A hacker group dubbed Shiny Hunters started selling hacked databases that contain over 73.2 Million user records of 11 different companies over the dark web.
It all starts with the Tokopedia dump shared last week contains more than 90 million user records, followed by Unacademy dump and the hack of the Microsoft’s GitHub account.
It seems ‘SkyHunter’ has got some interesting business model going in the darkweb market – the actor gained initial traction via Tokopedia breach and seems to be flooding the market with new bases,” reads Cyble report.
Hackers Selling Passwords
Now the hacker group started selling passwords on the dark web that exfiltrated from various companies.
At the first stage following companies data are listed for sale; HomeChef, ChatBooks, and Chronicle.com
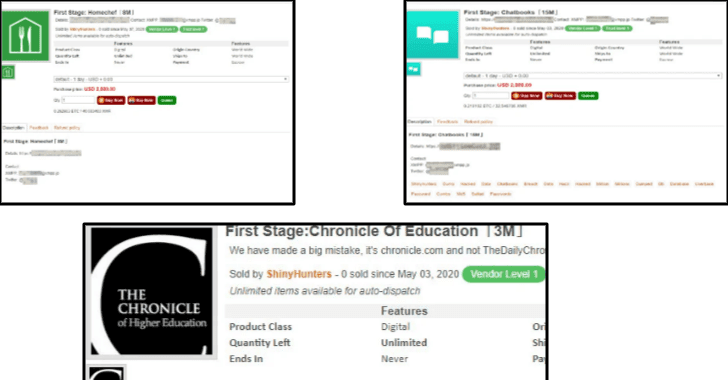
Among three the chronicle education data prices are lower when compared to others, the dump has more than 3M details, and the quoted price $1500.
The hackers said “that they have more databases from other breached websites. They plan on selling them in the near future.”
Shared list of user records and pricing details.
| Company | User Records | Price |
| Tokopedia | 91 million | $5,000 |
| Homechef | 8 million | $2,500 |
| Bhinneka | 1.2 million | $1,200 |
| Minted | 5 million | $2,500 |
| Styleshare | 6 million | $2,700 |
| Ggumim | 2 million | $1,300 |
| Mindful | 2 million | $1,300 |
| StarTribune | 1 million | $1,100 |
| ChatBooks | 15 million | $3,500 |
| The Chronicle Of Higher Education | 3 million | $1,500 |
| Zoosk | 30 million | $500 |
Users are recommended to change the login credentials and to use a unique login for every portal.
Tips to Stay Safe
- Use a complex password, enforce a strong password policy.
- Check the password regularly, Use two-factor authentication(2FA) for vital sites like managing an account and Emails, make sure all the passwords are unique.
- Change the Manufactures’s default Password that gadgets are issued before they are conveyed to the IT Department.
- Use password managers.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and hacking news updates.



.png
)
