcasing the adaptability and cunning of its creators.
The first two variants are regular Python scripts, while the third morphs into an executable assembled by PyInstaller for broader reach and impact.
Despite their differences, all variants share a common goal to harvest and exfiltrate user credentials to platforms like Discord, GitHub, and Telegram.
| Variant One | Variant Two | Variant Three | |
| GET request to ipinfo[.]io to identify geolocation of the victim. |  | ||
| Bundled by PyInstaller |  | ||
| Does not depend on Python packages to be installed locally |  |  |  |
| Deploy files to subdirectory of C:\Users\Public |  |  | |
| Obfuscation of function and variable name |  |  | |
| Obfuscation via data compression |  | ||
| Persistence via Startup Folder |  |  |  |
| Staged payloads |  |  | |
| Targets Brave |  | ||
| Targets Coc Coc Browser |  |  |  |
| Targets Chromium |  | ||
| Targets Facebook Cookies |  |  |  |
| Targets Google Chrome Browser |  |  |  |
| Targets Microsoft Edge |  |  |  |
| Targets Mozilla Firefox |  | ||
| Targets Opera Web Browser |  |
A particularly alarming aspect of the Python Infostealer’s operation is its use of legitimate platforms to transmit stolen credentials.
By exploiting the Telegram Bot API and other messaging applications, the malware sends harvested data to threat actors, making detection and prevention more challenging for security teams.
Recommendations for Protection
Cybereason recommends several proactive measures to combat the Python Infostealer.
These include enabling Application Control to block malicious files, activating Fileless Protection, and educating users on the dangers of downloading files from untrusted sources, especially on social media platforms.
Based on language clues in the malware’s code and naming conventions, analysis suggests that the developers or affiliates of the Python Infostealer may be Vietnamese-speaking individuals.
This insight not only aids in understanding the threat’s origins but also underscores the global nature of cybersecurity challenges.
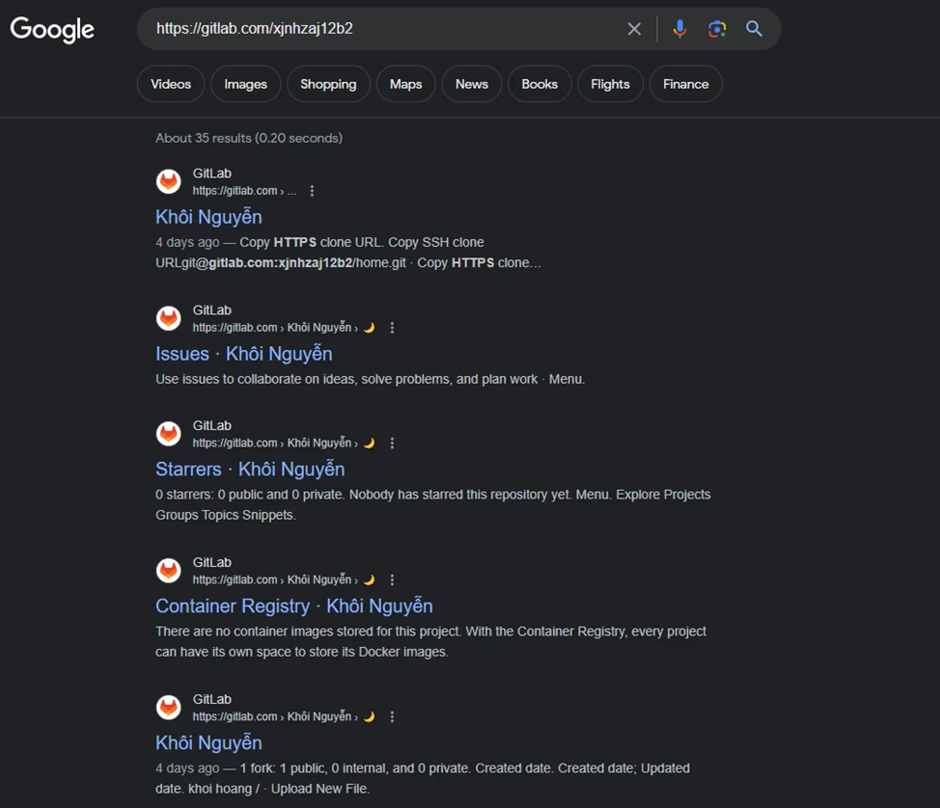
Some of the names of repositories and accounts on GitHub and GitLab are written in Vietnamese.
One of the aliases for the GitLab account was Khoi Nguyen, a popular Vietnamese name and a common alias in the community.
The emergence of the Python Infostealer as a threat to Facebook Messenger users highlights the evolving landscape of cyber threats.
These digital predators pose a real and present danger by leveraging legitimate platforms and employing sophisticated tactics.
Vigilance, education, and robust security measures are paramount in protecting against such insidious attacks.
You can block malware, including Trojans, ransomware, spyware, rootkits, worms, and zero-day exploits, with Perimeter81 malware protection. All are incredibly harmful, can wreak havoc, and damage your network.
Stay updated on Cybersecurity news, Whitepapers, and Infographics. Follow us on LinkedIn & Twitter.
.webp?w=696&resize=696,0&ssl=1)


.png
)
