A significant vulnerability has been discovered in the Sliver C2 server, a popular open-source cross-platform adversary emulation and red team framework.
This vulnerability, identified as CVE-2025-27090, allows attackers to hijack TCP connections, enabling them to intercept and manipulate traffic.
The exploit leverages a Server-Side Request Forgery (SSRF) technique, which can be particularly damaging as it allows attackers to bypass network defenses and access internal services.
Impact and Affected Versions
The vulnerability affects Sliver C2 server versions from v1.5.26 to v1.5.42 and v1.6.0 prior to commit 0f340a2.
This means that any server installed since September 2022 could be vulnerable.
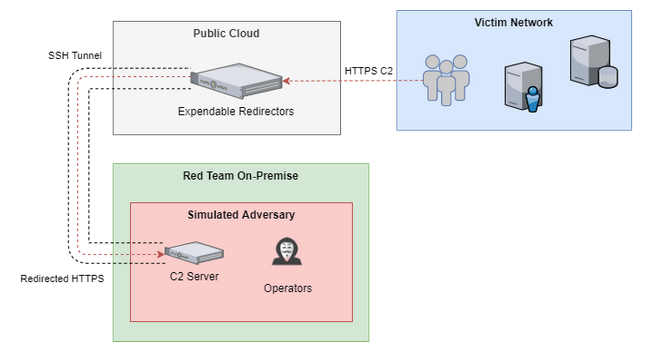
The SSRF exploit can lead to severe consequences, including the exposure of teamserver IPs behind redirectors and lateral movement within the network.
An attacker must have access to a C2 port and either a staging listener or a stager-generated implant binary to exploit this vulnerability.
Exploitation Mechanism
The exploitation process involves spoofing implant traffic to manipulate the teamserver into opening a TCP connection to an arbitrary IP and port.
This is achieved by manipulating the envelope type in the implant traffic, allowing attackers to call specific handler functions.
Key functions targeted include registerSessionHandler and tunnelDataHandler.
By registering a session and creating a reverse tunnel, attackers can establish a connection to any desired endpoint, effectively hijacking TCP traffic.
The tunnelDataHandler function is particularly critical as it allows the creation of a reverse tunnel.
By setting the CreateReverse field to true and specifying the target IP and port, attackers can coerce the teamserver into establishing a connection to an arbitrary endpoint.
According to the research, this connection can then be used to read and write traffic, effectively intercepting and manipulating data.
To mitigate this vulnerability, users are advised to update their Sliver C2 servers to the latest patched version.
The advisory and patched release are available for download, providing a fix for the SSRF vulnerability.
Users should ensure that all affected versions are updated promptly to prevent potential exploitation.
The vulnerability highlights the importance of regular security audits and updates in maintaining the integrity of critical infrastructure tools like Sliver C2.
Free Webinar: Better SOC with Interactive Malware Sandbox for Incident Response, and Threat Hunting - Register Here



.png
)
