Security Onion, a widely used open-source platform for network security monitoring, has recently released Security Onion 2.4.140.
This latest update focuses on enhancing key components such as Suricata and Zeek, offering improved security and functionality to its users.
Below is a breakdown of what’s new and how this release impacts security teams worldwide.
Key Component Updates
- Version Overview:
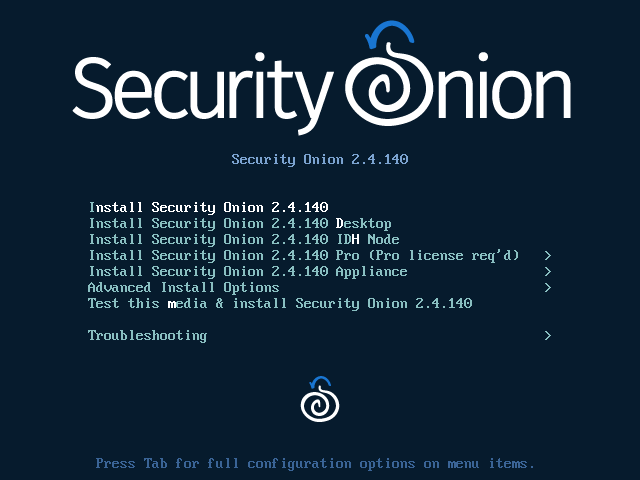
- Security Onion 2.4.140 has been released.
- It includes updates to Suricata and Zeek.
- Component Updates:
- Suricata 7.0.9: This update includes security fixes to enhance protection against emerging threats.
- Zeek 7.0.6: Contains bug fixes to improve stability and performance.
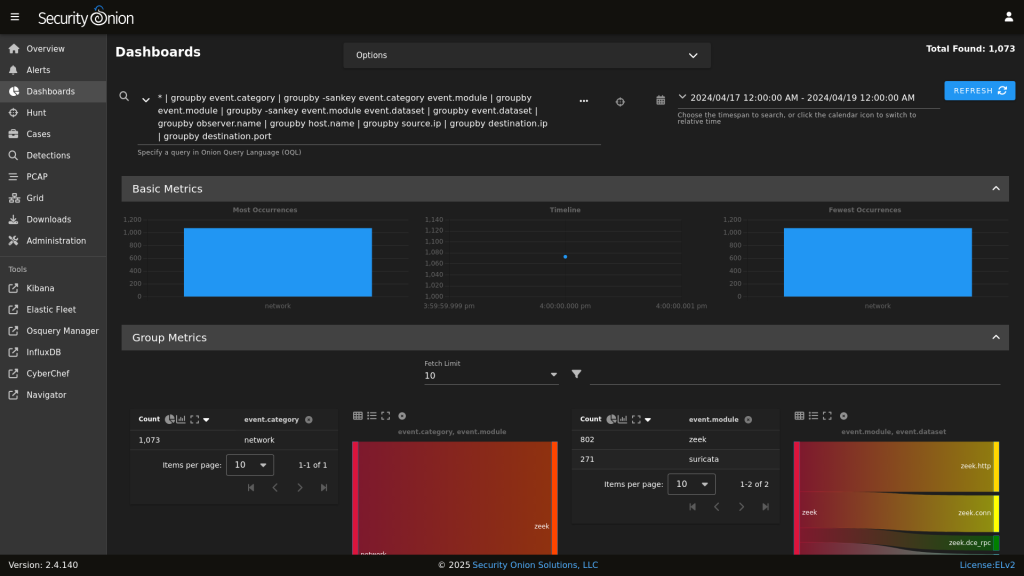
- SOC Config Improvements:
- Users can now move certain configuration entries (e.g., SOC Dashboard queries, SOC Hunt queries, SOC Actions) up or down.
- This feature enhances usability and workflow efficiency.
- Release Details:
- For a complete list of changes, refer to the Release Notes at Security Onion documentation.
- Known issues are also documented for troubleshooting and planning.
- About Security Onion:
- It is a free, open-source platform for network security monitoring.
- Offers network visibility, host visibility, intrusion detection honeypots, log management, and case management.
- Used by over 2 million downloads and trusted globally by security teams.
- Platform Capabilities:
- Network Visibility: Includes signature-based detection via Suricata, rich protocol metadata, file extraction (using Zeek or Suricata), full packet capture, and file analysis.
- Host Visibility: Uses the Elastic Agent for data collection, live queries via osquery, and centralized management with Elastic Fleet.
- Intrusion Detection Honeypots: Supports OpenCanary for enhanced enterprise visibility.
- Log Management: Integrates logs into Elasticsearch with custom interfaces for alerts, dashboards, threat hunting, case management, and grid management.
- Installation Guidance:
- New Installations: Recommended to start with an IMPORT installation for ease of setup, then move to more advanced configurations.
- Existing Installations: Update using the soup utility. It’s recommended to test updates on a test environment before applying them to production.
- Documentation and Feedback:
- Documentation is available online and is regularly updated.
- Users are encouraged to provide feedback on documentation for continuous improvement.
Security Onion 2.4.140 emphasizes critical security updates and usability enhancements, reinforcing its position as a go-to tool for security professionals seeking robust network monitoring and management capabilities.
As the security landscape continues to evolve, platforms like Security Onion play a vital role in equipping defenders with the tools they need.
Investigate Real-World Malicious Links & Phishing Attacks With Threat Intelligence Lookup - Try for Free



.png
)
