A consumer-grade spyware app named pcTattletale has been discovered running on the check-in systems of at least three Wyndham hotels across the United States.
This alarming discovery was made by TechCrunch, which reported that the app stealthily captured screenshots of hotel booking systems, exposing sensitive guest details and customer information.
Due to a security flaw in the spyware, these screenshots were accessible to anyone on the internet, not just the intended users of the spyware.
Sensitive Guest Information Exposed
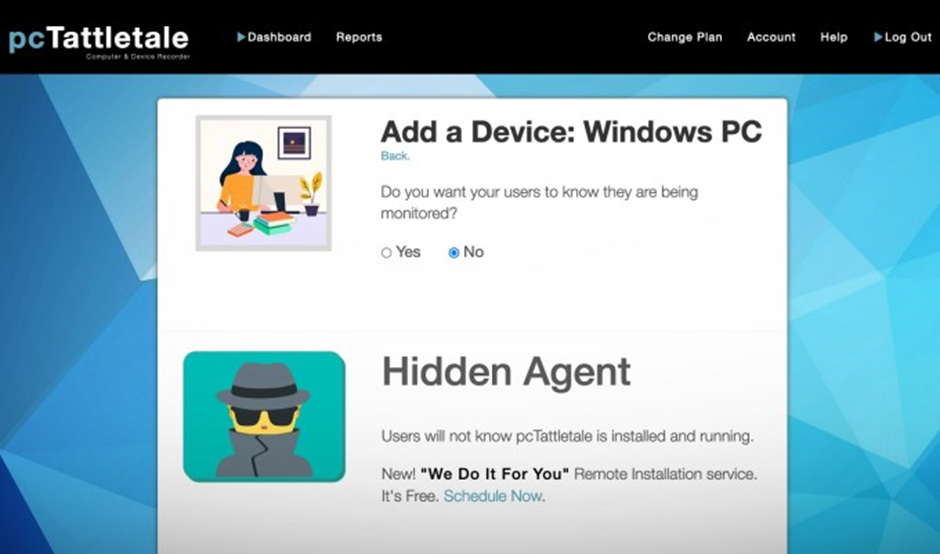
The spyware, pcTattletale, allows remote viewing of the target’s Android or Windows device and its data from anywhere in the world.
ANYRUN malware sandbox’s 8th Birthday Special Offer: Grab 6 Months of Free Service
The app runs invisibly in the background, making it undetectable to the user.
However, a significant bug in the app means that anyone who understands the security flaw can download the screenshots directly from pcTattletale’s servers.
Security researcher Eric Daigle, who discovered the compromised hotel check-in systems, attempted to warn pcTattletale of the issue, but the company has not responded, and the flaw remains unfixed.
Screenshots from two Wyndham hotels revealed the names and reservation details of guests on a web portal provided by travel tech giant Sabre.
Additionally, the screenshots displayed guests’ partial payment card numbers.
Another screenshot showed access to a third Wyndham hotel’s check-in system, logged into Booking.com’s administration portal used to manage guest reservations.
Hotel and Corporate Responses
The discovery has raised serious concerns about the security measures in place at these hotels.
The manager of one affected hotel expressed surprise, stating they were unaware that the spyware was taking screenshots of their check-in computer.
The managers of the other two hotels did not respond to TechCrunch’s calls or emails.
Wyndham spokesperson Rob Myers clarified that Wyndham is a franchise organization, meaning all its U.S. hotels are independently owned and operated.
However, Wyndham did not confirm whether it was aware of pcTattletale’s use on the front-desk computers of its branded hotels or if such use was approved by Wyndham’s policies.Booking.com, whose administration portal was accessed by the spyware, stated that its systems were not compromised.
Angela Cavis, a spokesperson for Booking.com, highlighted that this incident seemed to be an example of how cybercriminals target hotel systems through sophisticated phishing tactics.
These tactics often lead to unauthorized access to hotel accounts and attempts to impersonate the hotel or Booking.com to request customer payments.
This incident is the latest example of consumer-grade spyware exposing sensitive information due to security flaws. pcTattletale, marketed for child and employee monitoring, has also been promoted for use against spouses suspected of infidelity.
The app requires physical access to the target’s device for installation and offers a service to help customers install the spyware on the target’s computer.
Despite the serious implications of this security breach, Bryan Fleming, the founder of pcTattletale, did not respond to TechCrunch’s request for comment.
The exposure of sensitive guest information at these hotels underscores the urgent need for more robust cybersecurity measures and regulatory oversight to protect personal data from unauthorized access and misuse.
As investigations continue, the hospitality industry must reassess its security protocols to prevent such breaches in the future.
Free Webinar on Live API Attack Simulation: Book Your Seat | Start protecting your APIs from hackers
%20(2).webp?w=696&resize=696,0&ssl=1)


.png
)
